匚ㄚ乃乇尺ㄖᐯ乇尺ㄥㄖ卂ᗪ
733 posts





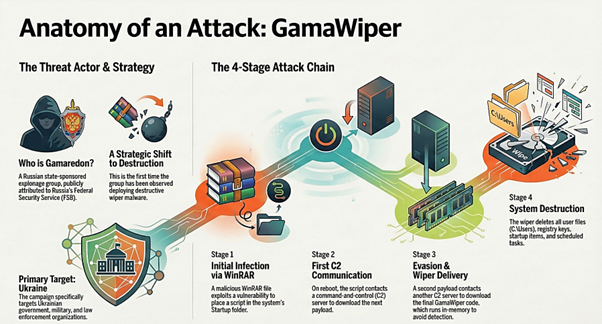
'Dogovor.rar' seen from Ukraine @abuse_ch bazaar.abuse.ch/sample/82e5a4d… CVE-2025-8088, CVE-2025-6218 @500mk500


#APT #Gamaredon #PrimitiveBear #TridentUrsa #UAC0010 🤡 🎯Keep your eyes on this: *.localhost[.]run *.lhr[.]life *.workers[.]dev *.trycloudflare[.]com 🔴IOCs: *.chocolate695.workers[.]dev *.70federal.workers[.]dev *.3022protestant.workers[.]dev *.213rrfgv.workers[.]dev