Abhishek Shukla
1.6K posts


Abhishek Shukla
@thetechnofeak
Cybersecurity engineer . learning Blockchain Security . Opinions are my own ☕️ | Open for Discussions




e-ink is so good for being able to enjoy the sun without sacrificing your eyes







⚠️ALERT: $AAVE is now down -19% today after a $292M Kelp DAO rsETH exploit triggered a full-blown liquidity crisis. Aave's ETH pool just hit 100% utilization. That means one thing: there's almost no ETH left to withdraw. Here's what happened: Attacker drained 116,500 rsETH ($292M) from Kelp DAO's LayerZero bridge He then deposited the stolen rsETH as collateral on Aave V3 to borrow ~$236M in WETH. Because the rsETH is now unbacked, those positions are unliquidatable. Aave is now stuck with ~$280M in bad debt it cannot recover. Panic withdrawals have followed: $5.4 BILLION in $ETH outflows, with Justin Sun pulling 65,584 ETH ($154M) alone. ETH utilization has maxed out at 100%, which means there's almost no ETH left to withdraw. This is the FIRST real-world test of Aave's Umbrella safety module & the BIGGEST DeFi exploit of 2026. This is a developing story.





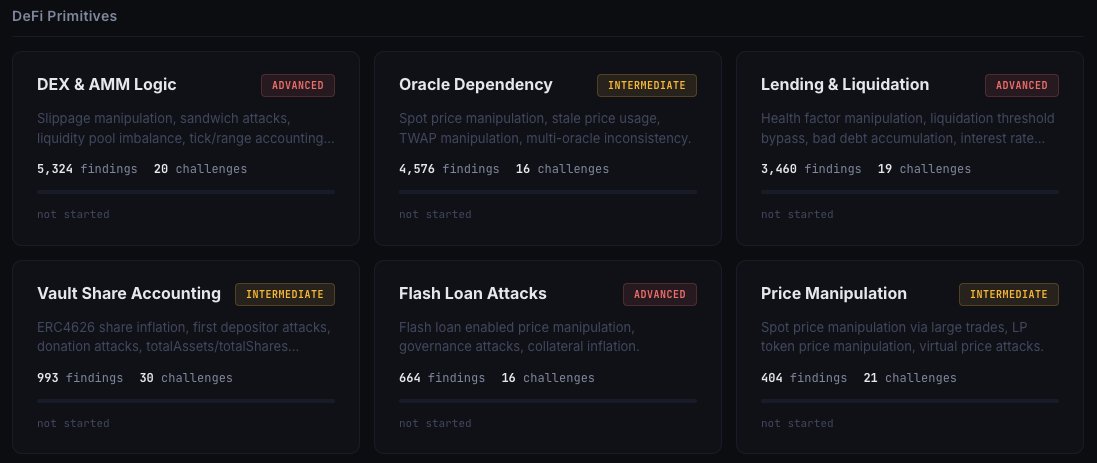
Recently read about the idea of thinking about smart contracts in terms of state machines, the concept felt a bit confusing at first. Then I stumbled upon a blog that made it click. It seems like a great way to better understand the intricacies of a system overall. Will definitely read more about this. > For context — I am into Web2 security full-time, working across SIEM, DevSecOps, detection engineering, SOC operations, and related areas. In the meantime, I am learning Web3 security because I want to pivot into Web3 as soon as I can. My goal is to do at least 40 hours of code reading every week, no matter what else I am involved in. I do believe Web3 security is a niche I want to see myself in .