The Company of Master Mariners of India
70 posts


@CompanyMariners
Maritime




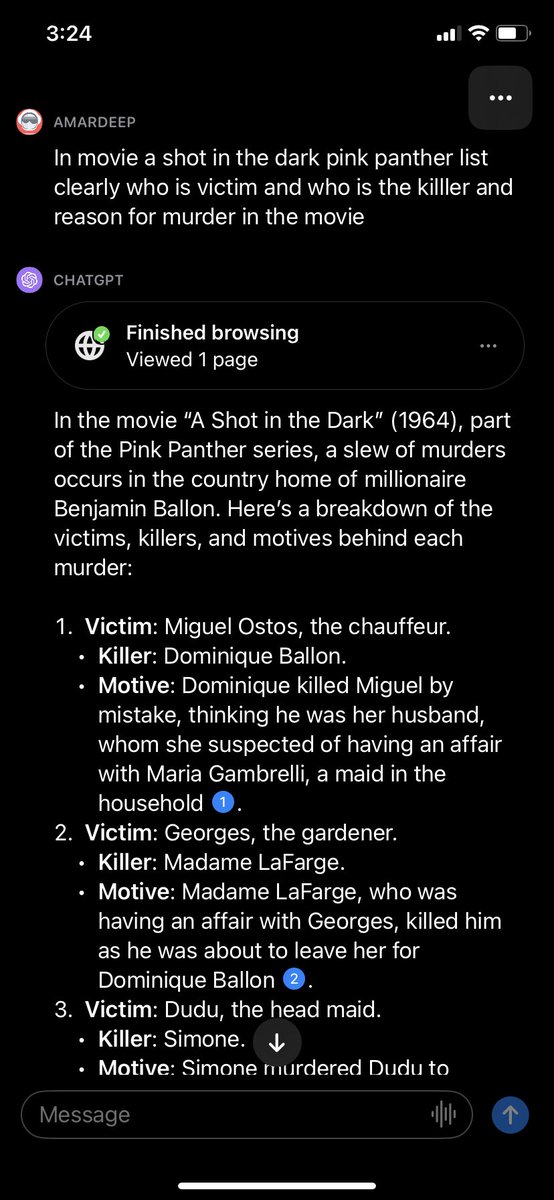
Chandrayaan-3 Mission: Today’s successful firing, needed for a short duration, has put Chandrayaan-3 into an orbit of 153 km x 163 km, as intended. With this, the lunar bound maneuvres are completed. It’s time for preparations as the Propulsion Module and the Lander Module gear up for their separate journeys. Separation of the Lander Module from the Propulsion Module is planned for August 17, 2023.


🛸Saw an epic video by @AbhijitChavda "Did China hack ISRO & crash Chandrayaan-2" 🔗 video link @YouTubeIndia youtu.be/QA7jKEeaoJs 👏Kudos to Indian YouTube community for making great videos. We should encourage and amplify such content. 📚He has mentioned an excellent paper by Maj Gen PK Mallick 🔗 Cyber Attack on Kudankulam Nuclear Power Plant A Wake up call google.com/url?sa=t&sourc… ☣️ Paper deals with potent malware DTrack deployed by North Korean Threat Actors called Group A or Lazarus. The malware is reported to have penetrated the information system Of India's biggest Nuclear Power plant to steal vital information related to plant operation & thorium based fission process. Same malware is said to have attacked ISRO at same time( days before Vikram Lander crashed - Chandrayaan-2), though extent of attack is not confirmed. KNPP attack however has been studied in detail. ☣️The malware has ability to collect information such as files, logs, key strokes, IP address, Mac address & other information regarding system/network architecture . It collects information in a neat, organized manner then proceeds to zip it and transmit the file back to the attacker. The file is transferred from the temp folder to better hidden folders, this enables malware to hide longer to collect more information or deploy other malware for the next stage of attack. Malware didn't penetrate the SCADA system used to control plant, A Malware that controls this system can do physical harm to the plant leading to catastrophic outcome. ☣️ Fascinating Analysis by @issuemakerslab ( a nonprofit cybersecurity expert team out of South Korea)shows that same virus was used to attack multiple critical infrastructure in South Korea & India. Image in their 2019 tweet shows the same/similar password used 🔑 to compress files as in previous incidents in South Korea. Password, Known Strings, Hashes, Hidden File Types, IP address in files linking to executables are few IOC(Indicators of Compromise) used in Threat Hunting & Assesment. 🔗x.com/issuemakerslab… ☣️ Document suggests several mitigation strategies. One Interesting is to switch to a Linux based operating system. DTrack is designed to penetrate the Windows system. @CDAC @cdacindia has developed an OS called BOSS Linux (Bharat Operating System Solution) which boasts 6million(60 lakh) deployment across India. How Linux type OS will prevent malware infection is not clear to me, could be due to better access controls, isolation of process restricting resources and network.