Tweet fijado
SMJS
706 posts

SMJS
@SMJSGaming
23 | I modify games in my free time. Discord: @smjs
Se unió Şubat 2019
45 Siguiendo558 Seguidores

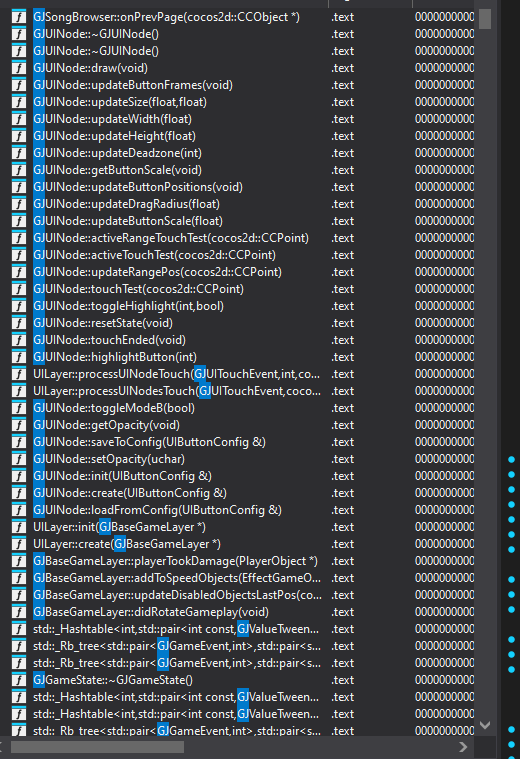
Fun fact about #GeometryDash . In RobTop's eyes it's still called GeometryJump since all endpoints and most methods are prefixed with GJ to this day.
English

@outstreamed_ @BeatGTO Just make it case sensitive and problem solved as long as camelCase and TitleCase is used correctly (it is)
English

@BeatGTO @SMJSGaming 1. anything that isnt gj as in geometry jump will be replaced too
2. whats the point
English

@SMJSGaming hey so i wanna message u ab something with this but your dms are closed
English

#GeometryDash A data breach was discovered in the GD servers which was likely already known by malicious individuals. This means that your email, IP address, hashed password, messages, private levels and much more has likely been dumped somewhere.
English
@SMJSGaming crazy how up until 2.2, logins were being sent over unencrypted HTTP and password were in PLAINTEXT, UNHASHED
English

@SMJSGaming Approximately how long has this exploit been a thing
English

@SMJSGaming You'd think something would already be known or found by someone else before, but you'd probably be surprised how many times that's not true, even for simple stuff.
Do we know if any incident response whatsoever been done on this? What makes you say it was likely already known?
English

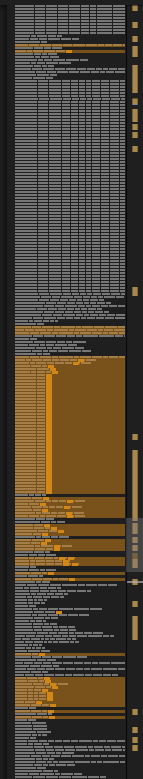
@luckylakie_real An overview of the amount of lines (1 line is 1 DB table) where the column userIP exists on (126 in total)
English

@luckylakie_real Well then for you it might be less of a problem but for every action taken with the server the IPv4 associated with the request was stored in the database.
English

@SMJSGaming Alright so it genuinely is likely lost forever
English

Regarding the recent post I made
while I had full access to the DB I looked for Element 111 Rg. It's not there #GeometryDash
English

@WinterDHX @Restoration_Uni Nah that's unrelated
they just bruteforce or use leaked passwords from other breaches
English

@SMJSGaming @Restoration_Uni Guess that explain all thoses hacks that happen in the mast 2 weeks by thoses teamtuff cockroaches
English

@ThophGD 1. Yes, if the password complexity in GD is not safe enough to protect against a brute force without restrictions like those imposed on the GD servers. Which is the case now that they might be available locally.
2. Mostly change your pass
3. Sell your data, leak private stuff etc
English

@SMJSGaming Would be nice if you or someone else answered those questions to make people feel safer!
1. Are our GD accounts in risk of getting hacked?
2. Is there anything that we should do? (changing password etc...)
3. What could people do with the dumped info?
English

@UncannyInfinity @cvsilly_ Yes that's the danger
this no longer limits them from brute forcing it.
English

@cvsilly_ @SMJSGaming but if your password is simple then it's still a problem. they now can guess a password locally
English

@jojo989_A7_ Yes, all passwords were hashed with bcrypt. A proven 1 way encryption
English

@SMJSGaming only the hashed password right? i mean stupid ahh question but anyways
English

@SMJSGaming is this how so many people are being hacked recently then
English

@SMJSGaming is this breach recent? cuz i changed my everything like a week ago
English

@GreenRedGD @wezakune Not really, worst case scenario he fucks it up and accidentally makes it not work properly. But the code is not so legacy that it's impossible to add totp. Infact I've already created an example before
English

@wezakune @SMJSGaming The problem with this is that RobTop is stuck with code from a few years ago, so adding a modern security system like 2FA can be very dangerous.
English

@SMJSGaming knowing robtop the hashes in question are sha-1 without salt.. gulp
English


