Sabitlenmiş Tweet
vxdb
1.7K posts


vxdb
@vxdb
Journalist | Cybercrime News | Staff @vxunderground | PGP - https://t.co/VWwniNXrEc
Cyberdelia Katılım Aralık 2012
473 Takip Edilen24.2K Takipçiler

inb4 they turn it into an Ai company
Watcher.Guru@WatcherGuru
JUST IN: GameStop $GME offers to buy $EBAY for $56,000,000,000.
English

One of the most frequent questions I'm asked is "how do you stay up to date on malware stuff?"
Okay, here is a pro tip:
1. Google OTX AlienVault
2. Make account
3. Look at latest
4. Scroll until you find posts from a guy named Petr something-something (has numbers in his name).
4. Follow his account
He monitors all the big malware places and shares the URL, hashes, etc. from malware vendors. I've been following this random ass dude for years and getting updates on everything.
I have no idea who he is. I don't know where he's from. All I know is his setup is absolute fire and he keeps you up to date on literally everything malware related 24/7 365. He also has stuff from vendors in China, Russia, Japan, etc.
Every morning I log into OTX and check up on my boy Petr to see what fire he's bringing me. I love him.
English

Just got done talking at Georgia Institute of Technology.
I was introduced to a bunch of cybersecurity students as "cybercrime TMZ", a person who "collects pictures of cats", "fills computers with mayonnaise", and discusses things with "Dragon Ball Z" references.
On paper this shit makes me look like a lunatic.
The entire room was dead silent as I vaped and spoke schizophrenic nonsense.
Chat, I DO NOT think they'll be inviting me back
English

OH GOD THEYRE GOING TO VIBE CODE A MOBILE OS
SAM DONT DO IT

Polymarket@Polymarket
JUST IN: OpenAI is reportedly developing a smartphone designed to "make apps obsolete" by replacing them with AI agents.
English

@EricParker You are missing the exclamation point at the end for added security
English



Attackers target weak verification infrastructure, then use that access to abuse the trust larger organizations extend to any official-looking source. Weak links don't stay local.
Verify before you comply. bit.ly/4837bQV

