Raf 👾 living his best life
15.4K posts


Raf 👾 living his best life
@raftomas
Detection Engineering | Signal-First SIEM Design | Lab-Tested AI Workflows
Italy Beigetreten Haziran 2021
1.4K Folgt565 Follower
Angehefteter Tweet
Raf 👾 living his best life retweetet

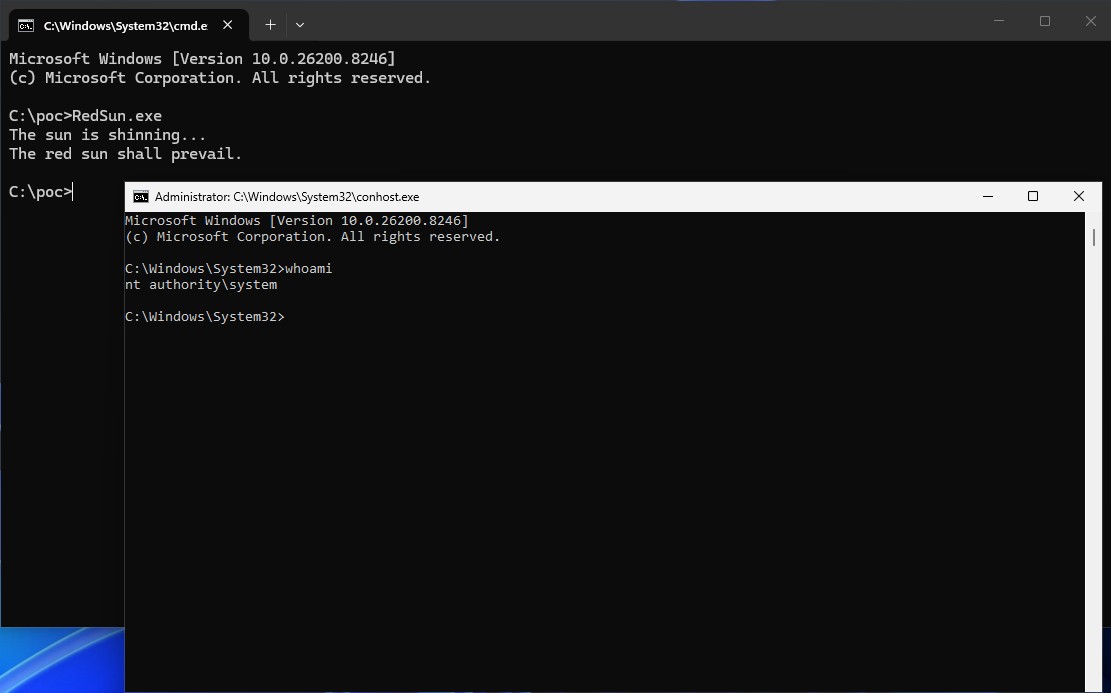
the Red Sun vulnerability is genuinely one of the funniest bugs i've seen in a while
Windows Defender finds a malicious file with a cloud tag and instead of quarantining or deleting it...
it helpfully rewrites the file back to its original location
the antivirus. protecting you. by restoring the malware.
the PoC abuses this to overwrite system files and escalate to admin privileges
the core idea is brilliant in the most embarrassing way possible
sometimes the best vulnerabilities aren't clever exploits
they're just Microsoft being Microsoft
English

