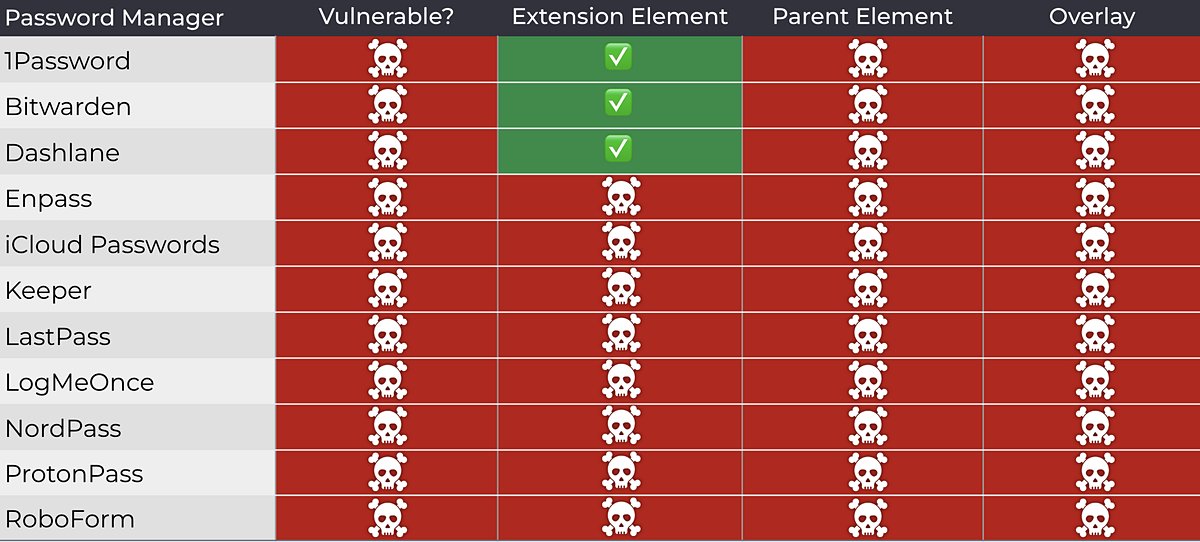
@CyberMedicsOrg If there have been any fixes from password manager vendors since publication, this is noted at the beginning of the research and the "Password Managers: Vulnerable & Fixed Versions" section is also updated, specifically "Fix Status (Updated: 11.9.2025)". Everything in these updated sections reflects the current situation as of today.
I will not correct any tables or conclusions from the original research. At most, only the above-mentioned sections will be updated.

English