Dominic Chell 👻
16.1K posts


Dominic Chell 👻
@domchell
Just your friendly neighbourhood red teamer @MDSecLabs | Creator of /r/redteamsec | https://t.co/3k3EBAZqGd | https://t.co/KwO2OwDOkl
Manchester, England Beigetreten Şubat 2009
547 Folgt17.8K Follower
Dominic Chell 👻 retweetet
Dominic Chell 👻 retweetet

In 2025, we achieved pre-auth RCE against another solution in a ransomware gang favourite category. Today, we finally click publish.
Join us as we walk through a chain of vulnerabilities we identified in BMC’s FootPrints ITSM solution.
Enjoy!
labs.watchtowr.com/thanks-itsms-t…
English
Dominic Chell 👻 retweetet

FancyBear Exposed: Major OPSEC Blunder Inside Russian Espionage Ops - Ctrl-Alt-Intel ctrlaltintel.com/threat%20resea…
English
Dominic Chell 👻 retweetet

In 2021 I mined 1.55 ETH into a crypto wallet. When I needed to access it recently my seed phrase didn't work in any standard tool.
Turns out the wallet software (coinwallet) back in 2021 had a bug that gave people the WRONG SEED PHRASE! Anyone who created a wallet during that period can't access it by normal approaches.
After weeks of forensics, I found the bug and recovered my ETH. Posting the full story and recovery code below!
Full story: robmulla.substack.com/p/how-my-sons-…
Repo: github.com/RobMulla/coins…
English

@retBandit Good luck mate - I’m sure you’ll kill the next one too 🙏 hopefully catch up with you for a beer this year 🍻
English

After 13 incredible years at IBM, I’m stepping away to start building something new.
IBM has been a defining part of my life. I’m especially proud to have founded and grown the Adversary Simulation team and to have served as a Distinguished Engineer focused on AI and offensive security. What began as a small idea became one of the greatest red teams, pushing the boundaries of what real-world adversary simulation can look like - made possible by an exceptional group of people I learned from every day.
I’m deeply grateful to the X-Force leadership and to the teammates, mentors, researchers, and operators who made the journey what it was. The team is in great hands and will continue to do important, impactful work.
Looking ahead, I’m excited to focus on building what’s next - continuing to raise the bar for offensive cyber and exploring how AI can enable high sophistication offensive cyber operations and capabilities at a speed, scale, and intensity never before seen. It’s still early, but I’m looking forward to sharing more soon.
I truly appreciate everyone who’s been part of the journey.
English
Dominic Chell 👻 retweetet

It's been a few months since I released a few short "Mythic Developer" videos. Before making more, I'd like to first get your feedback on the current ones. Please take a few min and fill this out so I can make sure you get the best content :)
specterops.typeform.com/MythicDeveloper
GIF
English
Dominic Chell 👻 retweetet

