Grant H
1.2K posts


Grant H
@Digital_Cold
Mobile security researcher. Previously @Qualcomm product security. @UF Ph.D, @UCF B.S. Opinions my own https://t.co/VKTGUksQFd 🦋: @digitalcold


CTF is cooked blog.krauq.com/post/ctf-is-dy…

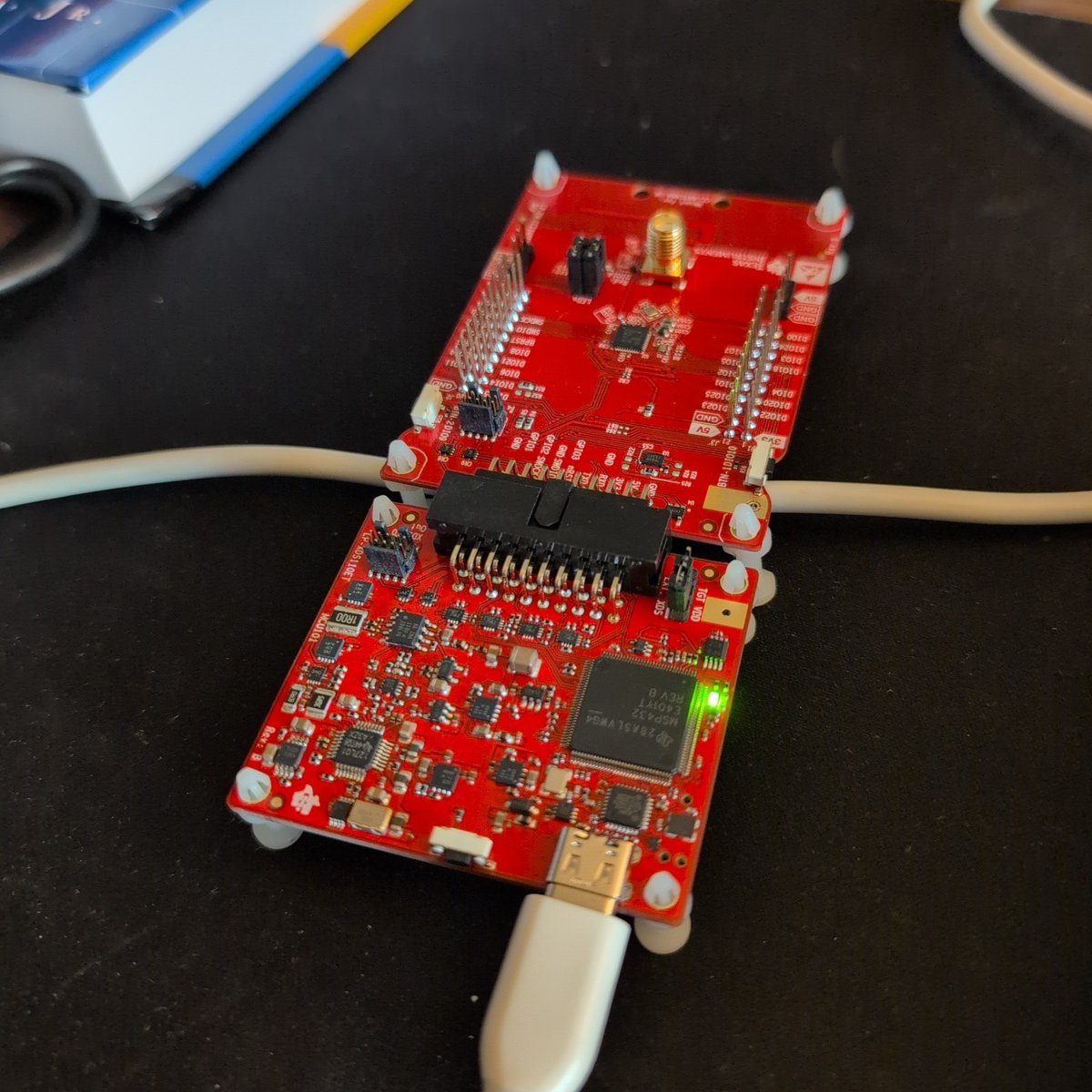
🚨 New advisory was just published! A critical vulnerability in UNISOC modem firmware allows one User Equipment (UE) to remotely attack another over the cellular network. By sending specially crafted malformed SDP within SIP signaling messages, an attacker can trigger memory corruption in the target modem, potentially leading to remote execution of arbitrary native code on the victim device: ssd-disclosure.com/unisoc-t612-rc…


