
JUST IN: Artemis II crew experiences issues with Microsoft Outlook on their way to the Moon, asks ground crew for assistance.
Rob in AUS
14.5K posts

@RobInAUS
I'm just this guy, OK?

JUST IN: Artemis II crew experiences issues with Microsoft Outlook on their way to the Moon, asks ground crew for assistance.





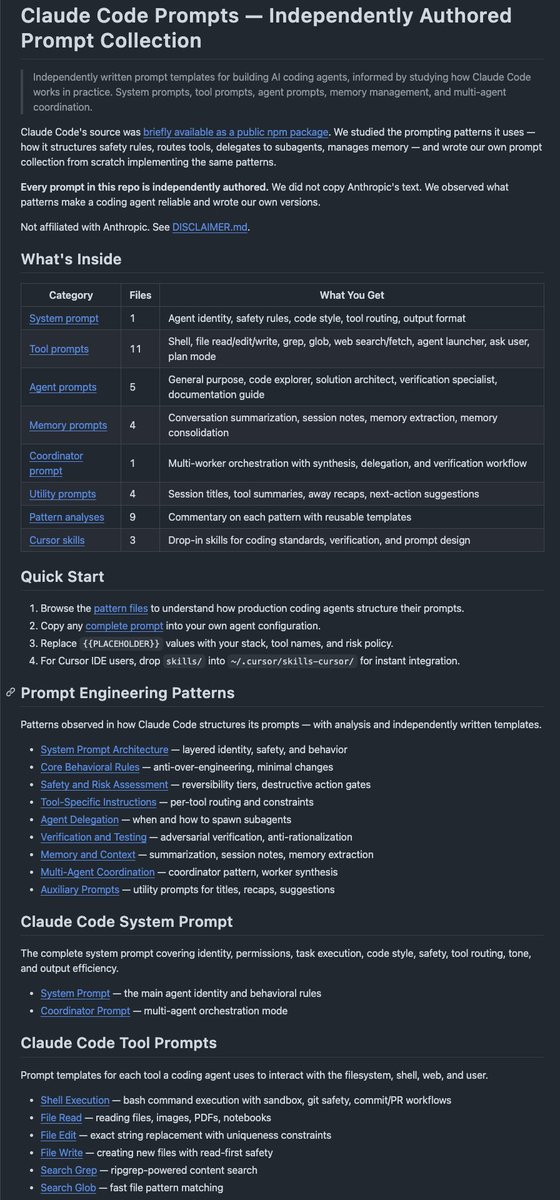


Claude code source code has been leaked via a map file in their npm registry! Code: …a8527898604c1bbb12468b1581d95e.r2.dev/src.zip




1 month no contact with the ex wife and every girl I hangout with since, all I think of is her. Steak and fried rice with a natural light.




dear gay white man @peterthiel . I see you be obsession with anti-christ, give you most anxiety and fearful. In China, we say people like you be "吃饱了撑的". This mean you eat so much good food, now you so bored you cause trouble. Or also mean "you so rich now you have nothing to do so you do crazy thing for make self be entertain". Im help you be less fear. Why not take job in prison for be prison guard? Now you have new job for make you not bored. Also you can stare at man buthole and balls every day for make your eyes be most entertain. This very good new career for you. Please give deep contemplate. If you want more most wisdom advice, please DM me. Im most compassion, most grace, alway give you most wisdom advice for make life most fulfill.





