AI Support for DeFi
227 posts


AI Support for DeFi
@TxDesk
Your support tools can't read a transaction. I'm fixing that. Building AI support agents for DeFi protocols. website: https://t.co/8m2Z0WhLlf







Unbelievable, shut down your protocols or something new victim: @syndicateio


Wasabi hurts, i know a number of people who used it DeFi expected yields were already low, now they starting to feel negative



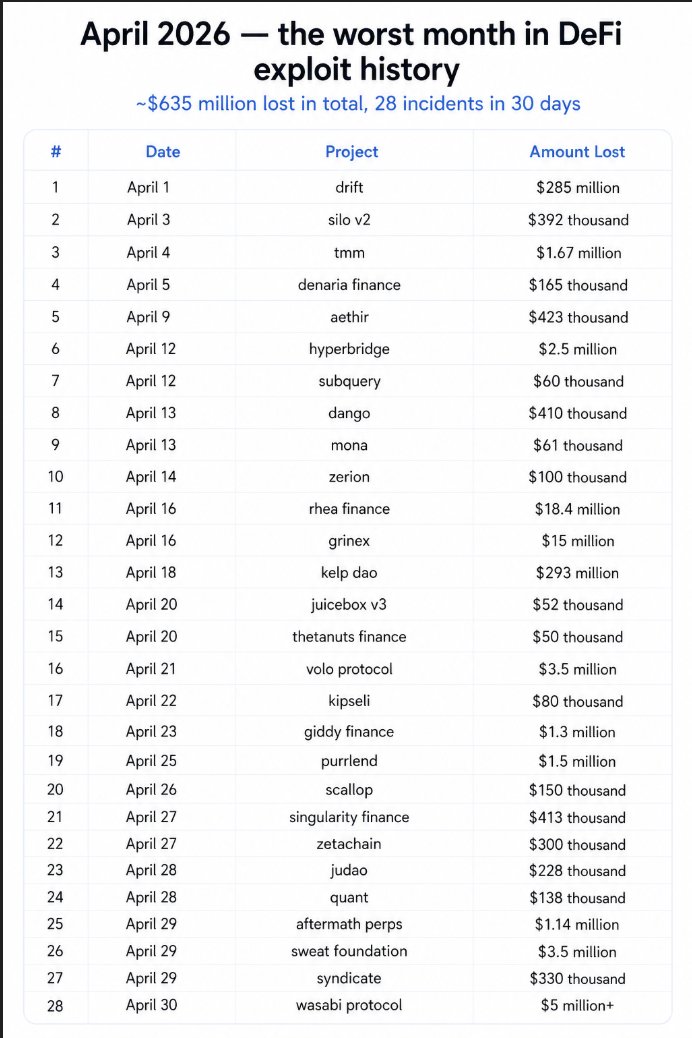
Over $421 M has been drained from crypto this year. April saw the highest amounts drained, as £288.35 has been drained so far. This is the list of drain events that have happened since the beginning of this year. -------------------- ➢ 𝐉𝐚𝐧𝐮𝐚𝐫𝐲 > @StepFinance_ lost $30M because several treasury and fee wallets got compromised. On-chain activity on Solana pointed to compromised private keys. > @Truebitprotocol lost $26.4M because an error in an old forgotten contract allowed attackers to mint TRU tokens for free, then burn them to drain protocol value. > @SagaEVM lost $7M because of a supply chain hack, inherited vulnerabilities in EVM precompile bridge logic from Ethermint that the protocol never patched. > @ApertureFinance lost $4M because their V3/V4 contracts contained an arbitrary call vulnerability, similar to the SwapNet exploit that same month. > @makinafi lost $4.1M because attackers exploited flaws in the execution logic of its DUSD/USDC CurveStable pool to drain funds. > TMX lost $1.4M because an attacker used USDT to mint TMX LP tokens, swapped USDC for USDG, then looped unstaking and selling USDG on Arbitrum. -------------------- ➢ 𝐅𝐞𝐛𝐫𝐮𝐚𝐫𝐲 > @iotex_io lost $8.8M because an attacker compromised the private key managing the Validator contract on the Ethereum side of their cross-chain bridge, stealing reserves and minting 111M CIOTX tokens. > @crosscurvefi lost $4.95M because validation bugs in their bridge's smart contracts allowed attackers to spoof Axelar messages, tricking the PortalV2 contract into releasing funds for a fake cross-chain deposit. > @MoonwellDeFi lost $1.78M because AI-generated code used only the cbETH/ETH exchange rate as its price, skipping the ETH/USD multiplication, valuing cbETH at $1.12 instead of $2,200. > @blend_capital yieldBlox pool was exploited using price manipulation of the USTRY asset. They lost $10m in a mixture of USDC and XLM > Ploutos Money lost $390K due to an oracle misconfiguration. The oracle was mistakenly configured to use the BTC/USD Chainlink price feed to price USDC. They've had their socials deleted since then -------------------- ➢ 𝐌𝐚𝐫𝐜𝐡 > LMI/USDT staking protocol lost $950K because a price manipulation attack exploited flawed pricing logic, allowing the attacker distort valuations and withdraw inflated staking rewards > GoonFi lost $254K because mispricing arbitrage exploited incorrect asset valuation, letting the attacker repeatedly profit from price discrepancies across pools > @Cyrus_Finance lost $5M because a flashloan attack manipulated pool share calculations, allowing the attacker mint excess shares and redeem more assets than deposited > @ResolvLabs lost $24.5M because a private key was compromised, giving the attacker privileged access to drain protocol funds > @dTRINITY_Defi dLEND lost $257K because a deposit inflation attack manipulated accounting logic, allowing the attacker inflate deposits and withdraw more than contributed > @VenusProtocol Pool lost $3.7M because a donation attack skewed internal accounting, allowing the attacker withdraw more funds than their actual share > @Goosedefi lost $8,435 because a share accounting flaw miscalculated balances, letting the attacker withdraw funds. > @StakeDAOHQ lost $176K because oracle message spoofing allowed attacker to extract funds > @Gondixyz V3 lost $230K because a PurchaseBundler exploit bypassed transaction checks, allowing the attacker manipulate bundled operations and gain unauthorized assets > M0lt EVM lost $127K because a flawed token modifier allowed unauthorized actions, enabling the attacker bypass restrictions and extract funds > @SolvProtocol lost $2.7M because a mint reserves logic exploit allowed tokens to be minted without proper collateral, draining protocol liquidity > @FOOMCash lost $2.26M because a fake proof spam attack bypassed verification logic, allowing the attacker mint or withdraw funds without valid proofs -------------------- ➢ 𝐀𝐩𝐫𝐢𝐥 > @zerion lost $100K because a hot wallet compromise exposed private keys, allowing the attacker gain direct access and drain funds > @dango lost $410K because attacker exploited a bug in the insurance fund's logic and drained USDC collateral held in the perps contract. > @SubQueryNetwork lost $60K because an access control exploit bypassed permission checks, allowing the attacker execute restricted functions and move funds > @hyperbridge lost $237K because fake state proof validation failed, allowing the attacker submit forged proofs and withdraw assets illegitimately > @AethirCloud lost $423K because an access control vulnerability allowed unauthorized privileged actions, enabling the attacker drain funds from protected contract functions > @SiloFinance lost $392K because a misconfigured oracle fed incorrect pricing data, allowing the attacker manipulate collateral values and overborrow assets > @DriftProtocol lost $285M because compromised admin credentials enabled unauthorized control, allowing the attacker upgrade contracts or withdraw funds at scale > Mona lost $60,950 because a burn address accounting flaw miscalculated supply, enabling the attacker manipulate balances and extract excess tokens It has been a crazy year so far and I hope protocols can work more on security. Daily bug checks, dedicated security team and so much more to make sure users don't lose funds.









