arandomhacker
242 posts

arandomhacker
@arandomhacker
GWAPT, GPEN, GICSP, GRID, OSWP, OSCP, CISSP, OSEP #InfoSec #Hacker #Consultant Apolitical AF.
C-137 Beigetreten Ağustos 2020
318 Folgt76 Follower
arandomhacker retweetet
arandomhacker retweetet

The Mandiant Twitter account takeover could have happened a number of ways.
Some folks are giving the advice to turn on MFA to prevent ATO and of course that is a good idea always *but it's also possible that someone in Support at Twitter was bribed or compromised which allowed the attacker access to Mandiant's account*.
vx-underground@vxunderground
Today Mandiant had their Twitter account stolen. 2024 starting strong
English

Tackling #GRID from @SANSInstitute next - Love me some ICS/OT Protocols
English

Next Course Picked & Booked. Exciting to be taking SANS ISC515 this Q4 - Hopefully get the GRID certification nailed before End of Year @SANSInstitute
English
arandomhacker retweetet

Finally achieved #OSEP Certification. Thanks to @offsectraining for another fantastic course. The new mode of taking the training is amazing and the setup is excellent. Cant wait to continue to work towards #OSCE3
English

@EoinKeary @NoelAnderson_ @HMcEntee @gardainfo Scandanavian Taxes with North Korean infrastructure.......A great oul island
English

This is why @HMcEntee we have been crying out for more @gardainfo in the city center. Was only a matter of time. independent.ie/regionals/dubl…
English

@EoinKeary @rahimjina @ger_heffernan Preaching to the choir! Im going to one desert to get away from another, hotter desert! ill make sure to pop by the booth and say hello!
English

@rahimjina @EoinKeary @ger_heffernan Will any of you Gents be at BlackHat this year? I will be in Vegas from the 3rd - 12th - If so, be great to grab a Pint & catch up with you!
English
arandomhacker retweetet

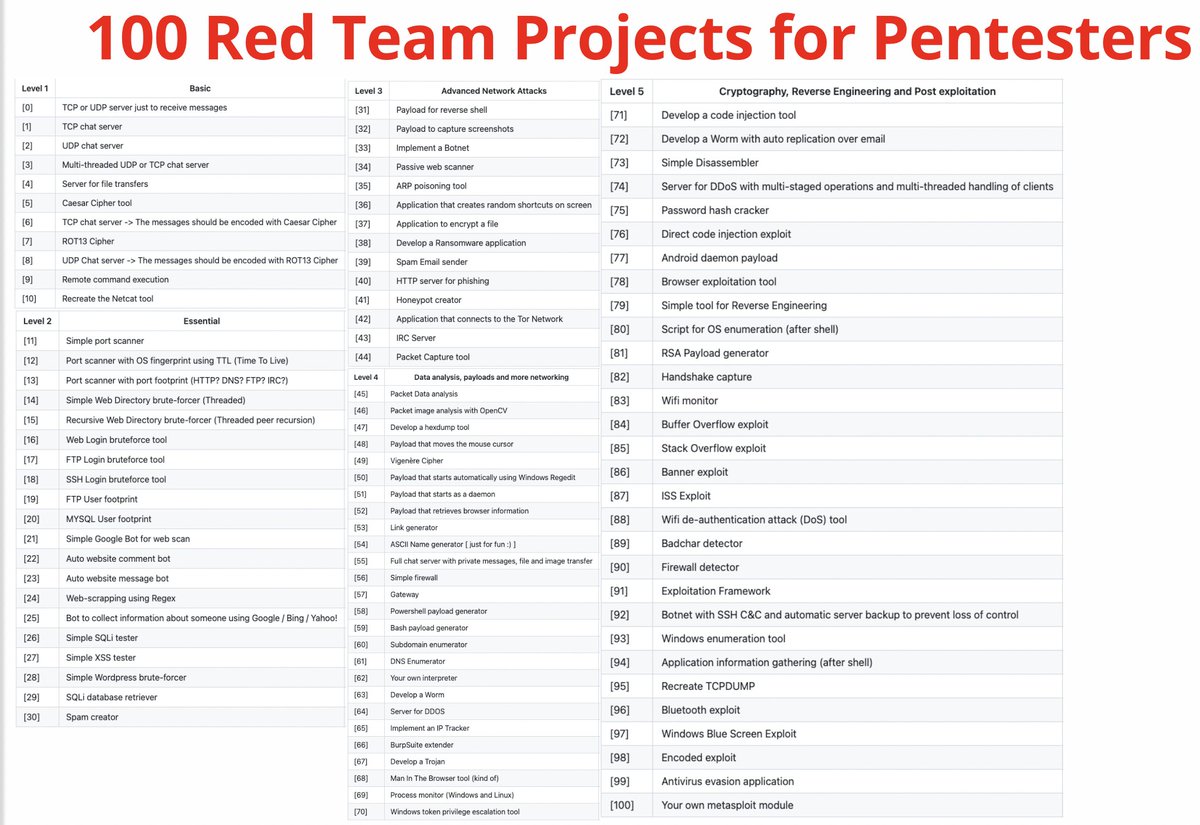
100 #redteam projects
A list of 100 projects that are worth a close look at the source code for someone who wants to become a high-level professional:
Advanced Network Attacks
Data analysis
Payloads
Cryptography
Reverse Engineering
Post exploitation
github.com/kurogai/100-re…
English
arandomhacker retweetet

@EoinKeary 5 years ago you'd be labelled a Conspiracy theorist Nut for saying this0!.......now you're just a Nut! 😅
English
arandomhacker retweetet
arandomhacker retweetet

Leaks and Breaches for OSINT
Long and detailed article about using data leaks in OSINT from Security by Accident blog.
@security-by-accident/leaks-and-breaches-for-osint-a7e3eb6bb56f" target="_blank" rel="nofollow noopener">medium.com/@security-by-a…
Surprisingly, there is no mention of Telegram channels with leaks, but still interesting.

English
arandomhacker retweetet
arandomhacker retweetet

Ask A Hacker: "Rachel, is it actually a big deal if I Google my name and my email address or phone number pop up. Why could that matter for someone like me?"
It can matter because many services you trust still use knowledge based authentication (KBA -- info like email address/phone number/date of birth) to verify identity when someone calls Customer Support.
Someone could pretend to be you, call Customer Support for a service you use, then leverage your public email address/phone number to "verify their identity" and make changes to your account and take it over. Here's an example:
English