English


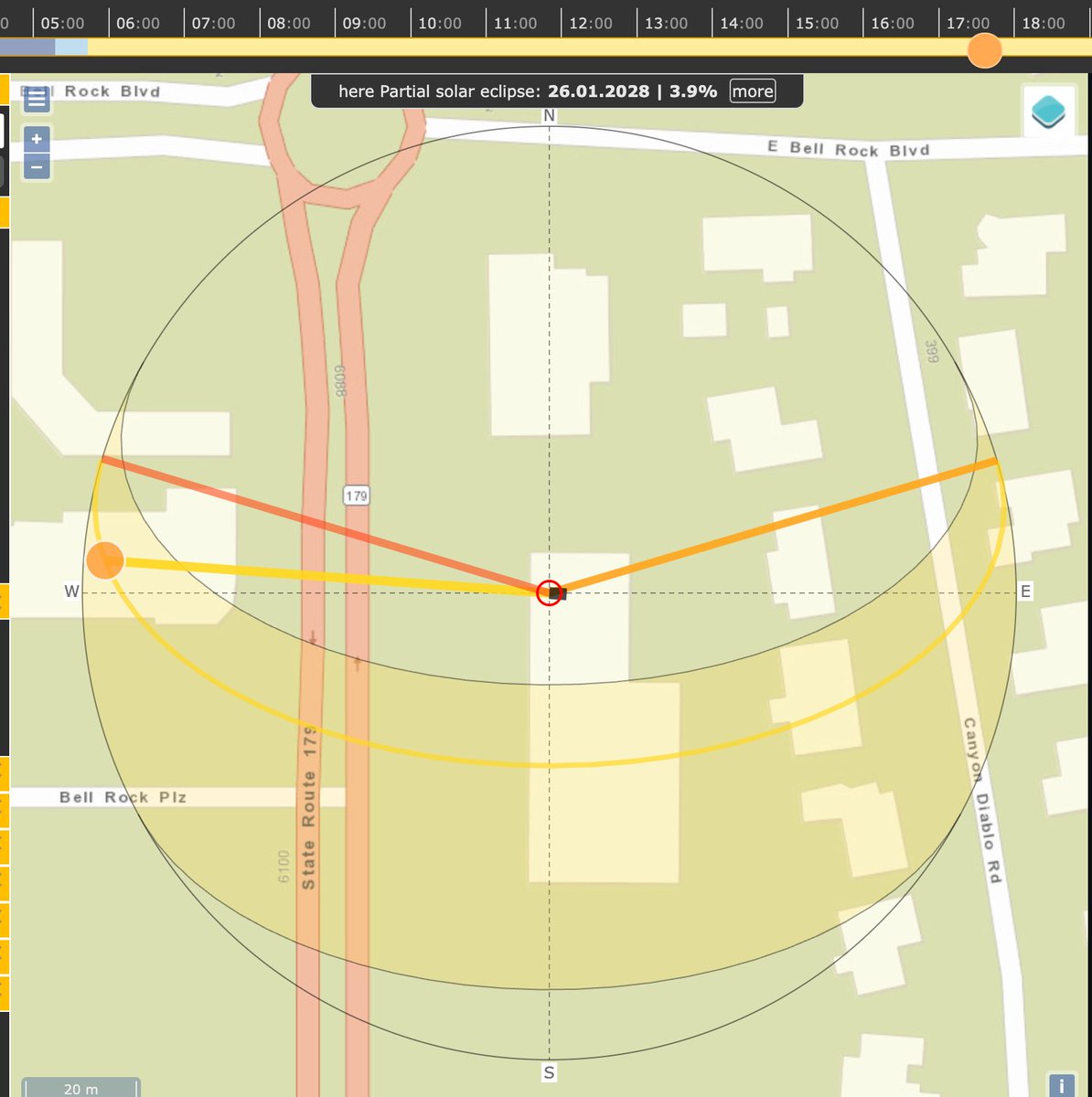
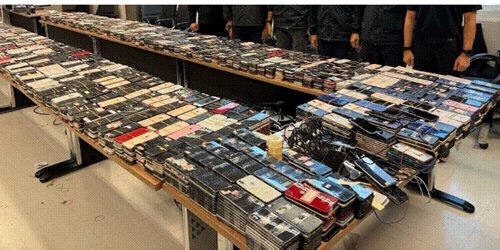
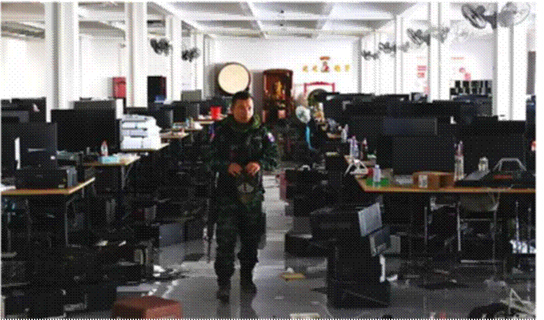
Yesterday, the DOJ made a press release confirming a coordinated crackdown against a massive Southeast Asian scam compound
Two Chinese nationals ran a forced-labor fraud factory in Myanmar called the Shunda compound. Trafficked workers, beaten and held against their will, were forced to run cryptocurrency investment and romance scams targeting Americans. One worker's team stole 3 million dollars from a single victim. When a militia seized the compound in late 2025, the FBI flew to Thailand, reviewed over 1,300 desktop computers and thousands of phones, and interviewed former workers. They tracked the two managers to Cambodia, where they tried to keep operating, then arrested them in Thailand on immigration charges. They are now facing federal wire fraud conspiracy charges in the US.
Separately, the Feds seized a Telegram channel with around 6,000 members that was recruiting English speakers with American accents for fake jobs in Cambodia. Once there, workers were held against their will and forced to impersonate JPMorgan Chase, customer service reps, and NYPD detectives over WhatsApp and Microsoft Teams, telling victims their bank accounts were used to buy illegal firearms, then draining their savings.
The Strike Force also seized 503 fake crypto investment websites in a single operation, seized over 700 million dollars in cryptocurrency tied to money laundering, and sanctioned Cambodian officials linked to scam center operations.

English