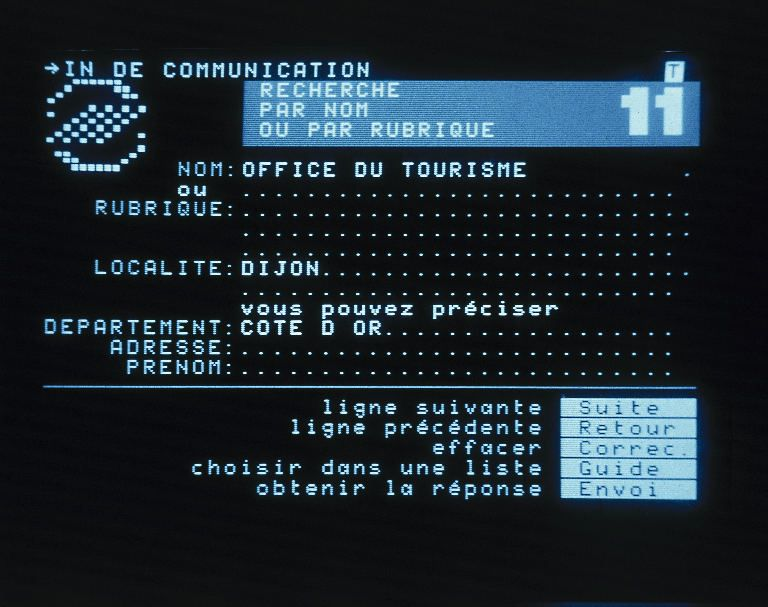
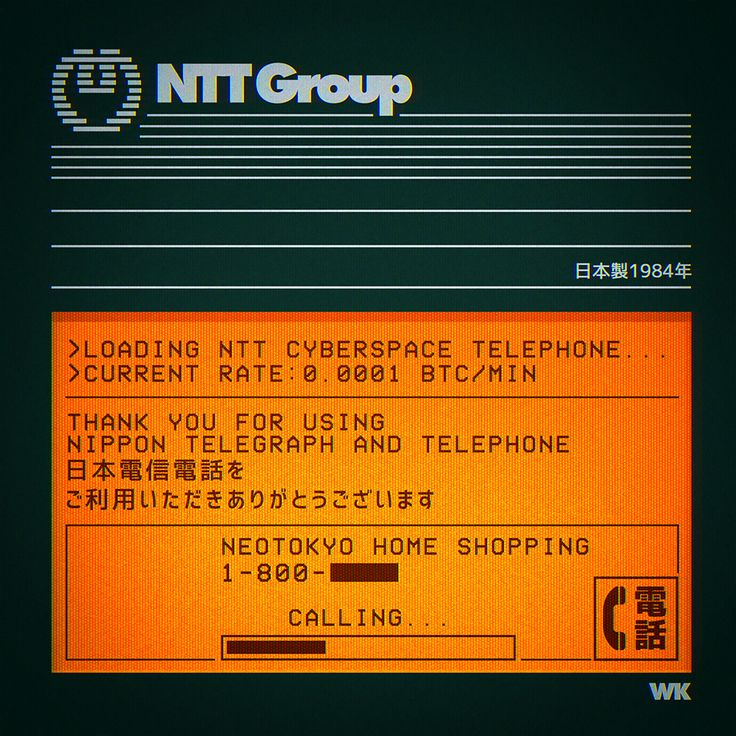
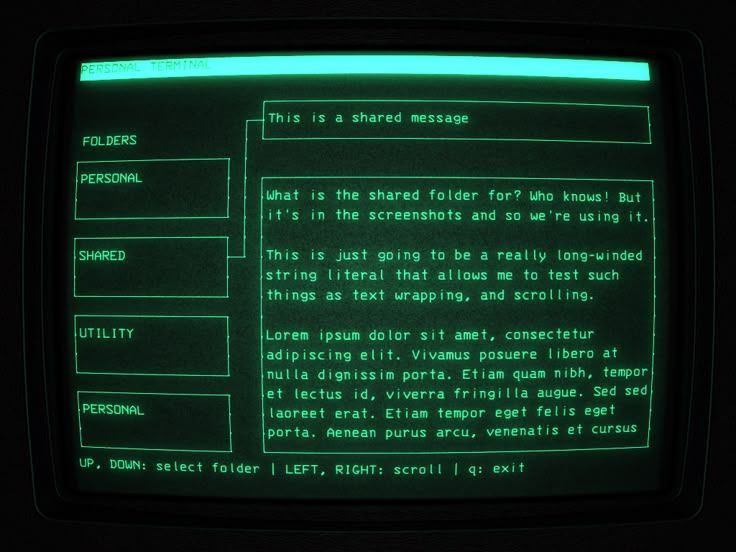
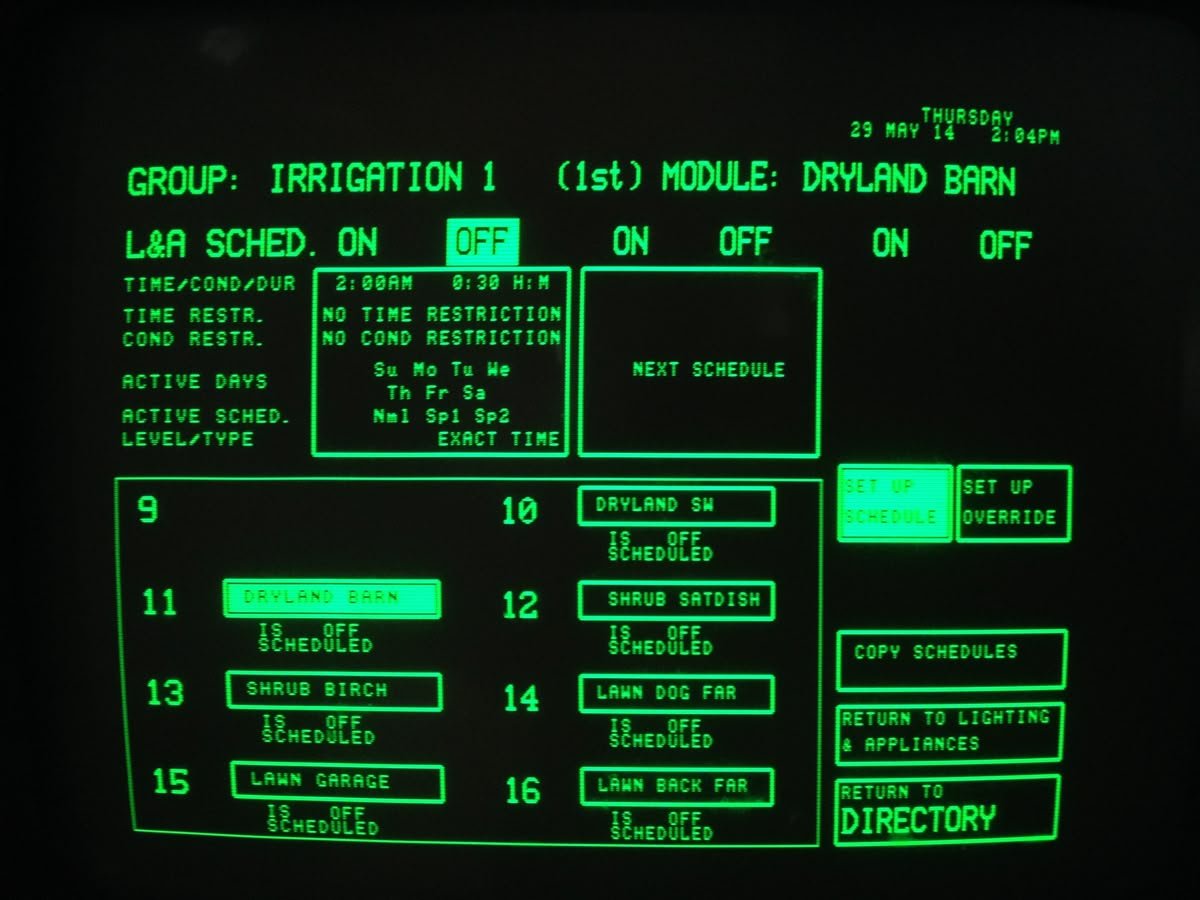
In an alternate timeline we’d be using Evangelion GUI designs rather than CLIs

Do LLMs actually help hackers reverse engineer and understand the software they want to exploit? We ran the first fine-grained human study of LLMs + reverse engineering. To appear at NDSS 2026. Interested? Some quick findings in 🧵👇 Paper: zionbasque.com/files/papers/d…



Qualcomm NPU Windows driver release notes


It's time to binge watch this masterpiece again.


The Secret Service dismantled a network of more than 300 SIM servers and 100,000 SIM cards in the New York-area that were capable of crippling telecom systems and carrying out anonymous telephonic attacks, disrupting the threat before world leaders arrived for the UN General Assembly. 📰 Read more about this at secretservice.gov/newsroom/relea…