JBird Cyber
193 posts

JBird Cyber
@JBirdCyber
Helping folks break into cybersecurity. No-fluff career guides. CISSP
Beigetreten Aralık 2024
14 Folgt29 Follower

the rejection email is not feedback. it means you didn’t match the role on paper that week. it doesn’t mean unqualified. doesn’t mean unhirable. doesn’t mean start over. it means send the next one. keep going. #careertips
English

nobody talks about how boring the breakthrough actually feels. one tuesday you stop googling basic kql syntax. one friday a coworker asks you a question and you just answer. nothing happens. no fireworks. you just got better. keep going. #infosec
English

imposter syndrome lies. the analyst you think has it together googles basic KQL syntax three times a day. the senior who ‘just gets it’ failed Security+ in 2019. you don’t need to feel ready. you need to keep moving. that’s the whole job. #CyberSecurity
English

If you’re getting into cybersecurity, understand this early:
Not everyone is a hacker.
Most people think cybersecurity = hacking.
That’s not even close.
There are,
SOC Analyst who are the Defenders
GRC who builds policy, risk assesment and Compliance.
Red Teamers who are the Ethical hacker and Pentesters
There is more to cybersecurity beyond this.
English

@IamTheCyberChef Exactly. People don’t realize how much their current experience can actually be translated to SOC skills on their resume
English

Most people overcomplicate becoming a SOC analyst.
If you’ve ever:
- Checked Windows Event Viewer
- Investigated a failed login
- Restarted a suspicious service
- Looked through firewall logs
- Traced a user permission issue
Now add:
- Log correlation
- Basic attacker techniques
- SIEM familiarity
- Clear documentation
Congrats — you’ve already done the foundation of SOC work.
English

@mr_kay7 For sure. Once you start to understand this is when the SIEM really starts to come alive
English

I used to think a SIEM was just a giant storage bin for logs, but it’s actually more like a translator
Most devices speak in jargon that humans can’t understand, that's where "Normalization" comes in. It turns it into something a SOC analyst can read #SOC #SIEM #BuildInPublic



English

@DefendWithFelix @malik_cybersec @nacss_uniosun @KoredeSec @ife0x01 Underrated knowledge to have IMO
English