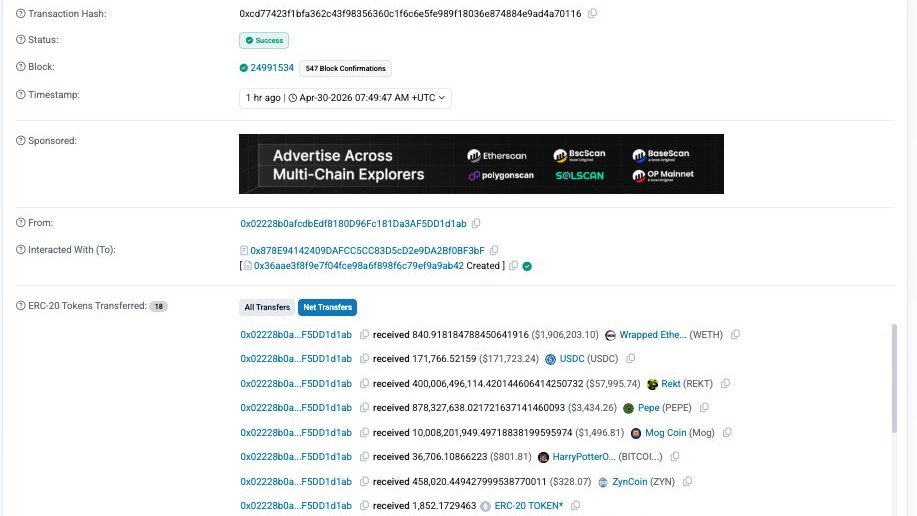





It seems the admin key of @wasabi_protocol has been compromised with the estimated loss of $5.5m across multiple chains, including ETH, BASE, BLAST, and BERA chains. Here is the related tx to add the malicious admin: etherscan.io/tx/0x11ff84ffb…




Attention Aftermath community - We’ve identified an exploit affecting the protocol. Our team is actively investigating alongside leading security partners. As a precaution, the protocol has been paused and measures are being taken to minimize potential impact to user funds. We’ll continue to share updates as we learn more. Thank you for your patience.


🚨Community Alert: Ongoing exploit on @SweatEconomy on @NEARProtocol. Exploiter: 3be304b2151870b2be88b9de0b80acab921337ad152584138bd852fc6e9ae018 Largest exploit tx: DvrSMfY85Anc6AuLUmoEDkDdab7qX5NUZLu76HN8NoPn




Attention Aftermath community - We’ve identified an exploit affecting the protocol. Our team is actively investigating alongside leading security partners. As a precaution, the protocol has been paused and measures are being taken to minimize potential impact to user funds. We’ll continue to share updates as we learn more. Thank you for your patience.