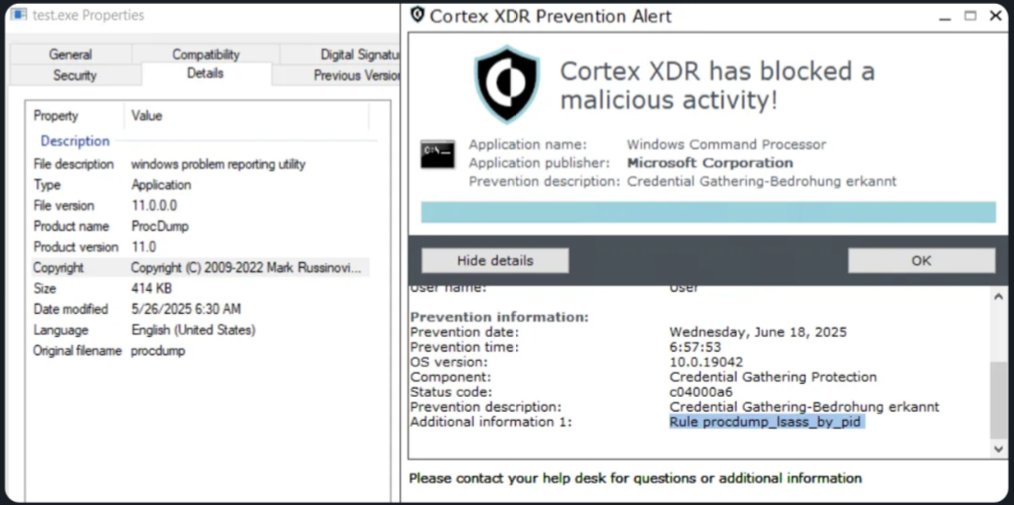
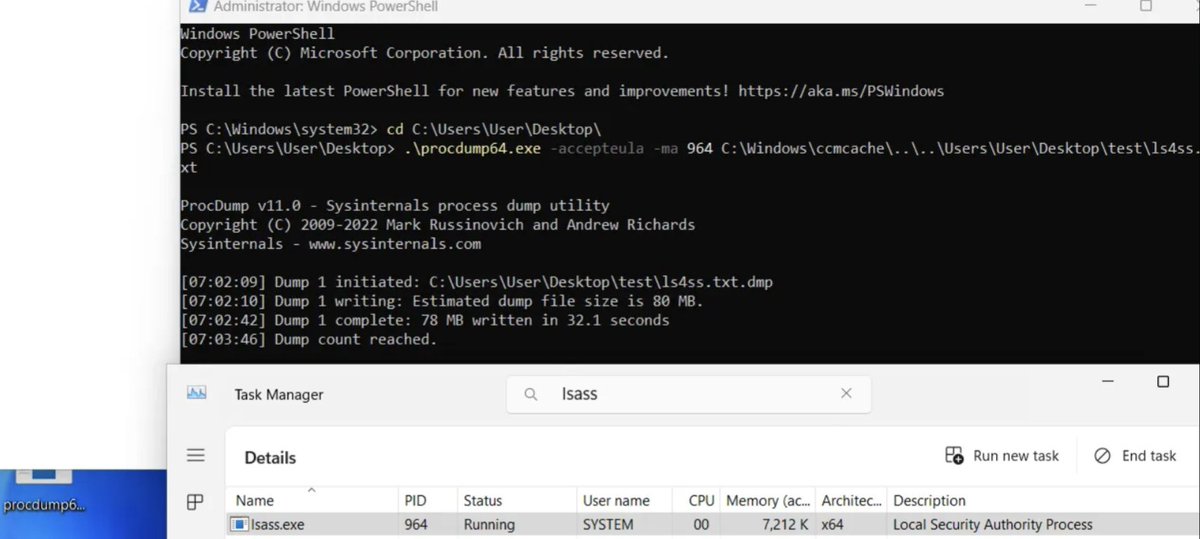
Research shows how Palo Alto Cortex XDR predefined BIOC behavioral rules can be decrypted and analyzed. By understanding rule logic and built-in exceptions, attackers can adapt techniques to evade detection and bypass behavioral protections.
core-jmp.org/2026/03/decryp…


English
Dominic Chell 👻 retweetet

This week’s video covers CVE-2026-24291, a Windows LPE nicknamed RegPwn by the team over at @MDSecLabs. As a part-time sloperator (Google it), I whipped up a quick RegPwn BOF, and in the video I demo it with Mythic and Apollo. Link below.
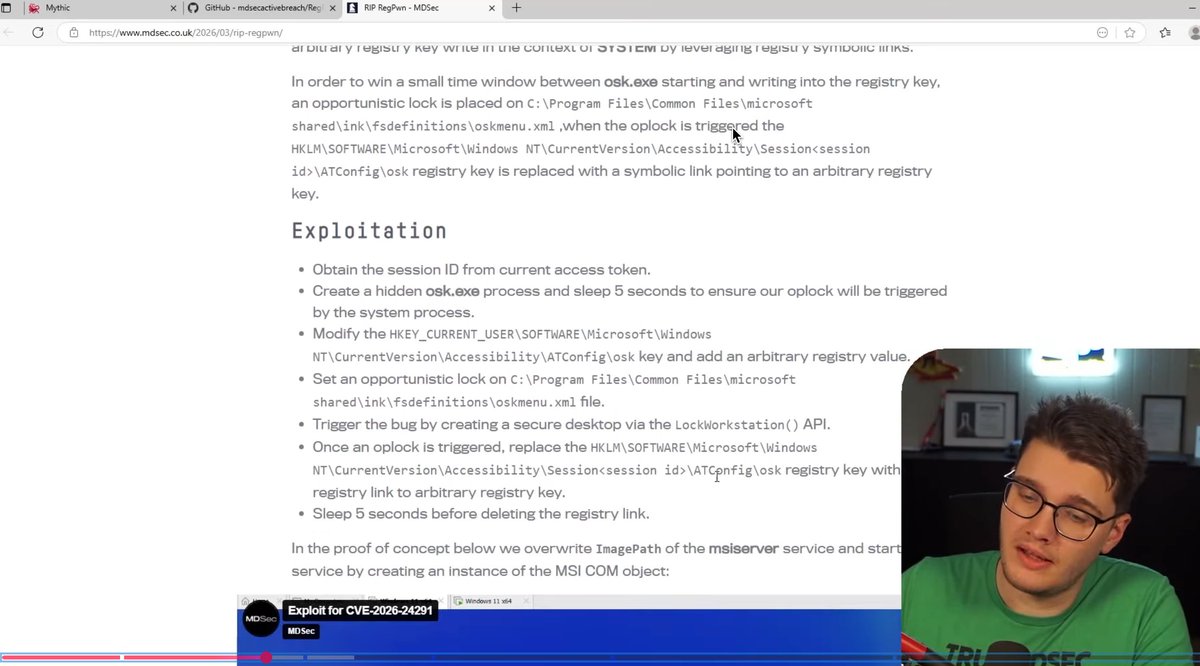
English
Dominic Chell 👻 retweetet

