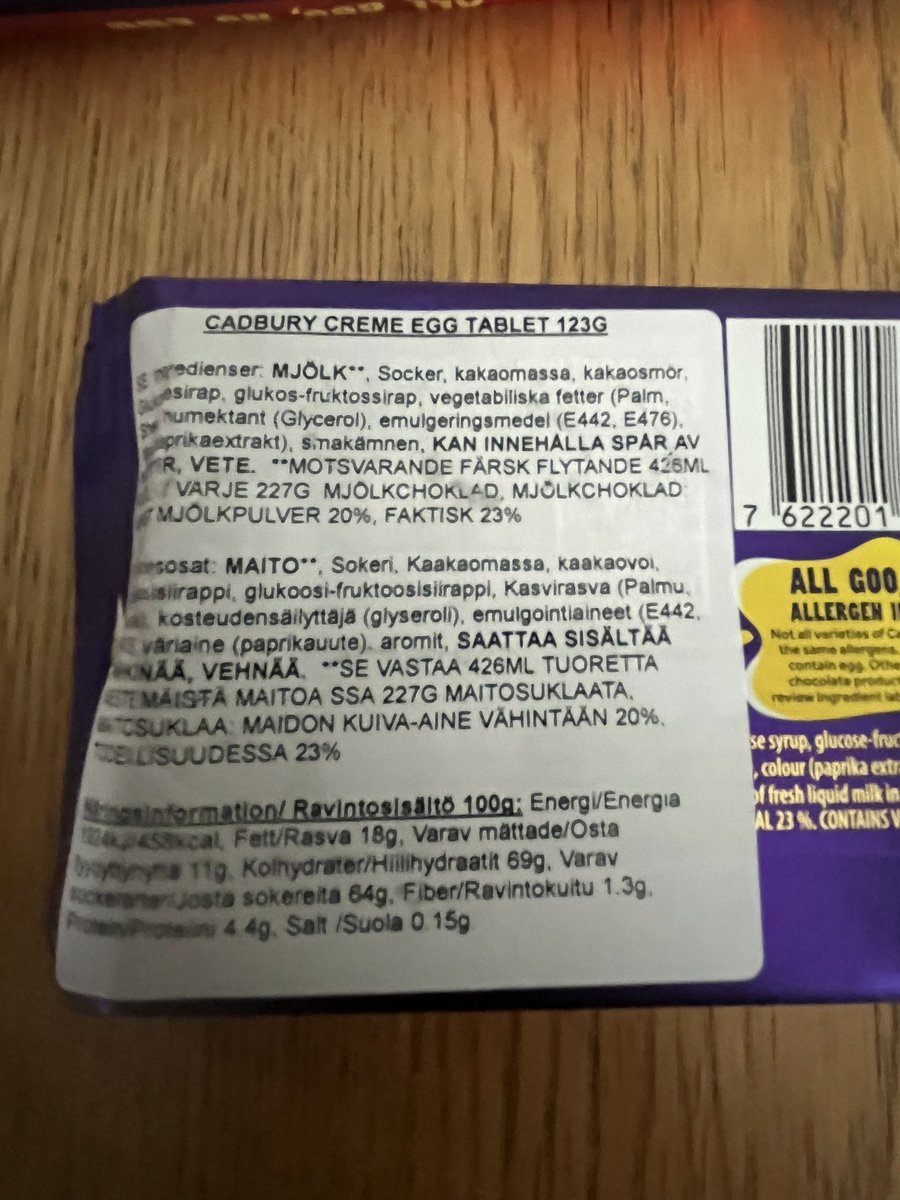
@elormkdaniel Straight in the bin.
I just want to know what's relevant
English
P.T.D
662 posts

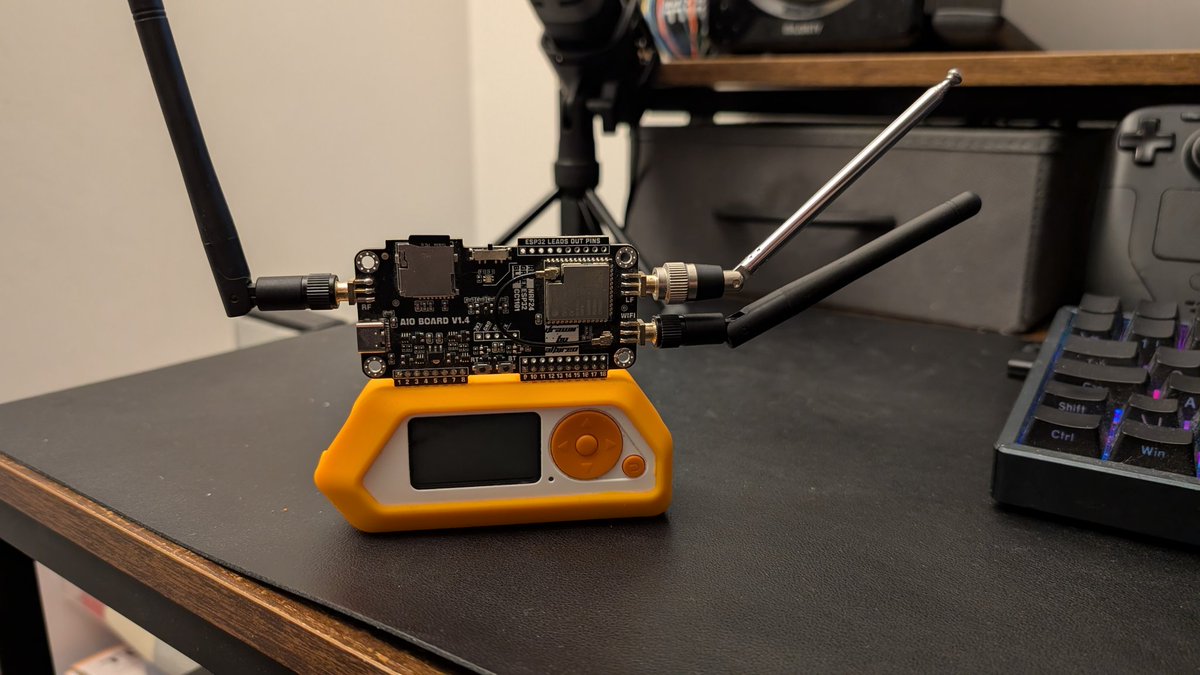
@Scada_Hacker
Critical Infrastructure Security / Presumed Hacker https://t.co/B8EBfMrk95










Developers be honest. Have you ever used Kali Linux?

Cybertruck replacing Raptor + Porsche