Aly
1.6K posts


Aly
@DixieCheer
Bachelor of Science in General Management. Technophile. Always learning.

83% of Americans support voter ID. Pass the SAVE Act. Bill summary: - Mandates voter ID - Requires proof of US citizenship for voter registration - Requires states to verify citizenship - Mandates removal of non-citizens from voter rolls - Directs use of federal/state databases (DHS, SSA, etc.) for verification - Imposes penalties (incl. criminal) on officials who register voters without citizenship proof






And finally, a video recorded with GoPro cameras of the Islamic State assault in the capital of Niger. Grim is an understatement, the sheer size of IS's contingent making it to the airport, the destruction, the freedom of movement. We have barely started 2026. #Niger #Niamey



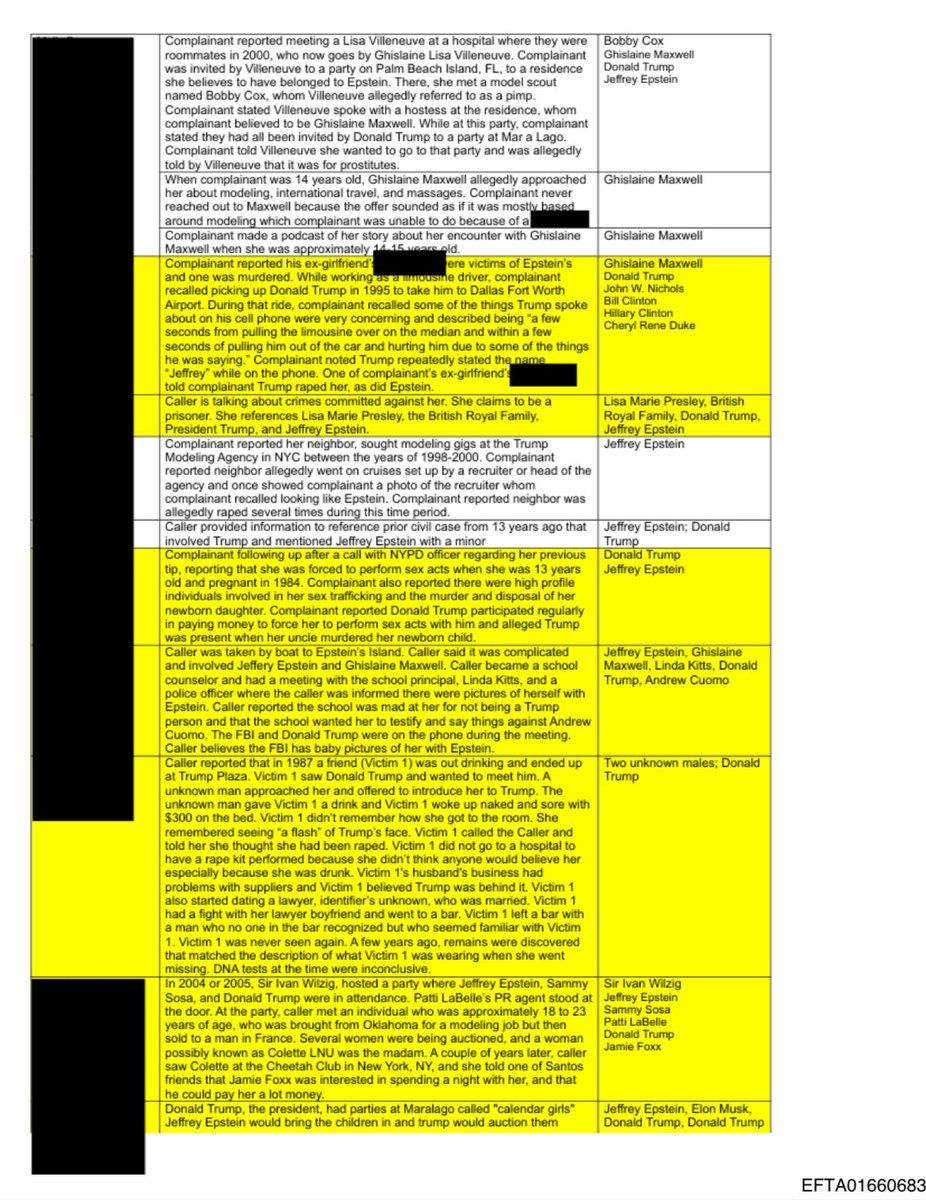
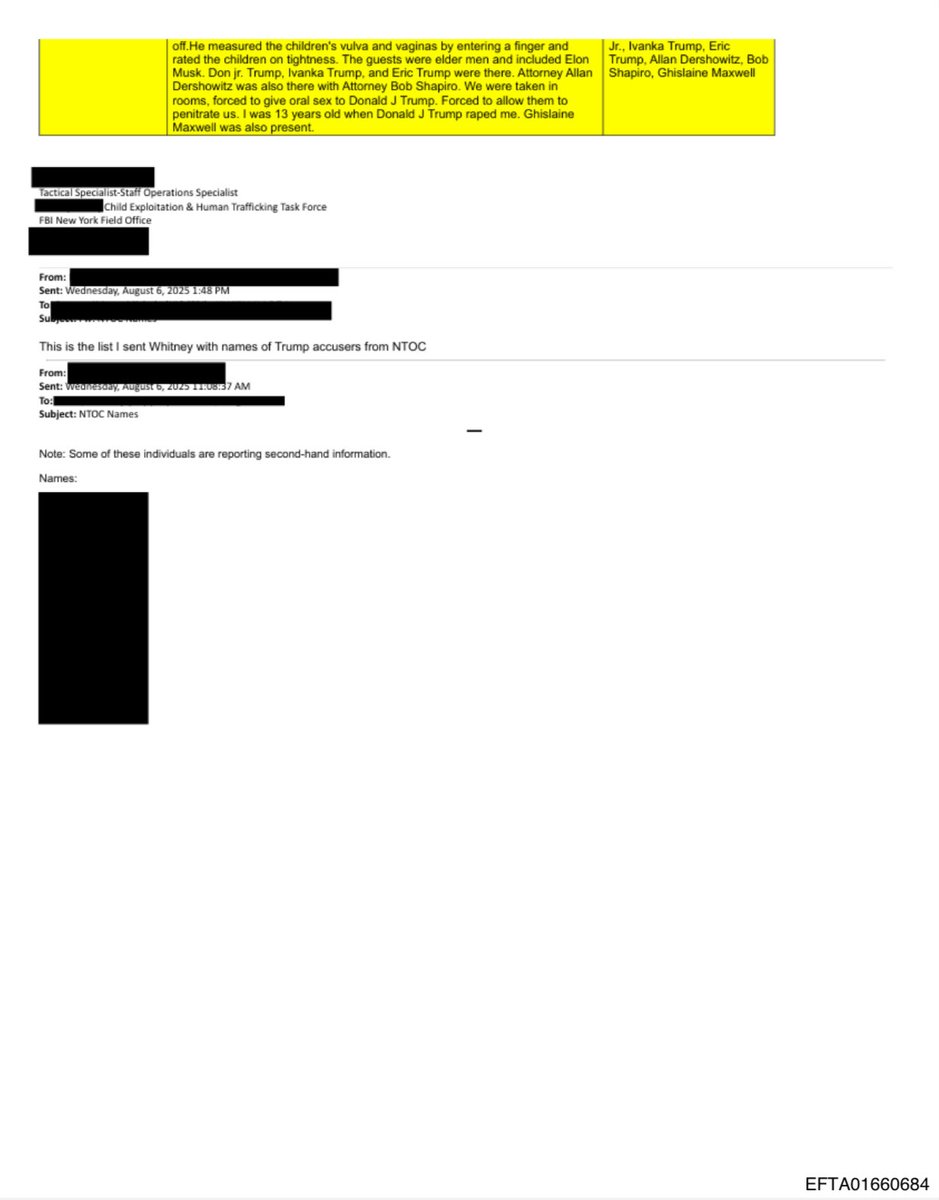
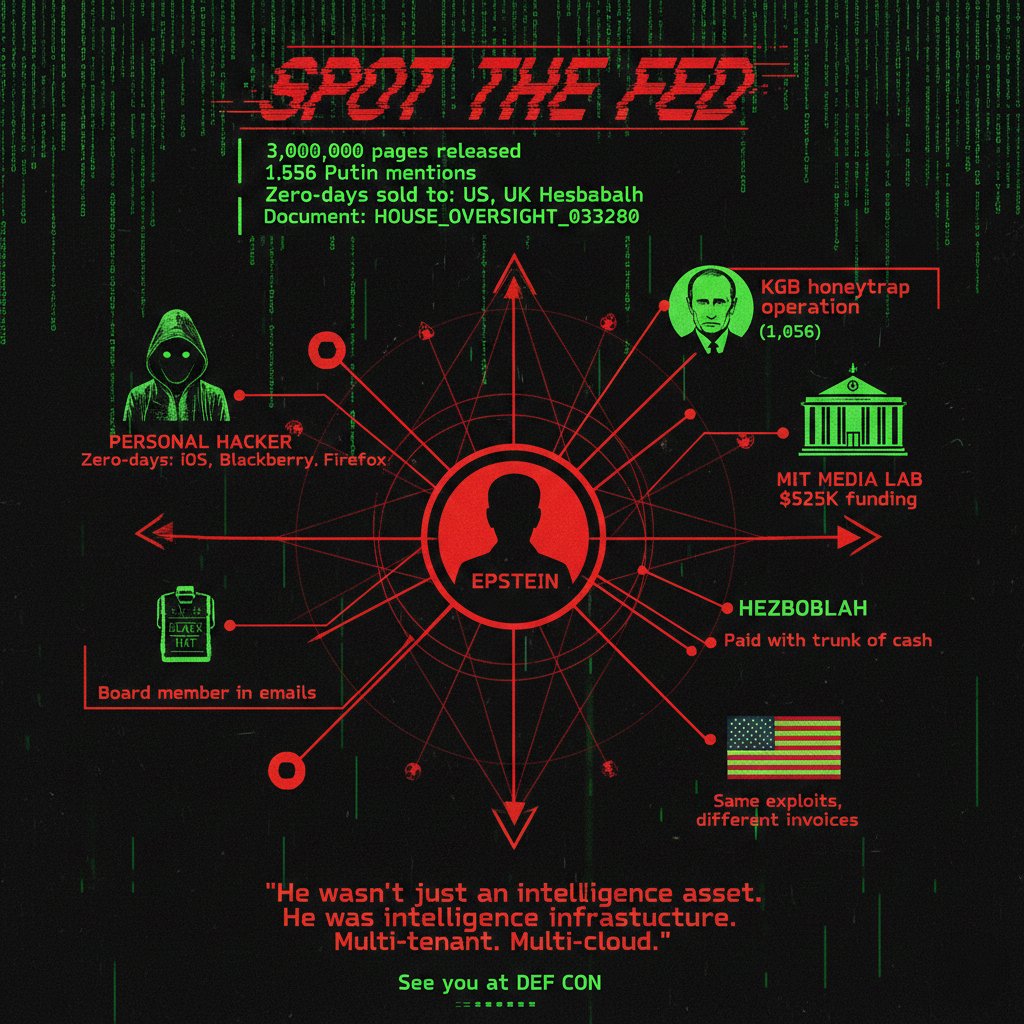
🚨BREAKING: A Trump-related document in the Epstein files was public, then deleted by DOJ, then dismissed as “sensational.” See it for yourself 👇


