Rockwell
314 posts


Rockwell
@hanysfa
Pentester @SeclabId | OSCP | OSEP | OSWE | Into Telecom and RE | tweet in EN/INA | opinion = mine


















How to be a Principal Engineer/Senior Principal Engineer/Senior Architect/fancy-sounding-title Engineer, a thread: 1. You're evaluated on how much more the company succeeds because you're there, not the lines of code you wrote. If you can unblock someone, do that. If you need to kill a two year project that's not going anywhere, do that. Do what is right, not what makes you look good.

Masih ingat tweet ini? Bbrp minggu yang lalu gw ngulik apa isi code yang mentrigger Microsoft Defender di VMnya @hynzoime_ dan ini yang dibilang oleh media infosec sebagai InfoStealer. Gw bahas detil teknis apa yang ada di dalam code ini. Gak pake iklan tentunya 🧵

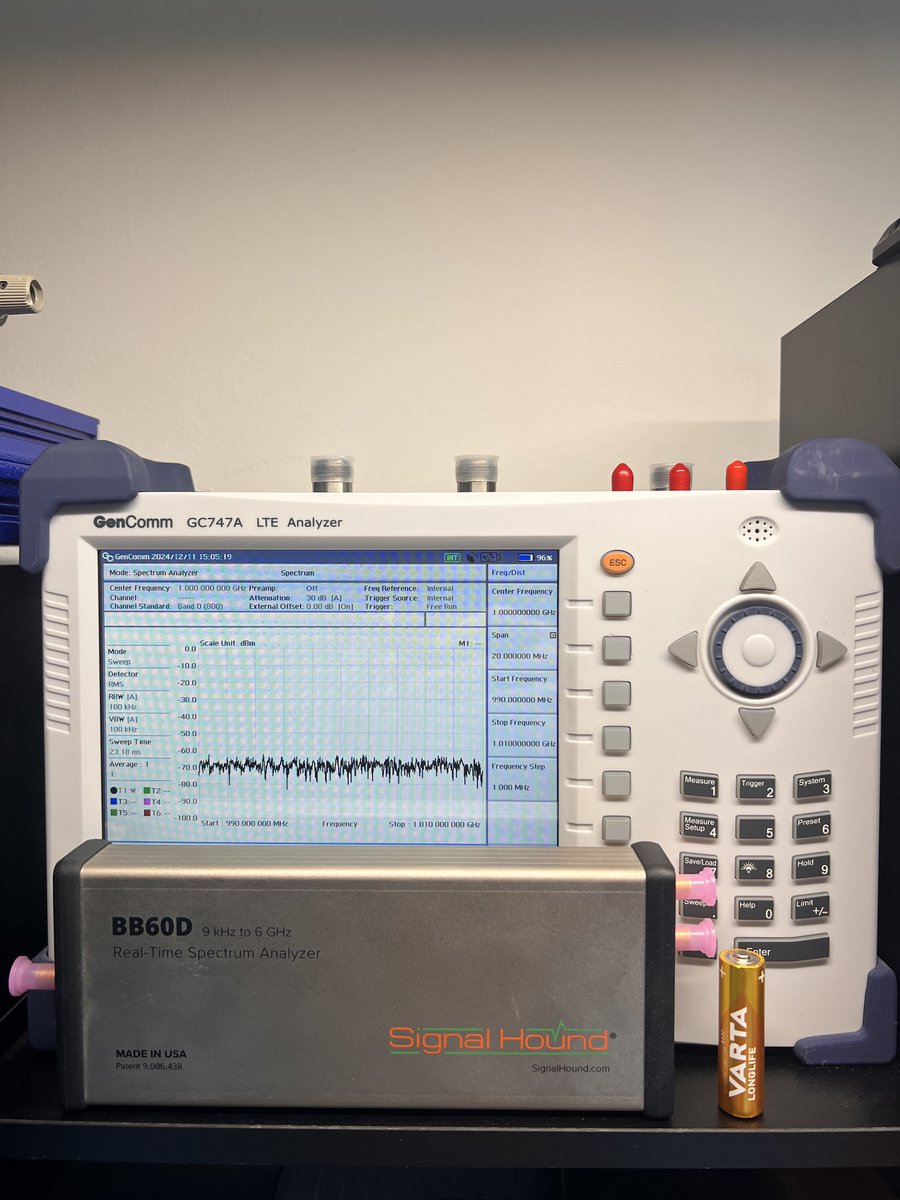

🧵 How to build an RF lab on a budget? A hacker's guide to the most important tools for signal hacking/analysis. Let's first introduce a few concepts and tools before actually jumping into the specific brands and models. Depending on what you want to do, there are a few tools you need in your lab for frequency analysis, antenna testing, and RF measurements: 1. spectrum analyzer: one of the most important tools in an RF lab. A device that lets you "see" signals. Mostly come in 2 shapes: either standalone (benchtop or portable, but with its display, and works independent of a computer), or USB-based that needs a computer. It's like a receiver, receiving signals from its input port (e.g. from an antenna) and showing them to you. 2. signal generator: as the name says, a device to generate signals. Like a transmitter. Important for many use cases (testing antennas, receivers, and many other RF accessories) 1/7