Angehefteter Tweet

The #SOCON2026 agenda is live! 🎉
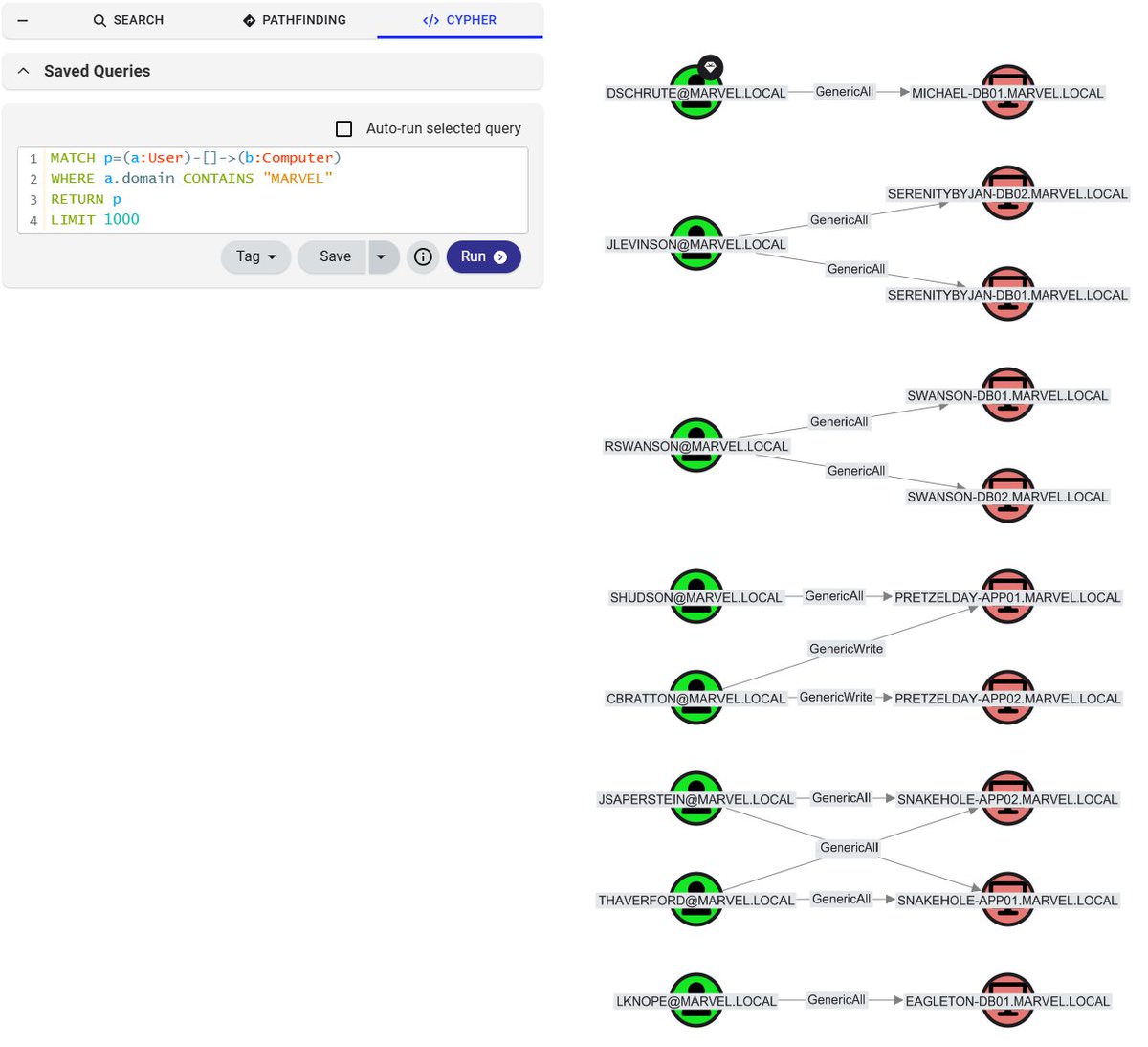
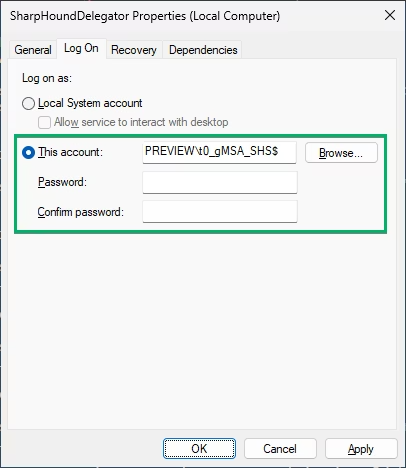
Explore talks, topics, & speakers across the Tradecraft, OpenGraph, & new Practice Track, focused on turning Attack Path Management into an operational discipline.
Check out the agenda & plan your experience: ghst.ly/socon26-tw
🧵: 1/4
English