Ben
189 posts
Ben
@XploitBengineer
Android Vulnerability Researcher, Pwn2Own 202{3, 5}
planet earth Katılım Nisan 2016
618 Takip Edilen1.1K Takipçiler
@evilsocket @IamAlch3mist I wonder if a CVE will be assigned for this
English

Pwn2Own 2026 Capacity Overflow, Hackers Drop 0-Days Solo awesomeagents.ai/news/pwn2own-b…
English
Ben retweetledi

Security researchers become trapped into an identity that they can’t escape, life seems purposeless, reality shifts and they realize they can’t bend like a tree in the wind. It turns out that intelligence isn’t the key to happiness.
For those that know. Chop wood, carry water.
L4ys@_L4ys
0days doesn't seem cool enough anymore. what should real hackers be doing now?
English
Ben retweetledi
📣New Android Vulnerability Researcher vacancy. Open to mid-level, senior and principal researchers.
interruptlabs.teamtailor.com/jobs/7668923-a…
English

@0x_shaq x.com/ScottyBauer1/s…
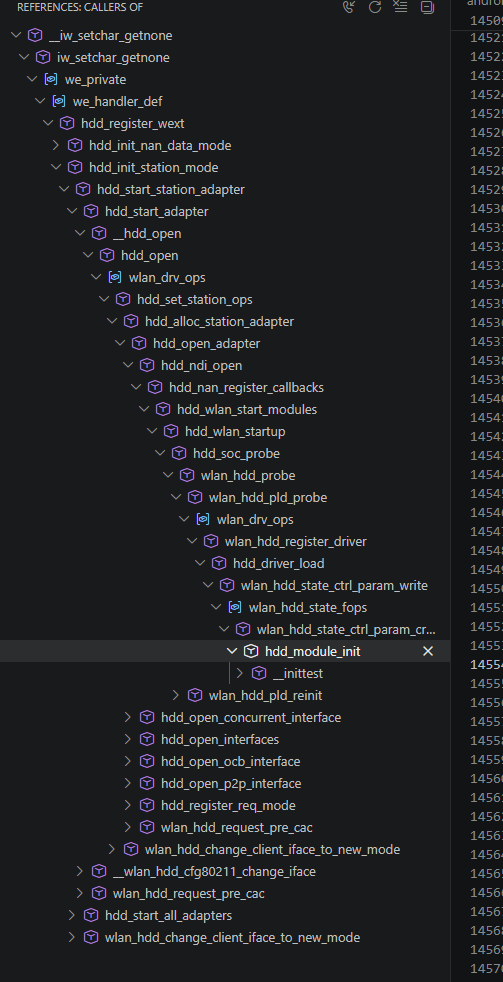
This was the exact driver that caused ^ that tweet. Glad real solutions were developed other than my whiteboard.
Scott Bauer@ScottyBauer1
Does anyone have a good tool to graph function call chains? Must run on Linux. I'm doing it by hand just need an easy way to link funcitons
English
Ben retweetledi

@boredpentester I have not had much success at all with LLMs for kernel exploitation either. I'm not sure what we're doing wrong 😬
English
@iBSparkes Unfortunately it's going the opposite way. Samsung has preemptively rolled out locked bootloaders globally as of ~August 2025 - apparently due to the new "Radio Equipment Directive"
English