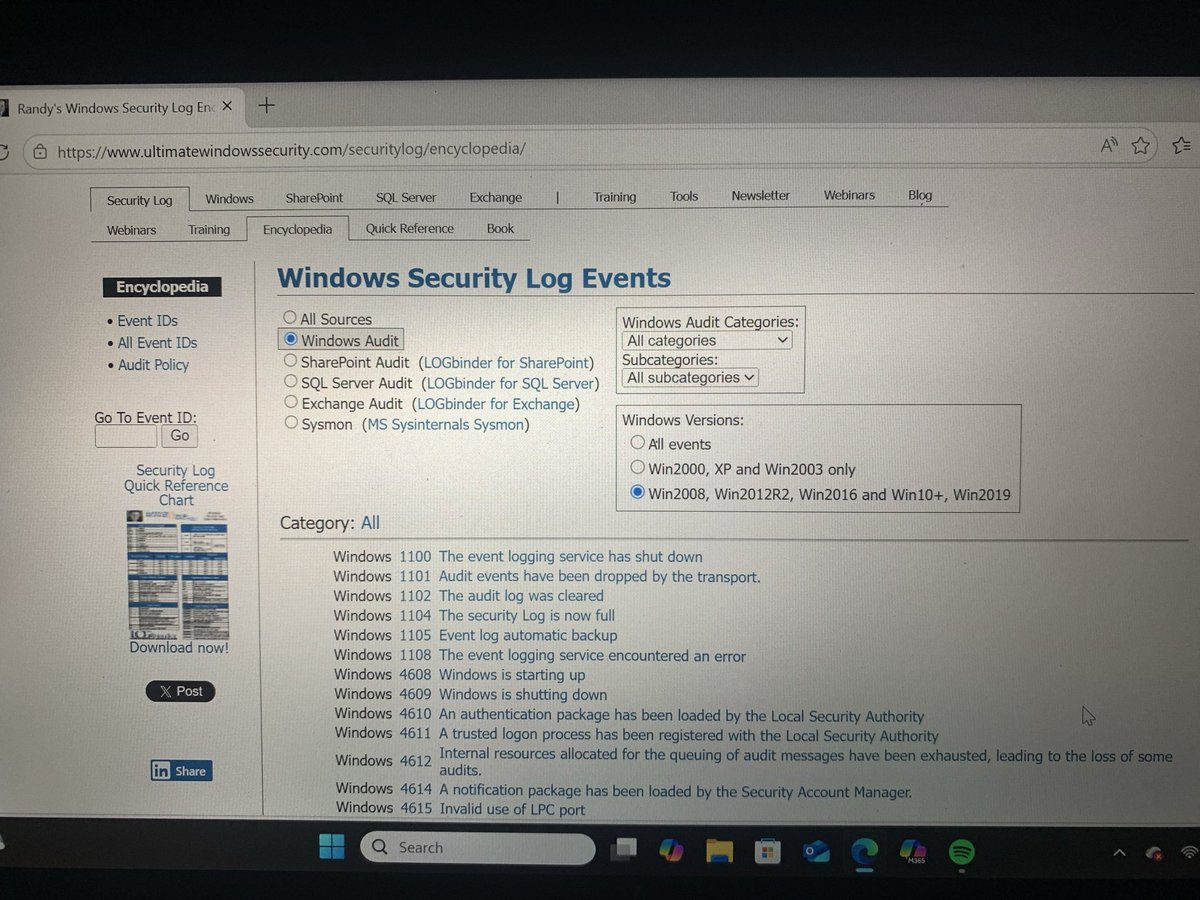
Day 2 of #30DaysOfSOC ✅
Today was all about Windows Event Logs.
Digging into the Event IDs every SOC analyst needs to know failed logons process creation new accounts and more.
The logs don’t lie🔍
#SecFelix #CyberSecurity #BlueTeam #SOCAnalyst #WindowsEventLogs @malik_cybersec
Oluwanifemi Felix Oyeniyi@DefendWithFelix
Day 1 of #30DaysOfSOC ✅ Completed the Case Creation & Playbook Initiation lesson on LetsDefend today. The journey has begun. 🔵 #SecFelix #CyberSecurity #BlueTeam #SOCAnalyst #LetsDefend #30DaysOfSOC @malik_cybersec @nacss_uniosun @ife0x01 @LetsDefendIO @hackthebox_eu
English

@CyberRacheal Soft skills for sure led to climbing the ladder faster
English

@CyberRacheal Couldn’t have said it better. I started in “hell desk” and I don’t think I’d be where I’m at now if I didn’t. Would I ever do help desk again? Absolutely not 😂, but it’s slept on as a way to build the resume to make the pivot
English

Look, I see it all the time in my training sessions:
students think a Bachelor’s or Master’s degree is a golden ticket straight into a SOC Analyst or Pentesting role.
The hard truth I have to tell them is that if you graduate without any internships or hands-on experience, that degree usually won't bypass the fundamentals.
Most graduates are surprised when their first job offer is for a Help Desk or basic IT Support role.
In this industry, we value skills over certificates. Even though certificates are regarded as well.
A degree proves you can learn, but experience proves you can defend a network under pressure.
If you aren't getting your hands dirty with internships or home labs while you're in school,
be prepared to "pay your dues" in entry-level IT before you land that specialized cybersecurity seat.
Start NOW!
English

someone deeply interested in cybersecurity, one resource I’ve found consistently valuable is the Cisco Networking Academy.
They’ve recently introduced a structured learning path for a Cybersecurity Defense Analyst (SOC Analyst) role focused on skills like threat detection, incident response, and security monitoring.
For anyone looking to break into cybersecurity, especially in blue team roles, this is definitely worth exploring.
I’ve personally found their courses practical and beginner-friendly, especially for building a strong foundation.
If this aligns with your goals, I’d recommend checking it out.
English

@tolad_ That’s pretty solid. That’s a big ask for an interview in my opinion !
English

