
“Transhumanism: The End Game” Short clip of my speech at the ‘Better Way Conference’ held by the World Council for Health earlier this year.
Nathan Petty
103.2K posts


“Transhumanism: The End Game” Short clip of my speech at the ‘Better Way Conference’ held by the World Council for Health earlier this year.

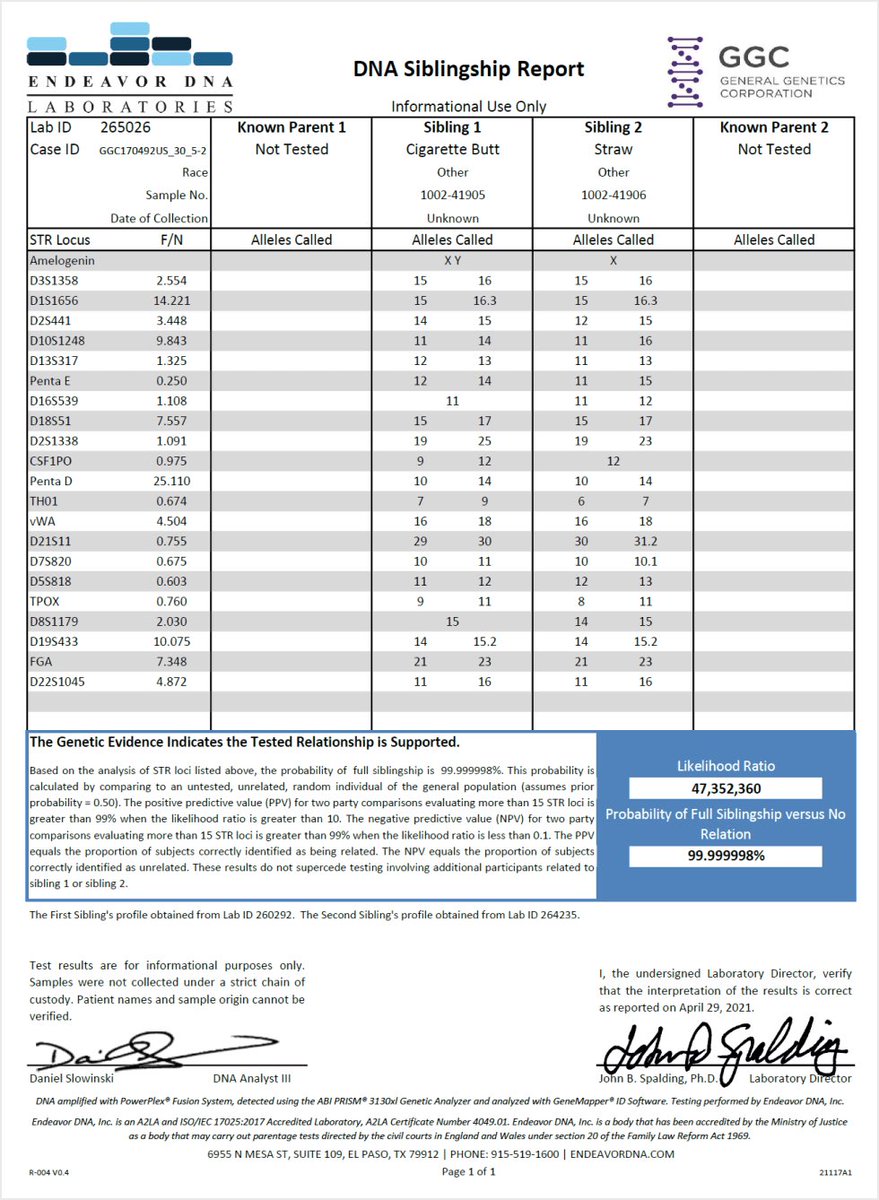


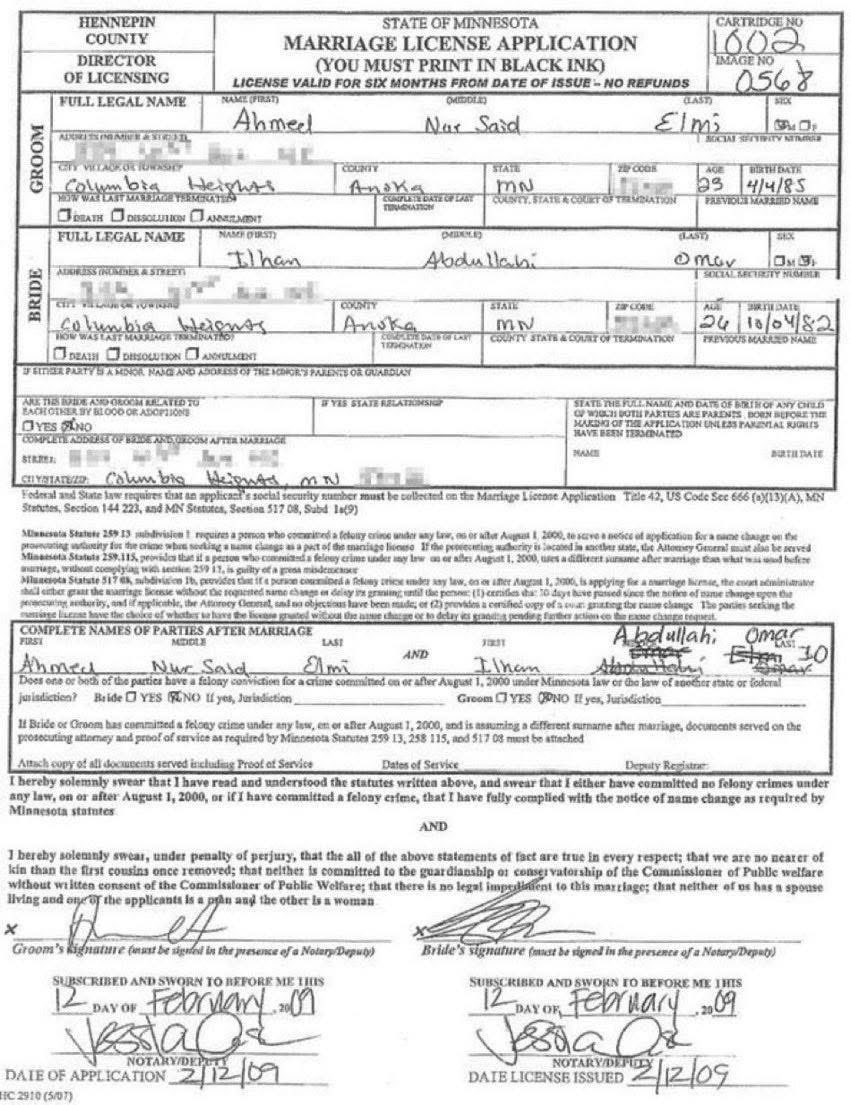

This is absolutely insane Journalist Angela Rose investigates Minnesota Rep Ilhan Omar’s consulting headquarters who claims to manage $60 billion in assets She goes into the building, walks every floor They DO NOT EXIST. (Holy Sh*t) “We are going to be infiltrating Ilhan Omar's sketchy consulting headquarters that claims that they have $60 billion in assets under their management. Yet they are located out of a co-working place called WeWork. This company is called Rose Lake Capital and it is co-owned by Ilhan Omar's husband Timothy Manette. And similar to the winery in 2023, it made up to $51,000 and it had a sudden and very suspicious increase in net worth up to $30 million in 2024” “I walked by every single office in this building and everyone has their logos proudly displayed on the wall. I asked around for Rose Lake Capital and people were not familiar with it. I looked at every logo and Rose Lake Capital did not have an office here.”


