Fox
1.4K posts

Fox retweetledi

@zetachain @esatoshiclub Zetachain lets you call a Bitcoin wallet from an Ethereum smart contract no bridges or wrapped BTC needed!
English

Thanks to everyone who joined our 𝕏 Space with @esatoshiclub today!
As promised — we’re giving away $400 ZETA 🎉
🟩 Like this post
🟩 In the comment: share one thing you learned or found interesting from the Space
We'll pick 4 winners after 24 hours.
ZetaChain 🟩@ZetaChain
Ready to explore the future where Bitcoin seamlessly connects with every blockchain? Join our 𝕏 Space with @esatoshiclub on April 29 at 1 PM UTC. 🟩 $400 ZETA Giveaway 🟩 Set your reminder: twitter.com/i/spaces/1jMJg…
English

@BGatesIsaPyscho Not true, this is is Maya Bay at koh Phi Phi. You cannot enter in the water because of the sharks
English

@dustfuncrypto @zetachain Some say it’s just a degen meme protocol, others believe it’s a portal to an alternate dimension where every dust wallet holds millions in lost Bitcoin. But the truth? The truth is hidden in the etherscan tx history of the Illuminati’s MetaMask.
English

💥 WHAT IS DUST.FUN? Winner gets $20 USDC! 💥
Drop the funniest, most exaggerated, or totally wild answer you can think of! 🤪
💸 The funniest comment wins $20 USDC!🔥Comment as many times as you want.
📢 Winner announced at the Twitter Space AMA with @ZetaChain on Monday.
Judges: @maistebuilds & @ZetaChain 🚀
English

When Bitcoin hits $100,000 I will give 1 BTC to one person who follows me.
The rules are simple:
- like this tweet, follow me and RT
- comment “100k incoming”
Let’s go! $BTC #bitcoin
English
Fox retweetledi

Today I received a $12,000 bounty using the Sandwich Attack ! 🤑
The vulnerability allowed me to enumerate the API Keys of other users 🤯
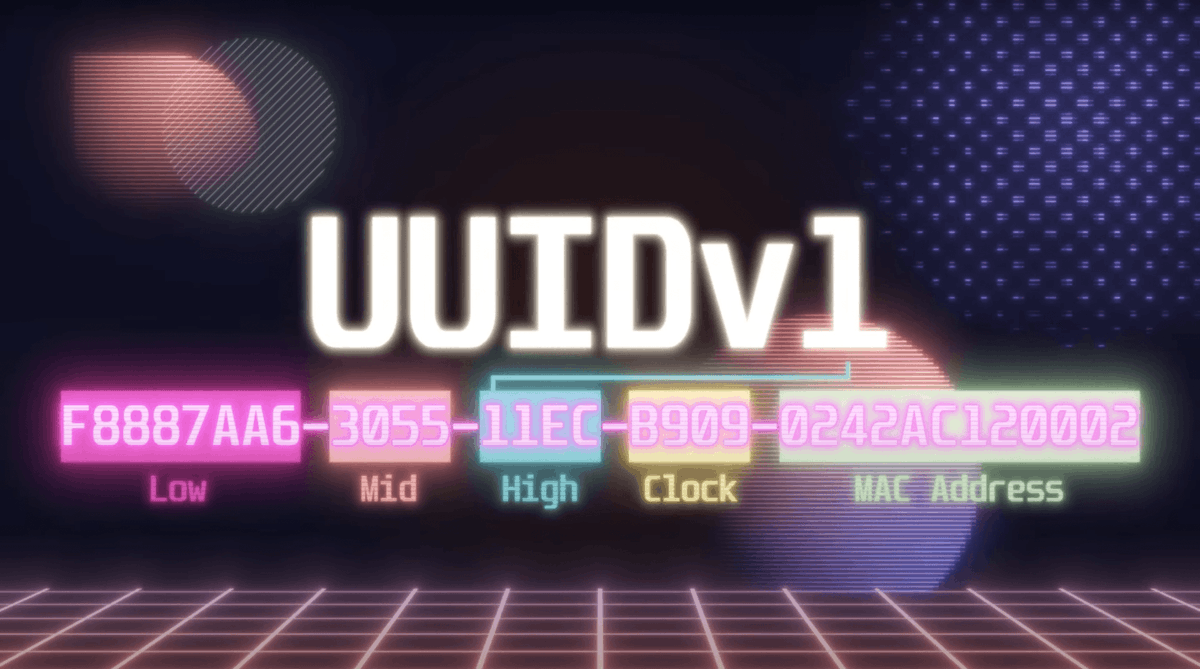
How did I do that ? Well the API key was a UUIDv1. If you are not familiar with UUIDv1s you need to know that they are constructed in 6 sections:
High, Mid, Low, Clock Sequence, Node ID, and UUID version.
Interestingly, the Node ID corresponds to the MAC address of the system generating the identifier. This means that if two consequent UUIDs are generated on the same device, this part remains the same, similar to the Clock Sequence.
When High, Mid, and Low are combined, they reveal a timestamp represented in hexadecimal value.
Using some basic mathematics it's possible to subtract the offset between the Gregorian Calendar and the Julian Calendar and then divide by 1000 to get an Epoch TimeStamp.
Ok now that we know that they are generated by a timestamp + machine ID, it means that we could generate them back if we know when the API keys were created 🧐
Luckily enough the API Key that I was using was generated in a batch, meaning I could use the Sandwich Attack in order to brute force the API Keys of other users easily 🔥
If you want to know more about how I exploited the Sandwich Attack, go check my video about this on my YouTube channel 🤟



