Grégory Parrot 🛡️🐧
2.7K posts


Grégory Parrot 🛡️🐧
@MrSlayers
Responsable Vulnérabilités Management & Micro-entrepreneur en secondaire (@XternalSoft) & Président de l'association https://t.co/0t3Maf3QEZ





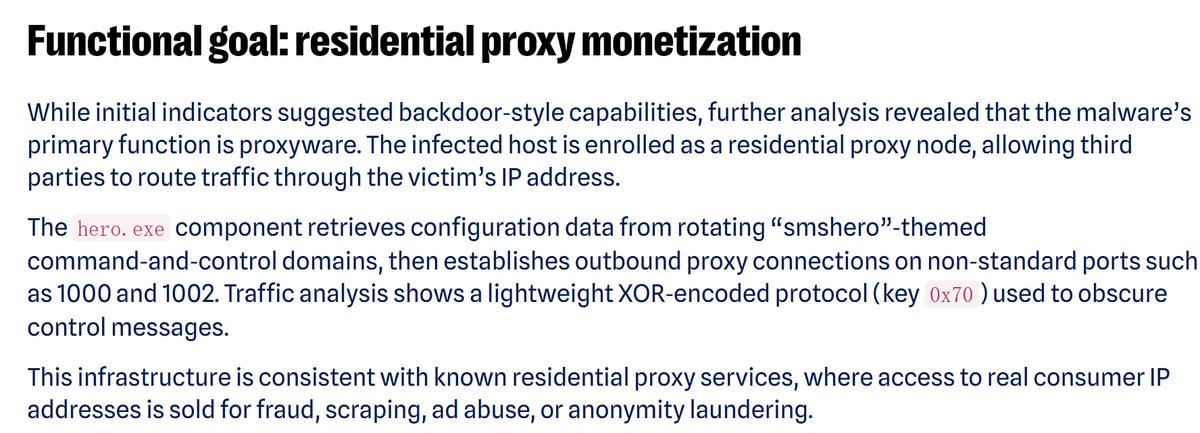






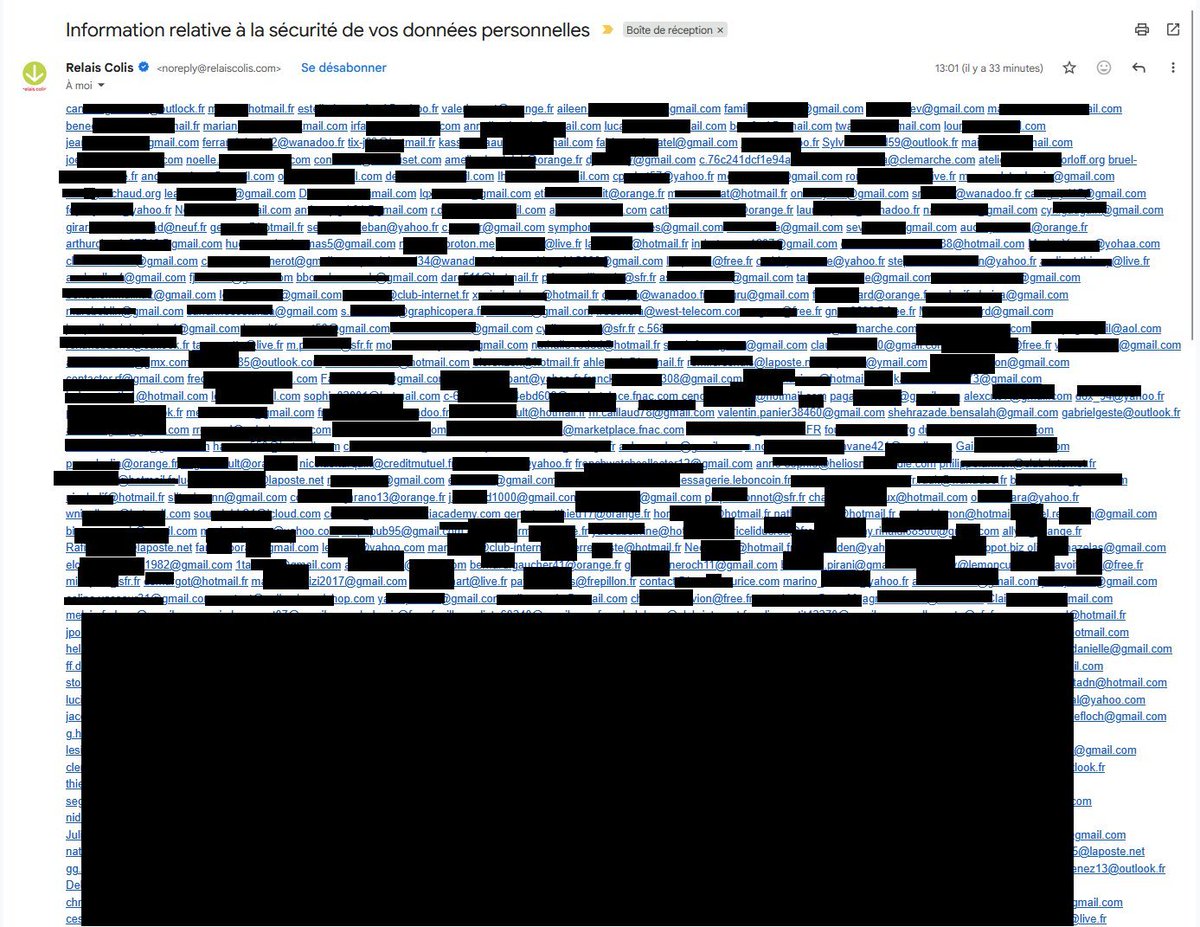
🚨🔴 ALERTE 🇫🇷 | Fuite Relais Colis : près de 10 millions de lignes exposés, noms, adresses, téléphones et emails… ⤵️ Après Chronopost, Mondial Relay et Colis Privé, c’est au tour de Relais Colis d’être victime d’une fuite de données comprenant près de 10 millions de lignes contenant nom, adresse complète, code postal, ville, téléphone et email.. le leak est pour l'instant mis en vente par le hacker. 📊 Volume : • 9 526 266 enregistrements • Base clients et données logistiques ⚠️ Types de données exposées : • Nom et prénom • Entreprise / enseigne • Adresse postale complète • Code postal et commune • Numéros de téléphone • Adresse email • Identifiant interne 🚨 Risques : • Faux SMS et emails de livraison • Faux livreurs • Vols ciblés • Usurpation d’identité • Phishing • Revente de bases clients • Risque physique direct