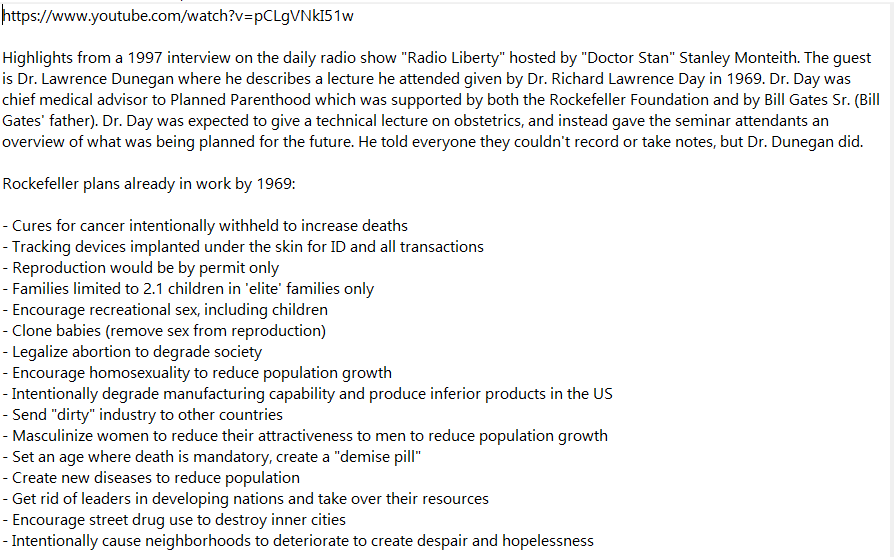





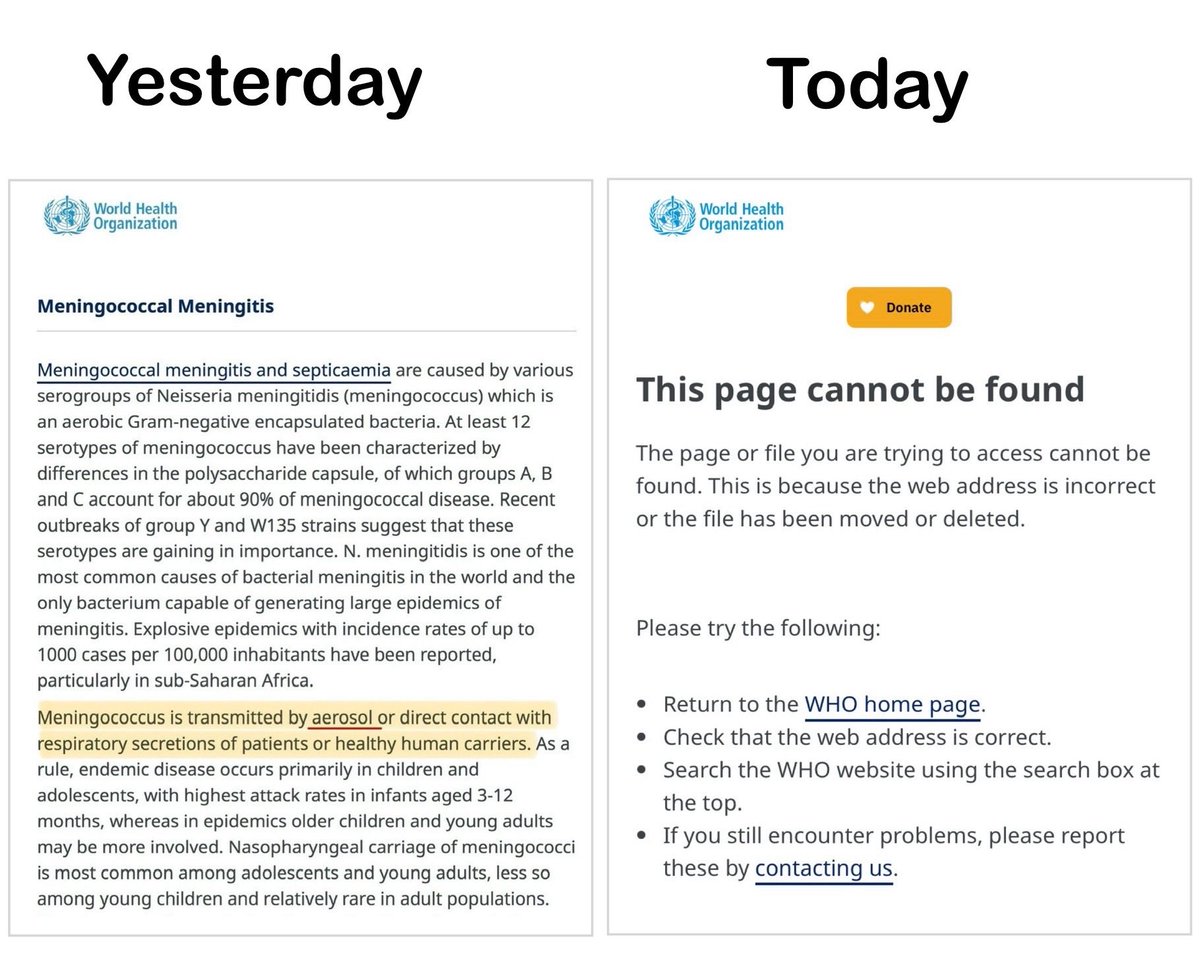
MENINGITIS TRANSMISSION Below is the UK Green Book & WHO info about transmission of the meningococcus bacteria which is responsible for the current Meningitis outbreak in Kent. Note use of the word “AEROSOL” in both. 🔗 assets.publishing.service.gov.uk/media/6849adb8… 🔗 who.int/teams/health-p…

I prosecuted the Proud Boys and the Oath Keepers, and then Donald Trump himself. One week after he took office again, he fired me. Now I’m running for Congress to defend our democracy and restore the rule of law.

You can watch the full video here 👇🏼 youtu.be/Im482k_at1g?si…


