Sabitlenmiş Tweet

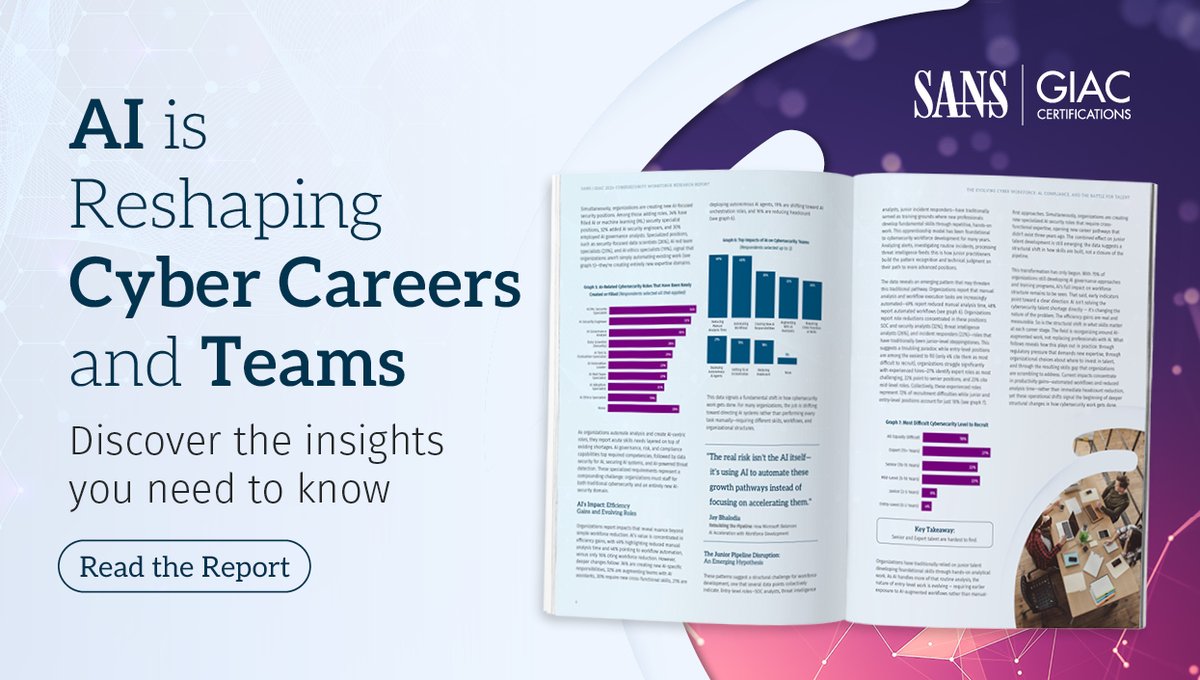
The threats are evolving. So is our leadership.
James Lyne is now CEO of @SANSInstitute. The next chapter starts now. 👏
Watch the full announcement → linkedin.com/feed/update/ur…
#SANSInstitute #Cybersecurity
English
SANS Institute
42.4K posts


@SANSInstitute
SANS is the most trusted and by far the largest source for information & cyber security training, certification and research in the world.