English
Fox retweetledi
Fox retweetledi

Are you interested in freelancing in cybersecurity and automation services?
I'm on the lookout for people who are interested in freelancing in Cybersecurity &/OR Automation of business processes within the IT industry with training starting immediately.
If this sounds like you, please get in touch with me!
#cybersecurity #freelancing #freelancer #automation #ai #workfromanywhere

English
Fox retweetledi

Analysis of the Stars Arena exploit:🔽
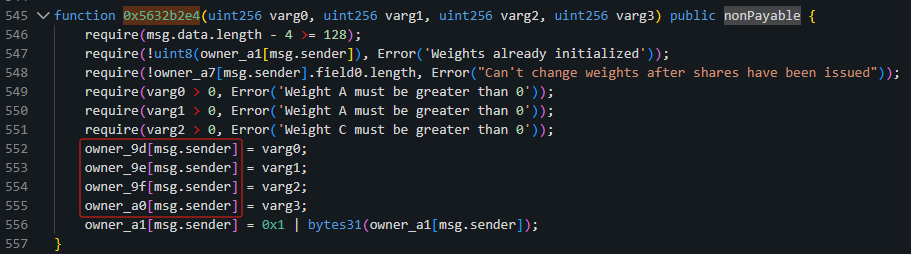
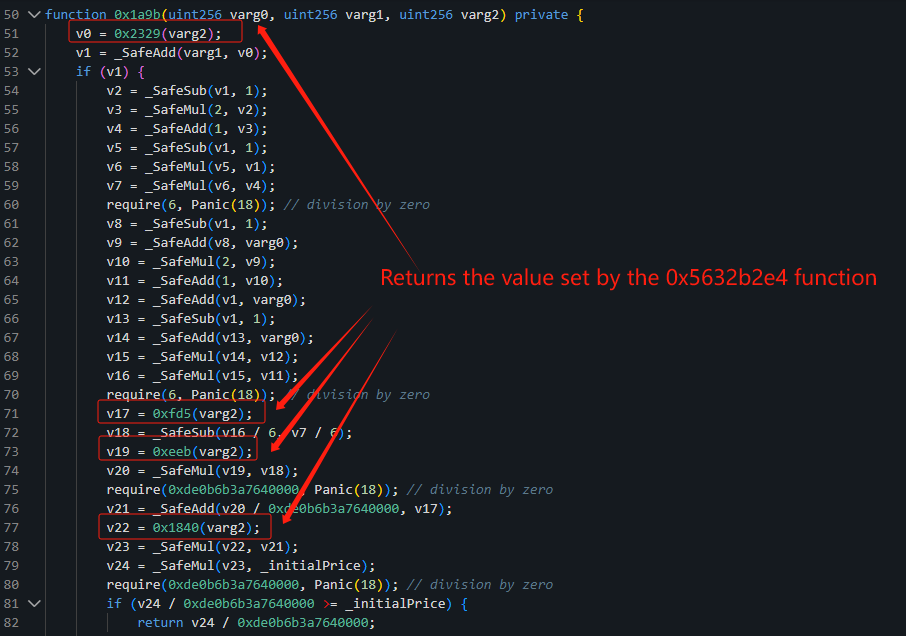
The contract is not open source, there seems to be a reentrancy vulnerability.
During the call of the 0xe9ccf3a3 function, the attacker reentered and called the 0x5632b2e4 function, setting a block height.
Then, in the sellShares function, this height was used as a parameter to calculate the amount of $AVAX to send, resulting in an abnormally large calculated amount. Ultimately, the attacker was able to obtain a large profit.
Beosin Alert@BeosinAlert
Stars Arena on AVAX exploited for ~$2.9M. Stay alert!
English
Fox retweetledi
Fox retweetledi