I think — genuinely — the only hope for jailbreaking at the point is if the EU forces manufacturers to have unlocked bootloaders. It is deeply fucked up to me that you can buy a $1000 computer and are not allowed to install your own software on it.
sparkey@iBSparkes
“Semi-jailbreak” makes me immensely sad
English
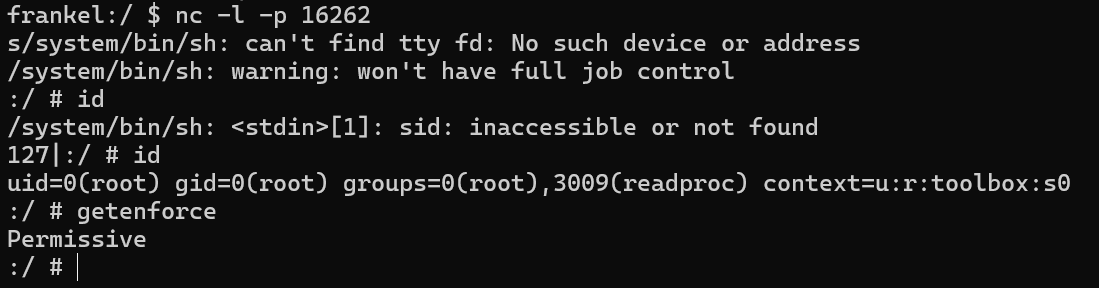
Professors have approximately zero free time. And yet. 👀
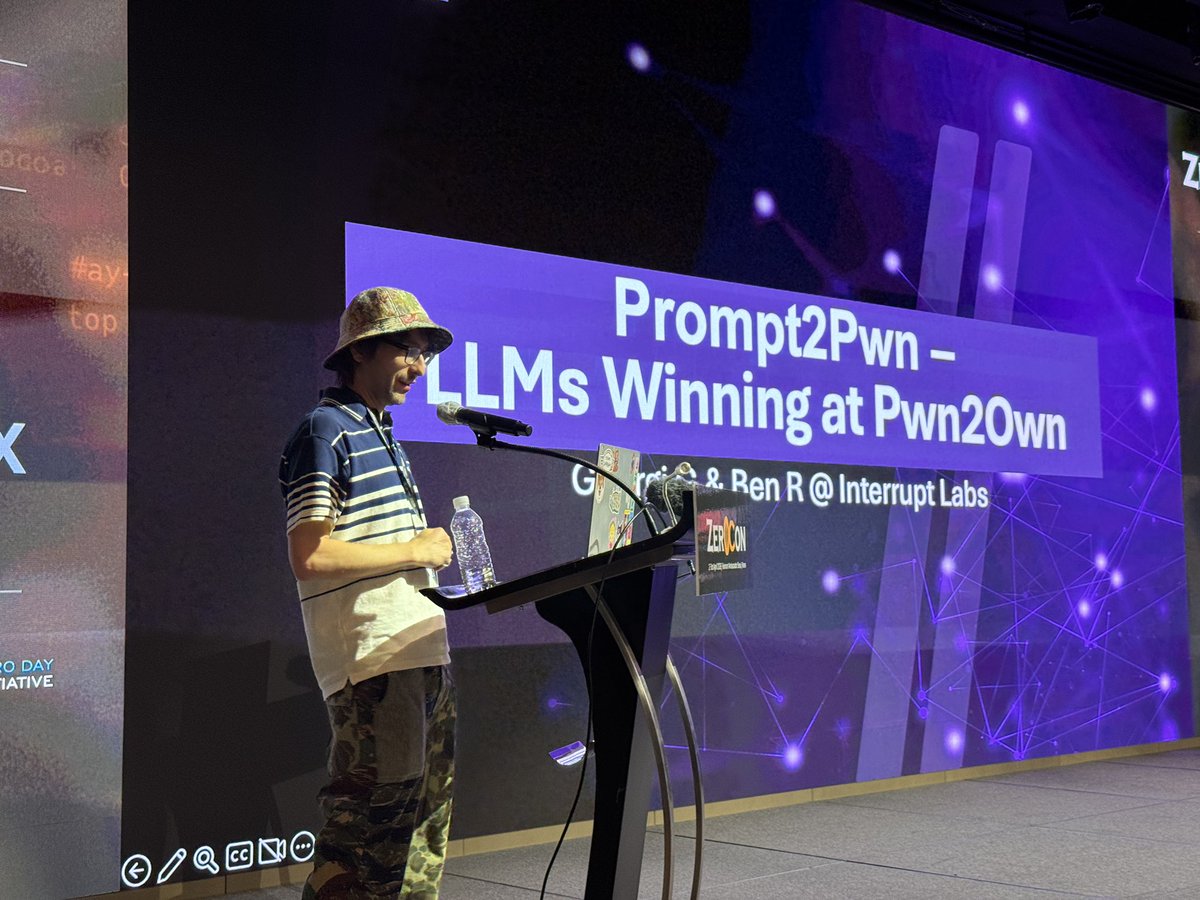
Turns out LLMs as super assistants make exploit dev manageable and fun again.
Pixel 10 root exploit (LPE) with an N-day. No public exploits exist for this thing.
Maybe I should teach a course on this. #LLM #ExploitDev