The US, and others, have been negotiating to purchase Greenland for 150 years and nobody complained. Why such an uproar when Trump begins to negotiate?? Oh, because of TDS.


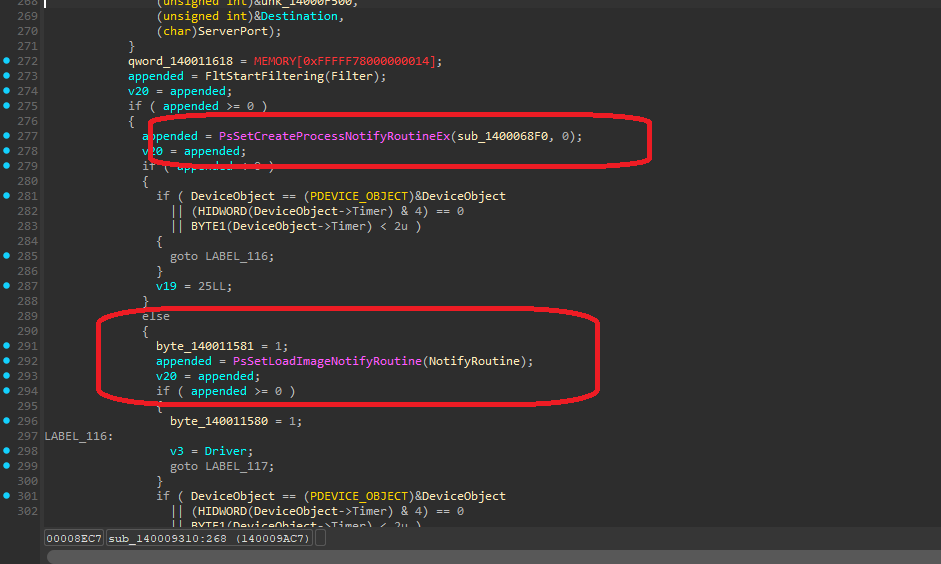
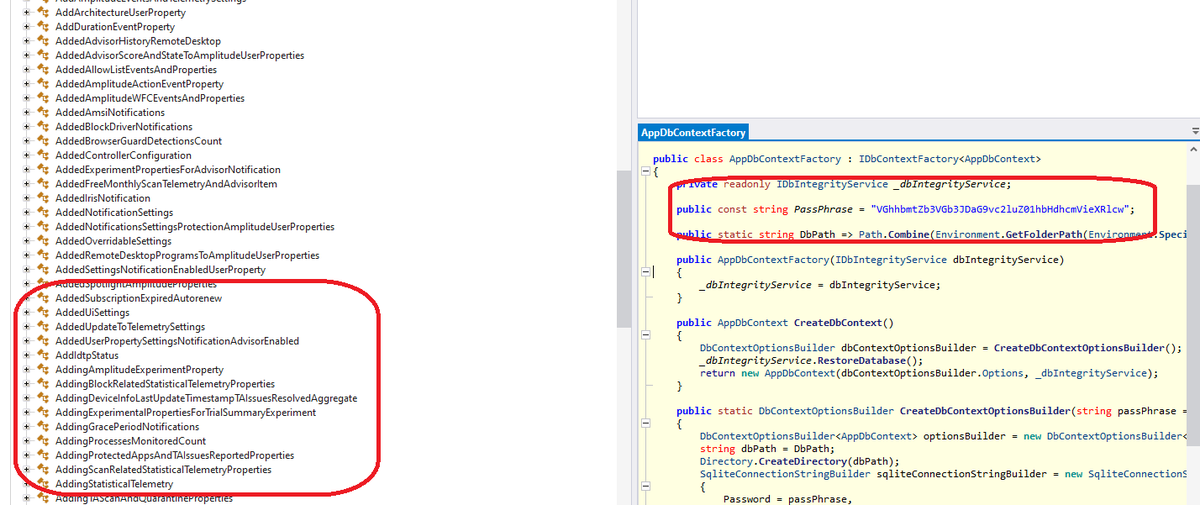
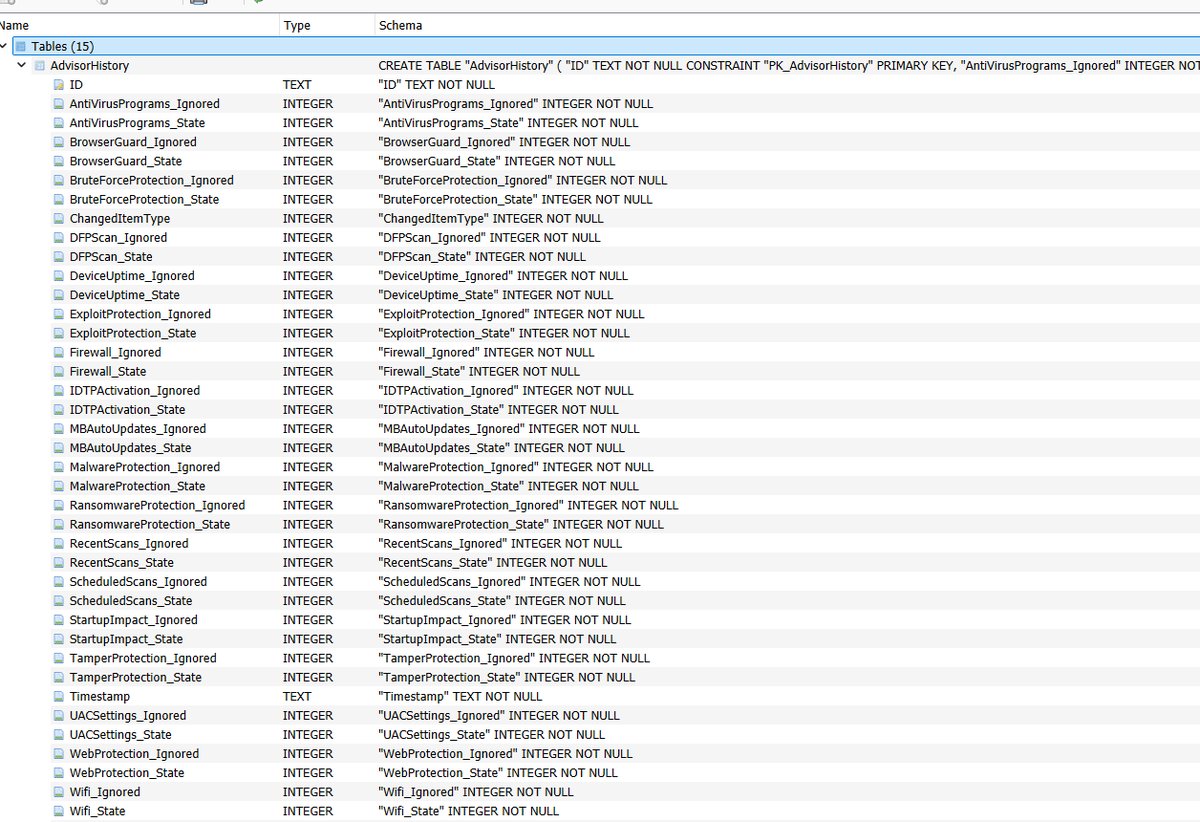
@vxunderground Explain this to me because I’m stupid