Calle Svensson
7.6K posts


Calle Svensson
@ZetaTwo
Security Engineer @ XTX. MSc in eng. physics & CompSci, dev & gamer. ❤️ music & long distance running. Wanna do a PhD sometime. Same U/N on all other sites














Here it is, our biggest issue to date, Issue #8! Read, share, enjoy! pagedout.institute/?page=issues.p… Get prints here - lulu.com/search?page=1&… And with that CFP for #9 is open - deadline 30 April 2026



I have so many thoughts on that Trackmania at EWC announcement. A lot of implications in this one, too. But there is something very beautiful about the fact that THE ESWC game from 15 years ago, is returning to the E(S)WC. Now we know all games for 2026 and yes, no AoE II 🤣

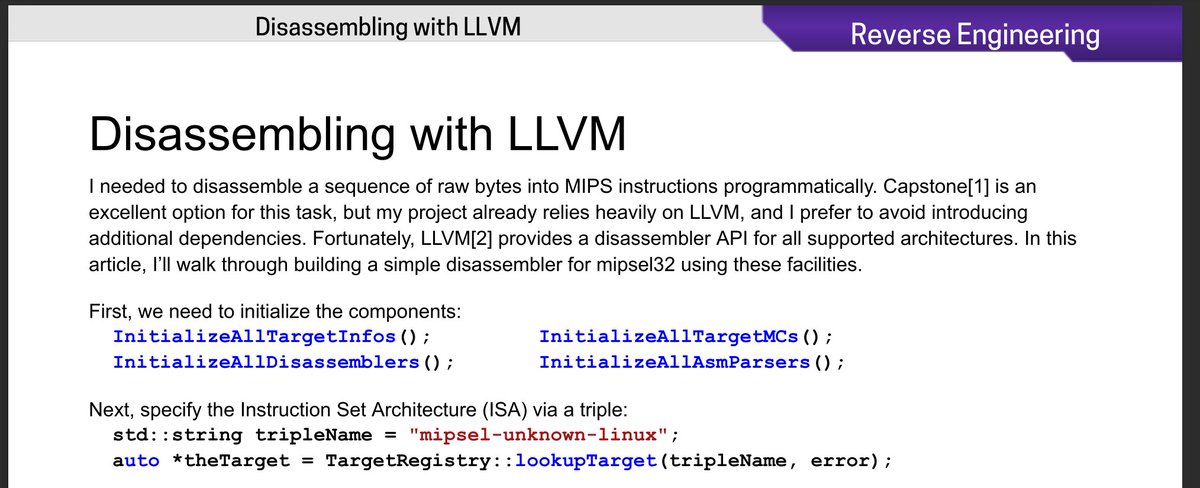
Carl Svensson (@zetatwo) is bringing Age of Empires II Definitive Edition to RE//verse 2026 as a playground for tooling. This talk walks through Binary Ninja automation to decrypt and deobfuscate game code and a BNIL query system for matching obfuscated instruction patterns. If you like game reversing you will want to see this talk: shop.binary.ninja/collections/re…








Games made in Sweden stood for 20% of the revenue on Steam in 2025. Pretty impressive considering Sweden’s size of 10 million inhabitants. Source: @alineaanalytics









