Angehefteter Tweet
spidersec
329 posts

spidersec retweetet

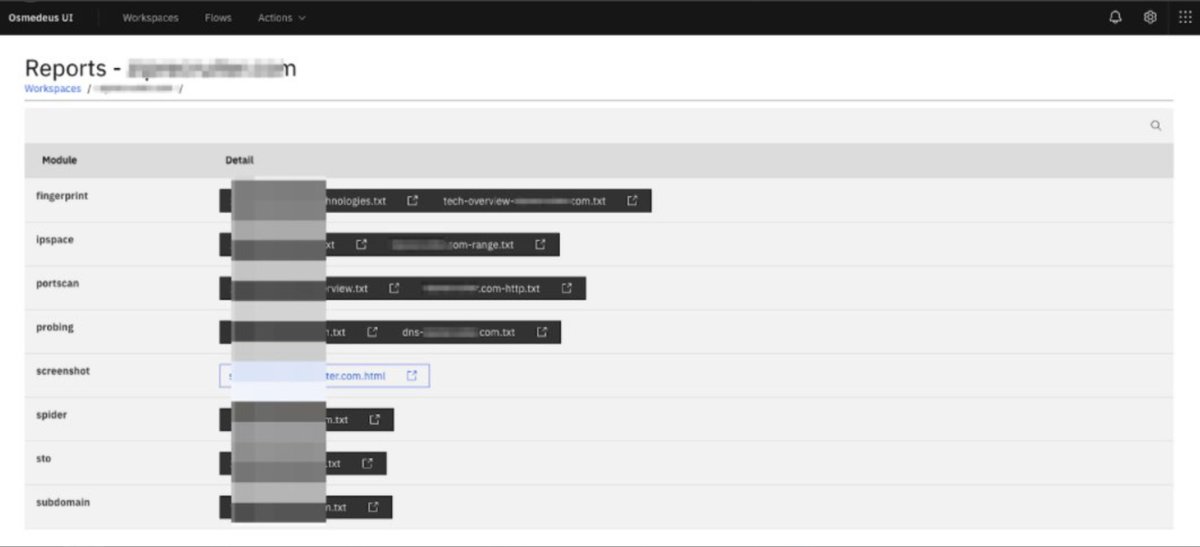
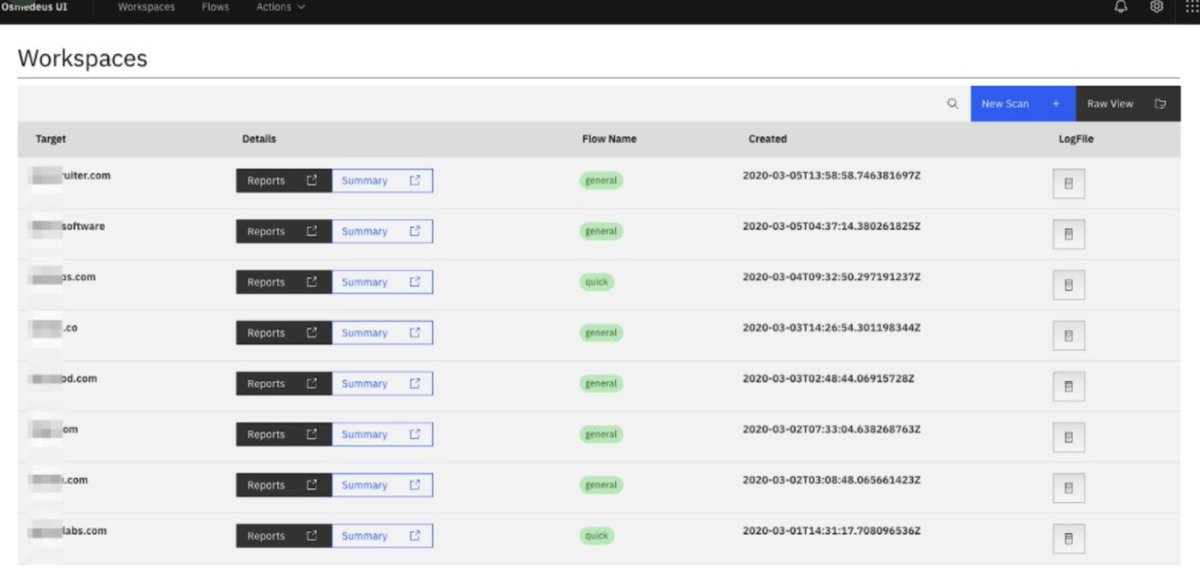
⚙️ A lesser known tool, Osmedeus is the closest to Nuclei, that comes with an amazing web UI. You can use custom YAML workflows and vulnerability signatures just like Nuclei.
🔗 github.com/j3ssie/Osmedeus
#bugbounty #bugbountytips #infosec #cybersecurity #Pentesting
English
spidersec retweetet

github.com/jmdx/TLS-poiso…
This is fucking bananas and I can't believe I missed it.
English
spidersec retweetet
spidersec retweetet

Exploiting Redis Through SSRF Attack infosecwriteups.com/exploiting-red…
English

In the industry:
Certifications are usually overrated.
Skills are hugely underrated.
What do you prioritise when hiring hackers to secure your product?
#infosec #cybersecurity #infosecjobs #bugbounty
English
spidersec retweetet

spidersec retweetet

Our Pre-Auth RCE exploit for Atlassian Confluence (CVE-2021–26084) was leaked after reporting it to @VMware. They have refused to admit the leak and ignored our emails.
tradahacking.vn/atlassian-conf…
English

@satish28888 @satish28888 I personally use these nuclei templets and tools for my day-to-day work, they give good results.
github.com/xm1k3/cent
gist.github.com/ihebski/c166a9…
gist.githubusercontent.com/0x240x23elu/1c…
github.com/SigmaHQ/sigma/…
github.com/ARPSyndicate/k…
github.com/six2dez/reconf…
English

I am trying out Nuclei for some testing . Eventually would love to integrate it to my every day work. Does anyone have any references for templates for web applications testing.
@SpiderSec
English
spidersec retweetet

@hummus_ful Yes you are correct, its not a valid test case for layer 4
English

@SpiderSec I guess that's true for only application layer (L7) rate limits, not network (L4) layer, or am I missing something
English