
Ben
174 posts
Ben
@XploitBengineer
Android Vulnerability Researcher, Pwn2Own 202{3, 5}
planet earth Beigetreten Nisan 2016
595 Folgt1K Follower
Ben retweetet

Long overdue episode with the iOS avengers @s1guza @littlelailo @iBSparkes @jonpalmisc @hdemoff_ open.spotify.com/episode/7IyjVv…
English
Ben retweetet
Ben retweetet

After weeks of reverse engineering MediaTek's DA2 with @shomykohai, we finally figured out how the V6 exploit works. We decided to call it heapb8 ("heapbait")!
Technical writeup: blog.r0rt1z2.com/posts/exploiti…
PoC: github.com/shomykohai/pen…
English
@SinSinology @InterruptLabs It's a mystery, for sure.
Looks like you had a great time in Japan btw, solid work 💪🏻
English

@XploitBengineer @InterruptLabs you're right! that looks like mitm to me too!
i'm wrong in that case, now i got no idea when it is and when its not allowed
English
Latest from our Labs - @XploitBengineer looks at how NAS vendors get TLS wrong, and why this matters.
interruptlabs.co.uk/articles/when-…
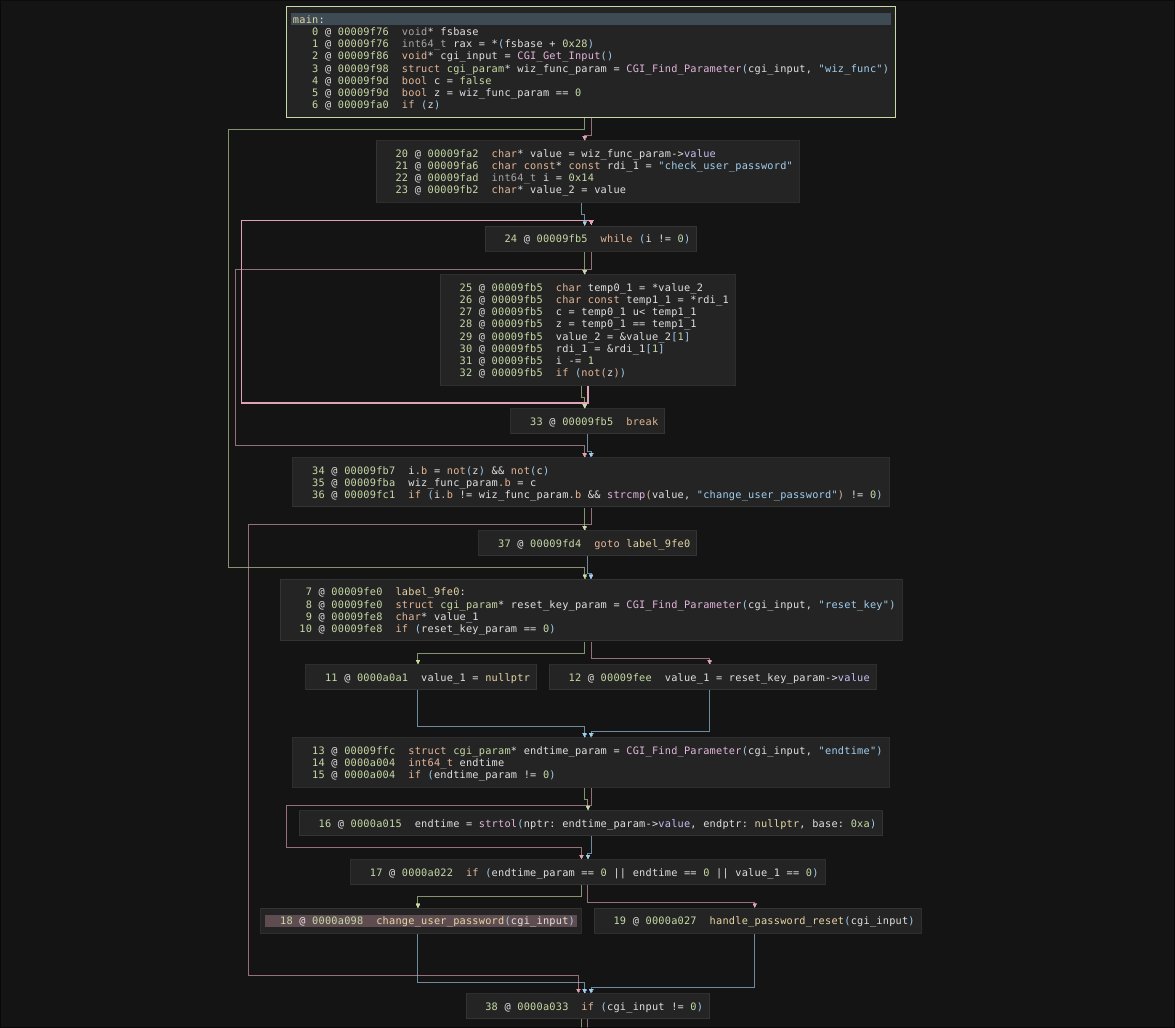
English
@SinSinology @InterruptLabs I'm seeing some advisories from what I think is the 2024 p2o, where mitm was presumably used
zerodayinitiative.com/advisories/ZDI…
English
@SinSinology @InterruptLabs Mitm is still in-scope for mobile, smart home etc categories right?
I didn't realise this change happened in 2024 though, even more frustrated I didn't notice now 🥴
English