SOC Analyst interview at the Imperial College, London.
“As part of your interview, you have been asked to prepare a 5-minute presentation or discussion point on the following topic:
As a SOC analyst, if you were given a task to harden Active Directory, how might you expect to approach this?”
👇
One of my points was wrong, considering that students have Active Directory accounts and it’s a global college where students are from all parts of the world.
Tolulope@tolad_
I’d like to share some of my job interview near misses. Specifically with top organisations like Tanium, Serco, Mimecast, Imperial College and Cloudflare. What went wrong (self reflections and feedback from hiring managers). I hope that these stories would strengthen my people.
English

@sec_hub93028 Definitely not in my opinion. Maybe so if you consider GRC specific
English

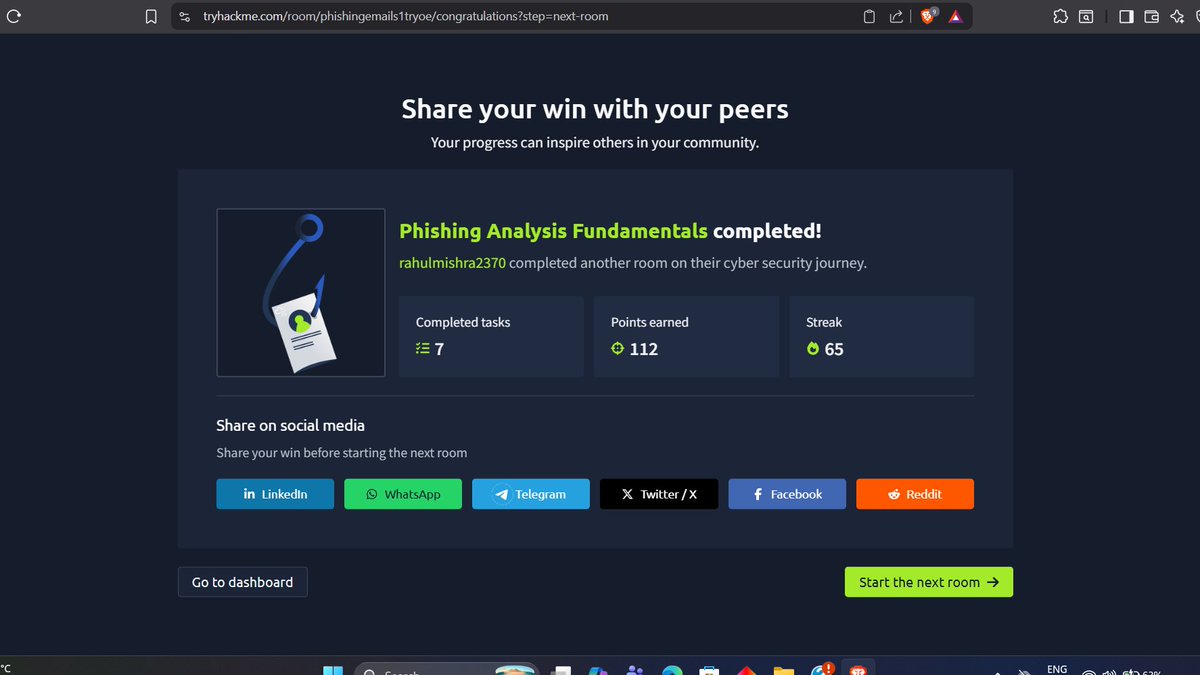
@romeo150x @tryhackme This is dope. Phishing analysis is one of the non-negotiable skills for any analysts we hire!
English

