
NZ Defence Industry Strategy just dropped: defence.govt.nz/assets/Defence…
English
F.A.
179 posts


@RecedingLights
Still not sure whose views mine are.










@McGrewSecurity I think it would be fun to see just how much opportunity is created per cyber criminal. It’s the digital war on drugs, lots of people profiteering. And none of them win by solving the actual problem.



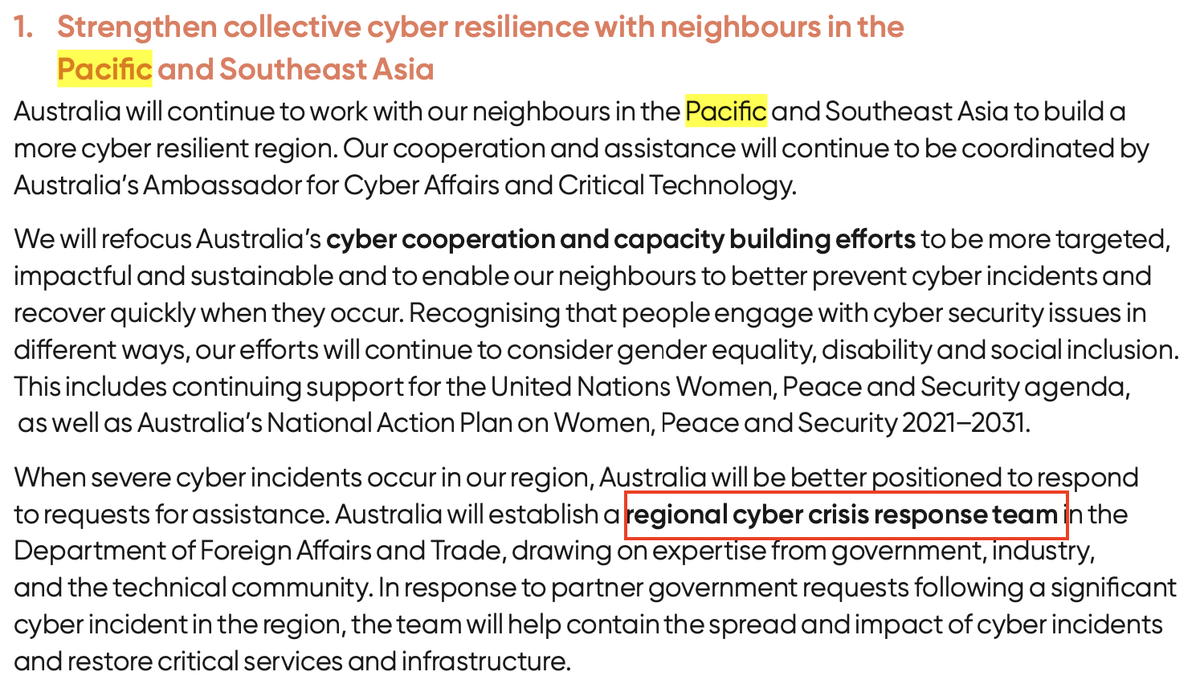

Story: the Pacific Islands Forum Secretariat targeted by hackers linked to the Chinese government. Australia has sent teams of cyber experts to Suva this year to help abc.net.au/news/2024-09-1…






