Jesko retweetet
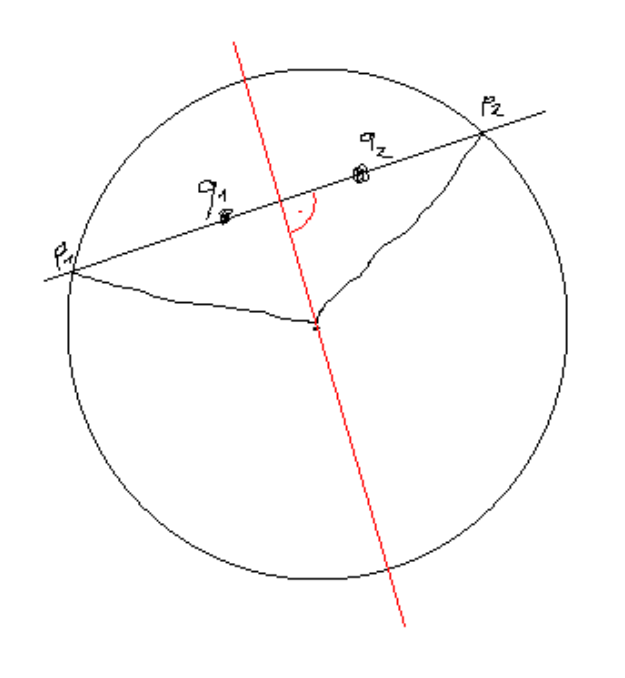
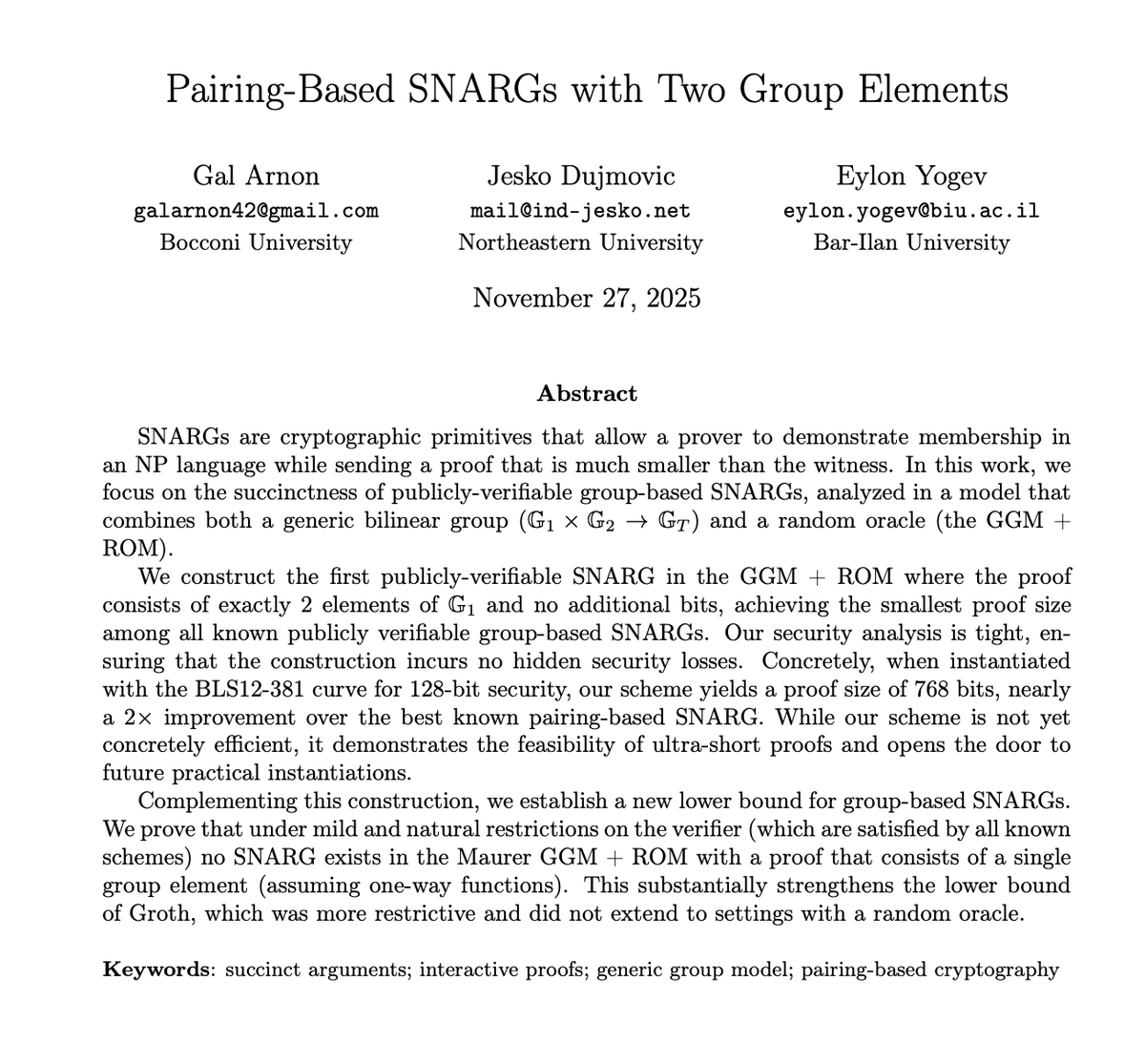
What's the limit of succinctness for pairing-based SNARGs? We answer this by constructing the first pairing-based SNARG with a proof of exactly 2 group elements (and 0 additional bits!)!
Joint work w/@IND_Jesko & Eylon Yogev.🧵👇
🔗 ia.cr/2025/2160
English