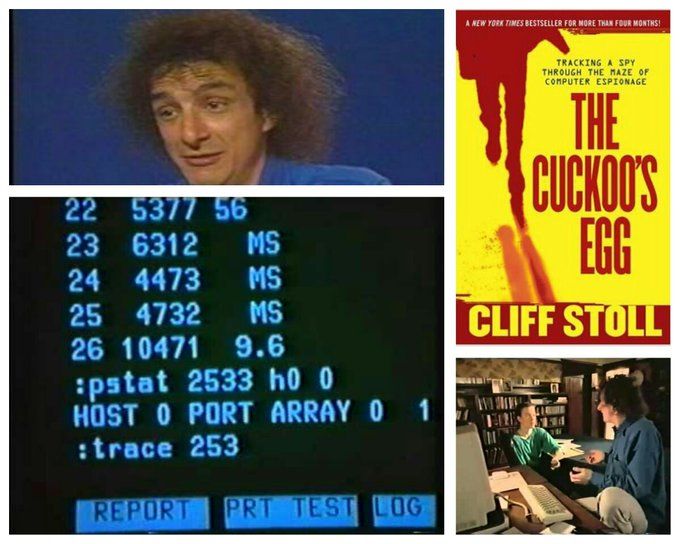
1990: Clifford Stoll's book "The Cuckoo's Egg" was turned into an episode of NOVA entitled "The KGB, the Computer, and Me". Without spoiling it, it's a story of how he tracked down a hacker who broke into his employer's computer. Watch it for free: archive.org/details/The_KG…
English
Fox retweetledi

$50k bug bounty on Shopify explained.
In this video, learn how Augusto Zanellato found a critical GitHub PAT linked to private Shopify repositories, earning a $50,000 bounty!
Watch now 👇
youtube.com/watch?v=xOoWHK…

YouTube
English
Fox retweetledi

Use silent #SMS messages to track LTE users’ locations
An attacker sends silent SMS messages with a defined pattern and analyze LTE traffic to verify the victim location.
All you need is just: SDR + SIM cards + LTESniffer software
mandomat.github.io/2023-09-21-loc…

English
Fox retweetledi
Fox retweetledi
Fox retweetledi

For everyone who didn't get to my @nullcon @paymentvillage training, I suggest starting with this free content:
slideshare.net/a66at/offensiv… - Offensive Payment Security (2h workshop)
paymentvillage.org/workshop - Payment Village DEF CON workshop (3h workshop about magstripe)
English
Fox retweetledi

NEW fully undetectable AMSI bypass script based on Matt Graeber @mattifestation 'amsiInitFailed' script.
After one year my "old" AMSI bypass script is now detected by 9 AV. So here is the new fully undetectable script:
@kmkz_security

Norbert Tihanyi, PhD@TihanyiNorbert
My new AMSI bypass script based on Matt Graeber @mattifestation 'amsiInitFailed' script. With a little math 0/59 AV detects as malicious in 2020. Happy pentesting. @kmkz_security
English