Raf 👾 living his best life retweetet

🖥️🔥 Two inmates at an Ohio prison built a secret hacking operation from behind bars, using computers they were supposed to be recycling, they downloaded and sold porn in return for snacks, built a hacker toolkit with Kali Linux and password crackers, and created fake passes to move freely around the facility.
All from two secret computers they built from recycling scraps and hid in a ceiling...
Marion Correctional Institution in Ohio housed 2,500 inmates.. In 2014, the prison signed a deal with a recycling nonprofit called RET3 to have inmates disassemble old computers for parts.
Inmates Adam Johnston and Scott Spriggs had other plans. Instead of breaking the machines down, they rebuilt two fully functioning computers from the scraps.
Johnston hid the two PCs on plywood boards in the ceiling above a closet in a third-floor training room. He ran cables from the hidden machines directly into the prison's network switch.
To get the computers there, he loaded them onto a hygiene cart alongside soap and shampoo. He wheeled the cart 1,100 feet across the prison, past a corrections officer, through a metal detector, into an elevator, and up three floors.
Once connected, Johnston had full internet access and could remote into the hidden computers from any inmate terminal in the facility. He obtained a staff member's login credentials by shoulder surfing, watching him type his password.
That password hadn't been changed in years. The prison's systems didn't enforce password rotations, in violation of their own policy.
Using the stolen credentials, Johnston accessed DOTS, the state's offender tracking database. He browsed inmate records, searching for a young prisoner serving a long sentence whose identity he could steal.
He found Kyle Patrick. Johnston pulled Patrick's Social Security number and date of birth from the system, bypassing a security filter that was supposed to hide SSNs by simply adjusting the browser's view settings.
Johnston then applied for five credit and debit cards in Patrick's name. He texted his mother from prison using a free online messaging service and had her provide a neighbor's address across the street as the mailing address.
One card, a Visa debit from MetaBank, was approved. His mother received it in the mail, called him at the prison, and read him the card number, expiration date, and activation code over the phone.
Johnston activated the card from inside the prison using the hidden computers. Both the application and the activation were traced back to an Ohio state government IP address.
He wasn't done. Johnston had also pulled up a Bloomberg article detailing how to file fraudulent tax returns and have refunds wired to prepaid debit cards. That was his next move.
The computers were loaded with a full hacker's toolkit: Kali Linux, Wireshark, Nmap, password crackers like Cain and THC Hydra, VPN software, the Tor browser, proxy tools, and encryption software. Investigators also found articles on making homemade drugs, explosives, and fake credit cards.
Johnston used DOTS to create fake passes, giving inmates unauthorized access to restricted areas of the prison. He also downloaded pornography onto thumb drives that another inmate sold to other prisoners for commissary items.
The scheme only unraveled because the prison upgraded its web filtering software. In early July 2015, the new Websense system flagged Canterbury's credentials being used for three straight hours on a Friday, a day Canterbury didn't work.
More alerts followed on Saturday and the following Monday. IT flagged the activity to the warden. Everyone suspected an inmate was involved. Nobody called law enforcement.
The prison's IT specialist, Gene Brady, was told exactly which network port the rogue computer was plugged into. He misread the email and checked port 10 instead of port 16. It took him three days to realize his mistake.
When Brady finally traced the cable into the ceiling and found the two hidden computers on July 27, he brought two inmates along to help and had them pull the computers down, contaminating the crime scene.
He then emailed the warden: "What do you want me to do with the PCs?" The warden admitted he knew illegal activity was occurring but had no answer for why he never reported it to law enforcement.
The state highway patrol trooper assigned to investigate crimes at the prison literally shared an office with the prison's own investigator. Neither one was informed.
It wasn't until August 7, over a month after the first alert, that anyone reported the incident to the Inspector General or law enforcement. And only because an outside IT security officer told them they were required to.
After the discovery, inmates immediately began wiping other prison computers with CCleaner to destroy evidence. Investigators later found the cleaning software had been run at least 10 times in two days, while inmates still had unsupervised access.
Four inmates were transferred to separate prisons and placed in segregation with their phone access blocked. Johnston simply used another inmate's PIN to call his mother five more times anyway.
When investigators finally seized computers across the prison, they pulled 308 machines. Of those, 291 had no inventory tags. Brady had been swapping recycling-bound computers into the prison network for years without documenting any of it.
The investigation uncovered a cascade of failures: no password enforcement, no IT inventory, no crime scene protection, no reporting of illegal activity, and years of unsupervised inmate access to computers, parts, cables, and network infrastructure.
The warden resigned.




English
Raf 👾 living his best life retweetet
Raf 👾 living his best life retweetet
Raf 👾 living his best life retweetet

Take-Two Interactive saw its stock value rise by more than one billion dollars following a data leak from Rockstar Games.
Hackers stole internal data and demanded a ransom payment.
When no one paid they released the information publicly for free.
Instead of hurting the company the leaked files showed how profitable the business really is and gave investors extra confidence
Rare case where a leak backfired on the hackers and actually helped the company


English
Raf 👾 living his best life retweetet

Still thinking about the Anthropic recs where step #1 is the equivalent of:
“If you’re homeless, just BUY a HOUSE????”
Honestly, “patch every exploitable vuln immediately” is like toddler level strategic thinking. Let them eat cake. Baby’s first seceng job.
English
Raf 👾 living his best life retweetet

These takes are weird when the industry as a whole has a fairly good understanding of how organizations actually get compromised.
"Point AI agents at your own code and find the vulnerabilities before attackers do. That's Priority Action 1 in the briefing released today from the Cloud Security Alliance."
It wouldn't be ensure MFA?(BEC is still loses people the most money)
Conditional access? No device code/strong auth?
Ensure EDR is on ALL endpoints?
Reduce external attack surface?
Understand risks of file transfer/edge appliance software?
Strong protected backups??
x.com/robtlee/status…
English

@nas_bench this is 🔥🔥🔥 great platform
sigma.nasbench.dev/logsources
English
Raf 👾 living his best life retweetet