English
Ben retweetledi

Long overdue episode with the iOS avengers @s1guza @littlelailo @iBSparkes @jonpalmisc @hdemoff_ open.spotify.com/episode/7IyjVv…
English
Ben retweetledi
Ben retweetledi

After weeks of reverse engineering MediaTek's DA2 with @shomykohai, we finally figured out how the V6 exploit works. We decided to call it heapb8 ("heapbait")!
Technical writeup: blog.r0rt1z2.com/posts/exploiti…
PoC: github.com/shomykohai/pen…
English
@SinSinology @InterruptLabs It's a mystery, for sure.
Looks like you had a great time in Japan btw, solid work 💪🏻
English

@XploitBengineer @InterruptLabs you're right! that looks like mitm to me too!
i'm wrong in that case, now i got no idea when it is and when its not allowed
English
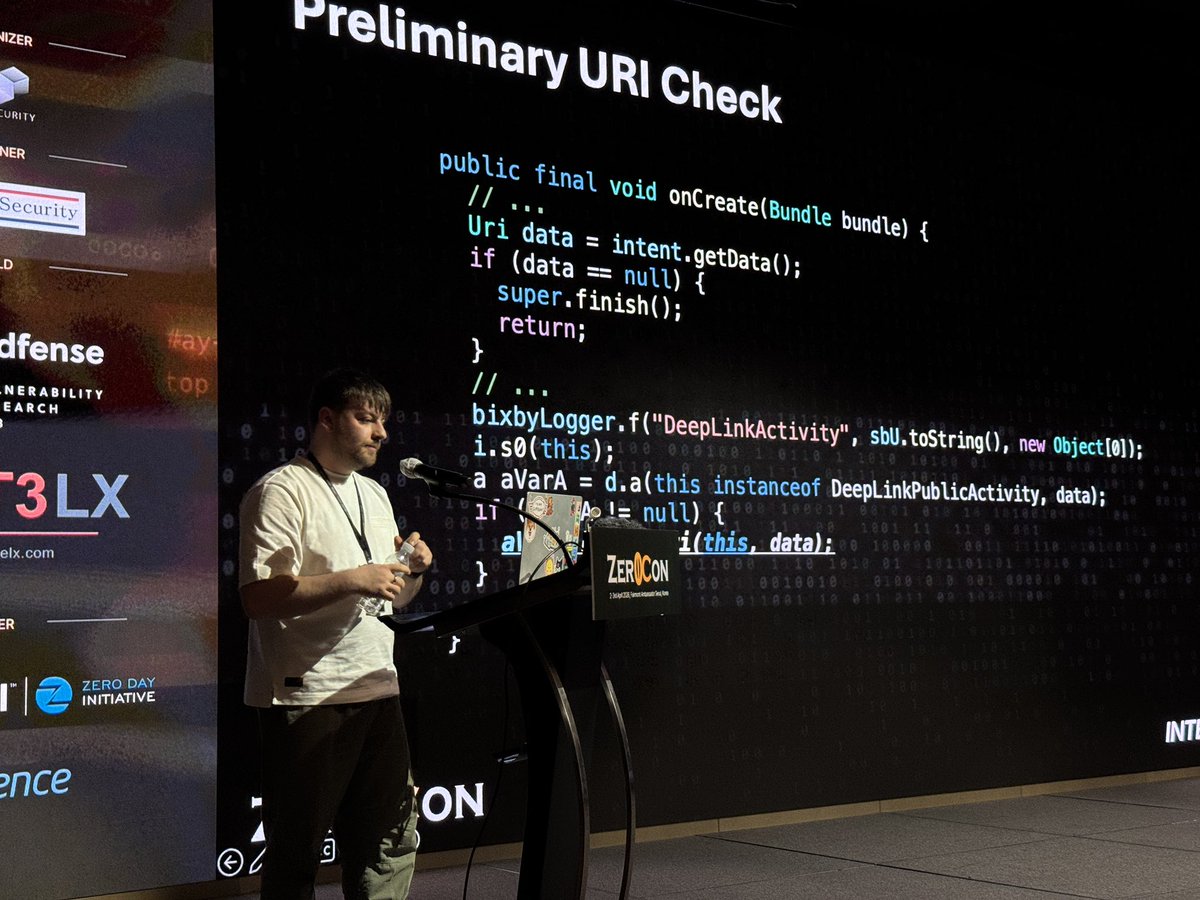
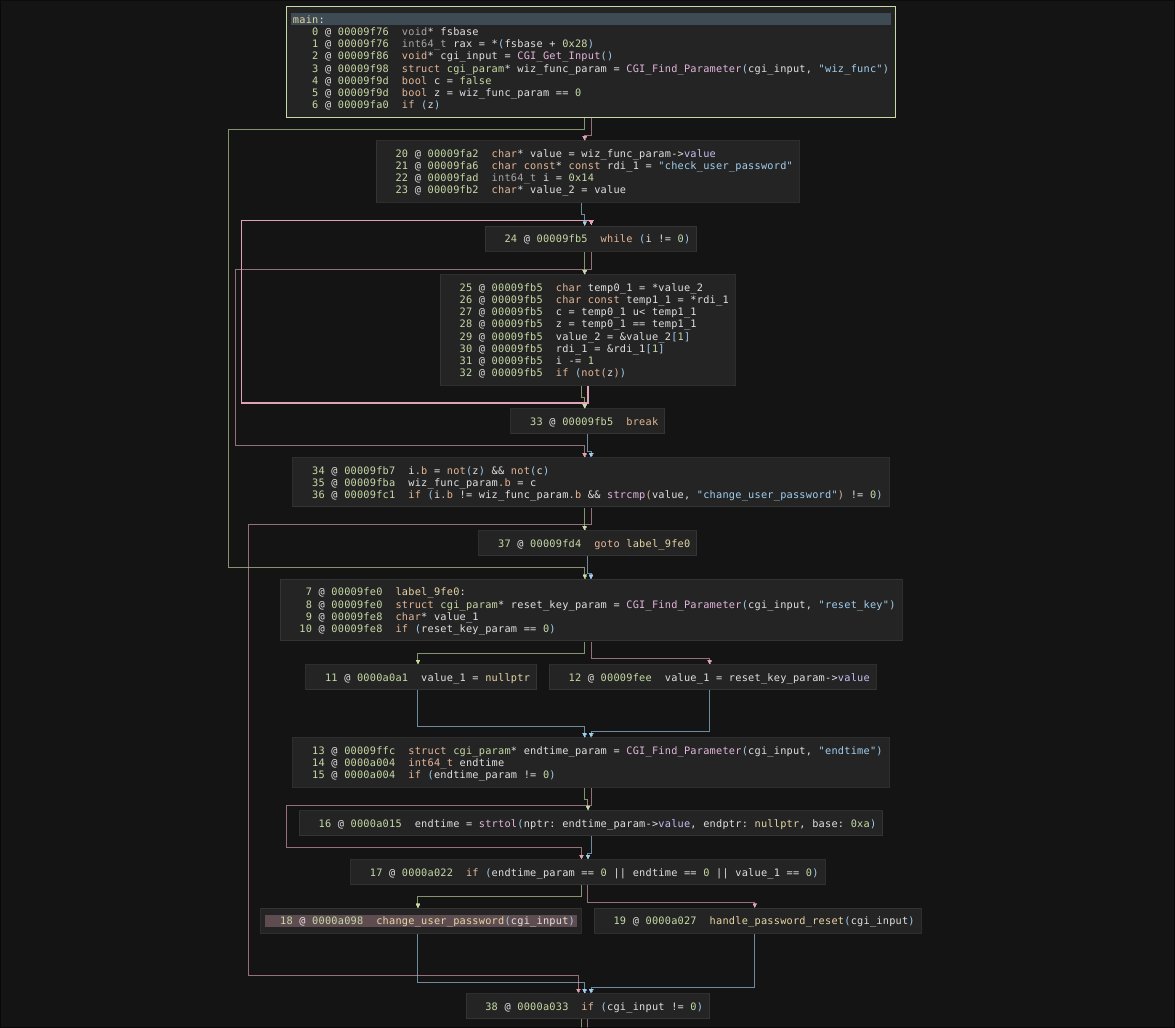
Latest from our Labs - @XploitBengineer looks at how NAS vendors get TLS wrong, and why this matters.
interruptlabs.co.uk/articles/when-…
English