I am releasing a reconstructed version of the cassowary CVE (CVE-2024-23222) that was disclosed as part of the Coruna leak. I also did some research with my AI assistants 😄 to reproduce a crash for the bug on x86_64 Linux
github.com/FuzzySecurity/…
English
Dominic Chell 👻 retweetet

RIP FX
We collected some texts from the community in memory of @41414141 . You can find them here phenoelit.de/fx.html
English
Dominic Chell 👻 retweetet

New blog! We found an open directory attributed to #MuddyWater Iranian APT and found vulnerabilities/victims they've been targeting, red-team tools, and a loader that deploys a persistent variant of #Tsundere botnet - a MaaS sold by a Russian threat actor that is known for using #EtherHiding to store C2 addresses on the Ethereum blockchain.
esentire.com/blog/muddywate…

English
Dominic Chell 👻 retweetet

The next public edition of my "Offensive Entra ID" course will take place from June 8th to 11th in The Hague! Tickets are now available via events.outsidersecurity.nl/entra-26-07/. Last time the tickets sold out in a few weeks, so don't wait too long if you want to secure a spot.
English
Dominic Chell 👻 retweetet

> be uk government
> make web portal for doing taxes
> companieshouse
> click file for different company
> enter company number
> prompt for auth
> hit back button 3 times
> authentication bypassed
> ???
> full information leaked
> can modify company details for uk gov
> ???
Dan Neidle@DanNeidle
I see some weird things but this takes the biscuit. A vulnerability in the Companies House website, that let anyone view the private dashboard of any one of the five million registered companies, see directors' personal details. And modify them.
English
Dominic Chell 👻 retweetet
Dominic Chell 👻 retweetet

Recently, a report on the APT28 toolkit was published. APT28 is associated with Russia’s GRU military intelligence service
You can learn more about their recent tools and techniques here
hunt.io/blog/operation…
#apt #redteam #pentesting
English
Dominic Chell 👻 retweetet

Gdynia is calling. 🌊 The #x33fcon X training list is LIVE!
8 sessions announced:
🛠️ AI Sec: @abhinavbom
🛡️ Linux: @cr0nym
☁️ Azure: @matthieubjl & Paul
🕵️ eCrime: @jark
🦠 Malware: @DrCh40s & @t0nvi
🍏 macOS: @surya4n6
🏰 AD: @wil_fri3d & Guillaume
🔓 Physical: @tatramaco & Jiri
8/10 slots filled. 2 more surprises coming. 🤐
Grab your seat: x33fcon.com/#!training.md
#Infosec #Hacking #x33fcon2026 #CyberSecurity

English
Dominic Chell 👻 retweetet

We've had quite a few submissions to our CFP so far, but we still need more. If you have something interesting to share with the community, get it submitted here:
forms.gle/Sx4EZNRcS9zbCH…
English


@lazzslayer It’s a great course and @_dirkjan is a great instructor 🙏
English

got my ticket! 🔥🔥
Dirk-jan@_dirkjan
The next public edition of my "Offensive Entra ID" course will take place from June 8th to 11th in The Hague! Tickets are now available via events.outsidersecurity.nl/entra-26-07/. Last time the tickets sold out in a few weeks, so don't wait too long if you want to secure a spot.
English