Tweet épinglé

@albinowax Had any interesting ideas for security research ??? currently going after ai models , looking for any ideas under client or server side :)
English
ctx
662 posts


@_fxstack
ctfプレイヤー @CTFtime 🇯🇵 team | (wanna-be)zeroday security researcher | (wanna-be) security engineer












There goes the first one 🥳

Is there any chance for CSRF? 🤔 Test it out live at: pwnbox.xyz


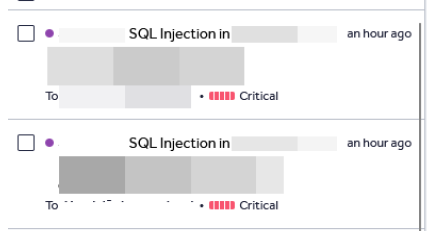
0day on telegram 👀