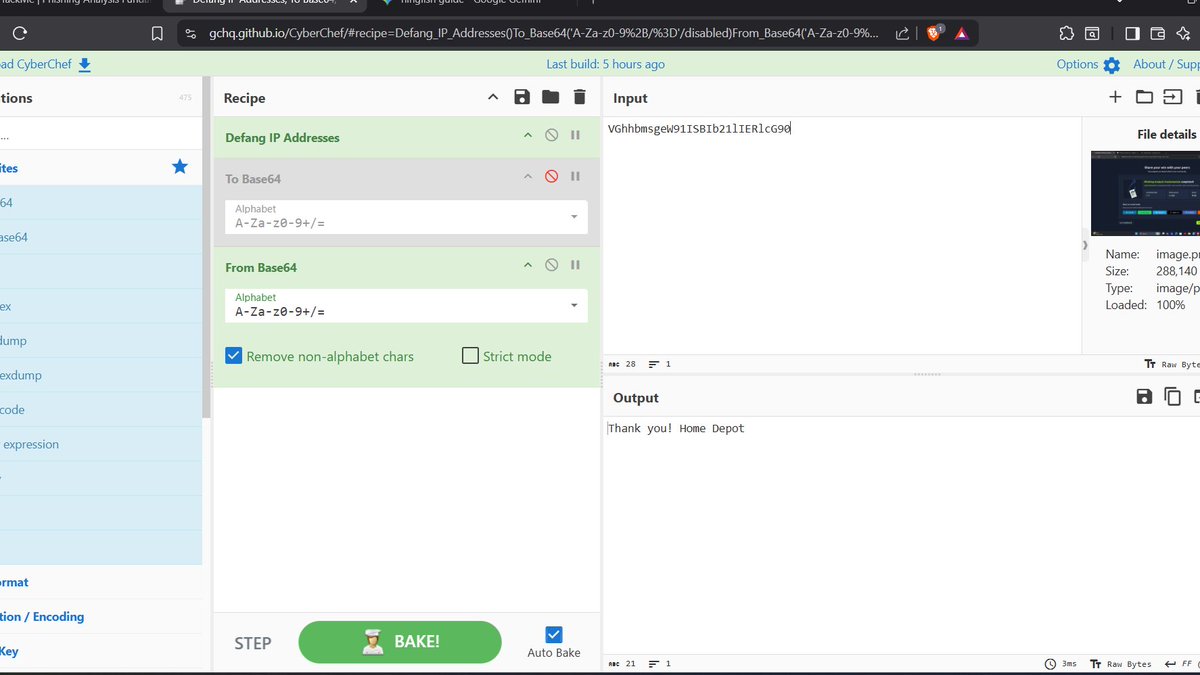
Just crushed the Phishing & Email Analysis room on @tryhackme
Dissected raw email headers, decoded Base64 malicious payloads using CyberChef, and hunted down obfuscated brand impersonation attempts. Tactical defense mode: ON
#SOCAnalyst #CyberSecurity #BlueTeam #ThreatHunting
English
I successfully earned the 3 Days Streak badge on @CyberDefenders! cyberdefenders.org/blueteam-ctf-c…
#CyberSecurity #BlueYard #blueteam #InfoSec #SOC
English

@Dr_SevenLabs @CyberRacheal @JolieOrich @dmlszn_cyber @smbclient1 @AltSchoolAfrica Lfg. Phishing analysis one of the core things I make sure analysts are comfortable with in our interviews !
English

Phishing emails tried it… I analyzed it 🕵️♂️🛡️
Just completed a hands-on Phishing Analysis challenge. Diving into email headers, tracing delivery details, and spotting red flags
one lab at a time. On to the next challenge 🚀
#CyberSecurity #SOCAnalyst #BlueTeam #Phishing #InfoSec




English

@est_faithy Great skill to get advanced at. One of the core things I make sure our analysts are comfortable with during interviews!
English

Today I started learning about phishing analysis and the different types of phishing attacks, along with the techniques attackers use to obtain sensitive information and deploy malware.
#Cybersecurity #SOCAnalyst #Phishing #LearningInPublic

English

Blue Team Cybersecurity Roles You Should Know 👇
🔵 SOC Analyst
🔵 Threat Hunter
🔵 Incident Responder
🔵 DFIR Analyst
🔵 Security Engineer
🔵 SIEM Engineer
🔵 Cloud Security Analyst
🔵 Vulnerability Analyst
🔵 IAM Analyst
🔵 Detection Engineer
Which role fits you best?
#BlueTeam

English