@InterruptLabs @XploitBengineer banger blog Ben, as always!
small note about this part:
"the only categories that had this rule change were categories with Synology devices."
mitm, arp spoof, dns poison are out of scope for all targets since october 2024
English
Ben retweetet

I hear a high-profile Pwn2Own winner is fuming now that we've dropped a 0-day affecting their home setup. Perfect time to leverage that MITM access and ransack years' worth of bugs if you happen to be sitting in the right network 🙂
Interrupt Labs@InterruptLabs
Latest from our Labs - @XploitBengineer looks at how NAS vendors get TLS wrong, and why this matters. interruptlabs.co.uk/articles/when-…
English
Ben retweetet

Helloooo! BlackHoodie still has some spots for their training at DistrictCon.
The class will focus on reverse engineering and exploiting an integer overflow bug in libpng, with @pinkflawd
Sign up today 😊
blackhoodie.re/DistrictCon202…
English
I posted a short blog about how a Samsung GPU vulnerability (CVE-2025-21479) can be leveraged for an LPE on affected devices
xploitbengineer.github.io/CVE-2025-21479
English
Ben retweetet

@XploitBengineer Have you had a pint of the local Guinness (Murphys? Or something)?
English
@w1ntercoats @LinxzSec Good. The farming community wasn't ready for you yet.
English

Well….. I guess I don’t have to give up and become a farmer yet. Soz @XploitBengineer and @LinxzSec you are stuck with me for a bit longer 😂😂
TrendAI Zero Day Initiative@thezdi
English

absolute legend! Incredibly talented dude who is still very early on in his career, very proud!!!
@XploitBengineer
Also wouldn't be a p2o entry without our resident boss man too @munmap. Congratulations guys
TrendAI Zero Day Initiative@thezdi
Bang! Interrupt Labs successfully took over the #Samsung Galaxy 25 with 1 click. They remotely enabled the camera and location services, which has some frightening privacy implications. They head off to the disclosure room to explain how it works. #Pwn2Own
English
We did a thing!
TrendAI Zero Day Initiative@thezdi
Another big confirmation! Ben R. And Georgi G. of Interrupt Labs used an improper input validation bug to take over the Samsung Galaxy S25 - enabling the camera and location tracking in the process. They earn $50,000 and 5 Master of Pwn points. #Pwn2Own
English
@SinSinology Cheers mate! Glad to see your knocking over most of the Pwn2Own range again 🤙🏻
English



