Defused
715 posts


@DefusedCyber
Managed Honeypots for Early-warning Threat Intelligence 🍯 Access free honeypot intel: https://t.co/TTnxgiafkD















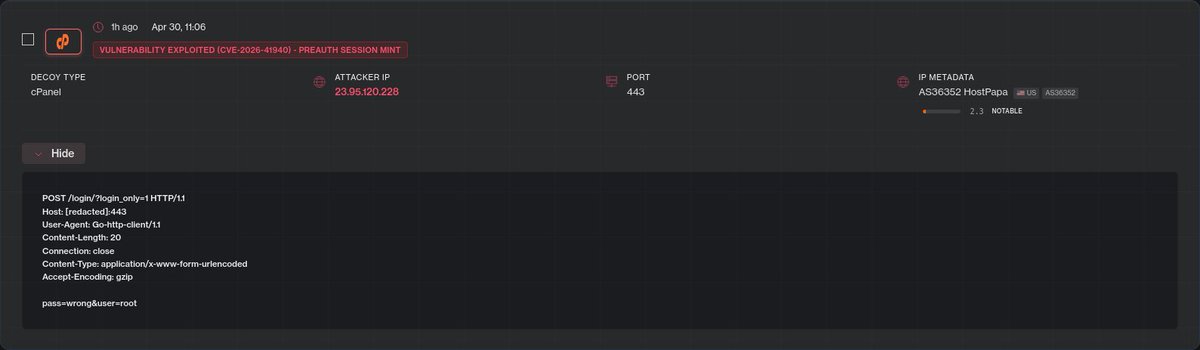
🚨 cPanel CVE-2026-41940 is undergoing active exploitation as of right now We are observing multiple actors actively attacking our cPanel honeypots, likely utilizing the recently released watchTowr proof-of-concept exploit Track live exploitation of cPanel 👉 console.defusedcyber.com/intel

🚨 cPanel CVE-2026-41940 is undergoing active exploitation as of right now We are observing multiple actors actively attacking our cPanel honeypots, likely utilizing the recently released watchTowr proof-of-concept exploit Track live exploitation of cPanel 👉 console.defusedcyber.com/intel