MalwareHunterTeam
71K posts


MalwareHunterTeam
@malwrhunterteam
Official MHT Twitter account. Check out ID Ransomware (created by @demonslay335). More photos & gifs, less malware.

🤯You can't make this up: amid Kremlin meddling in Hungary's election, OSCE PA sends Vladimir Putin's former interpreter Daria Boyarskaya – sanctioned by Poland, detained by Lithuania – on an election observation mission to Budapest. More in my newsletter: vsquare.org/goulash-putins…

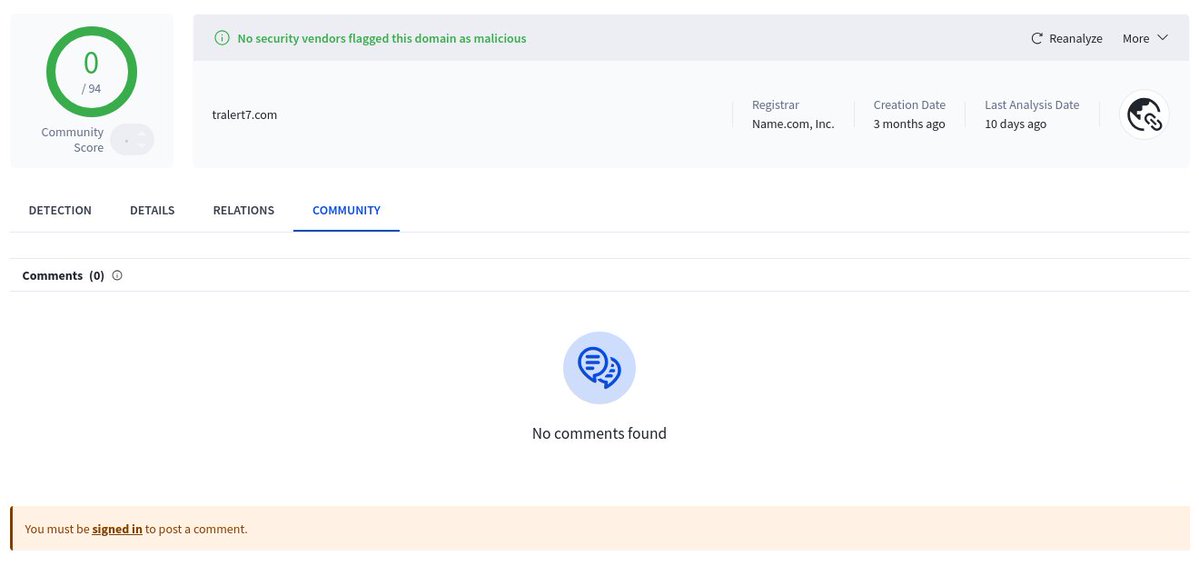
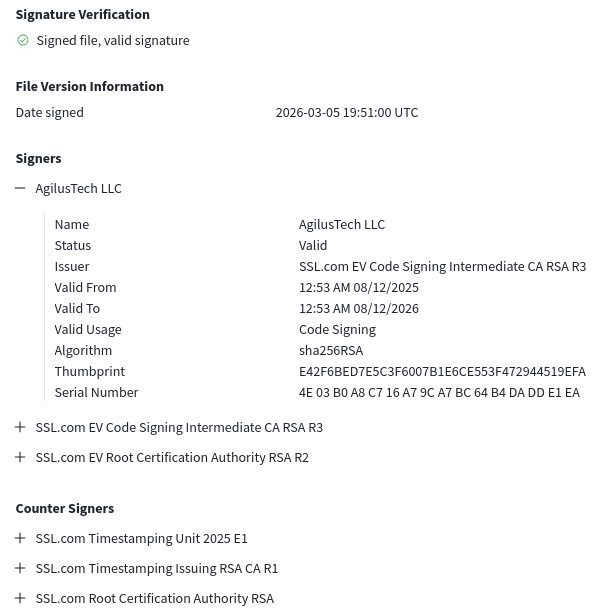
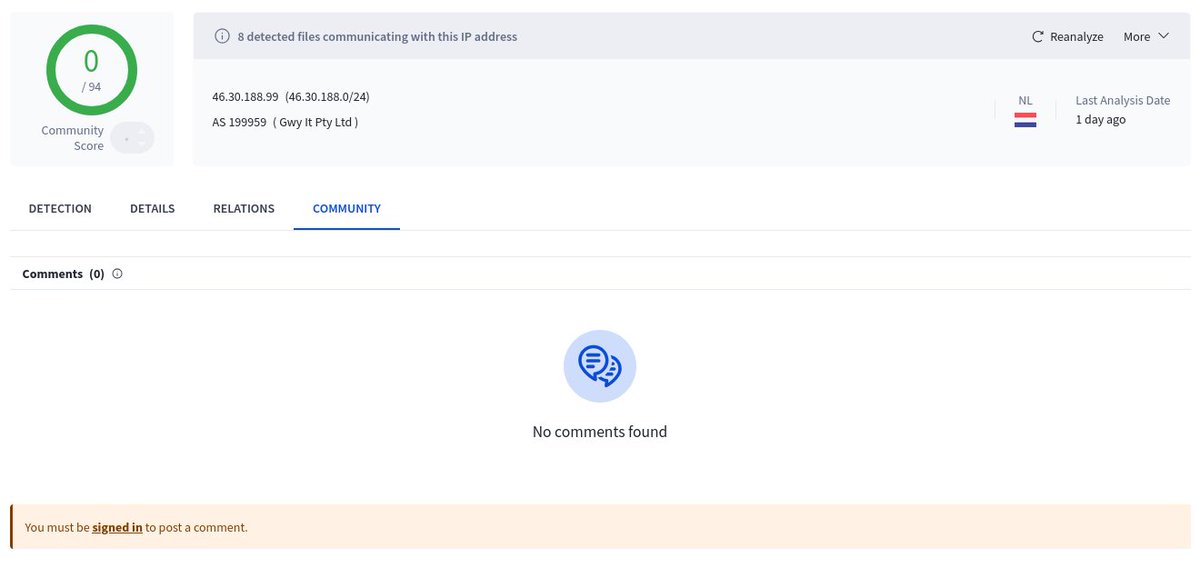
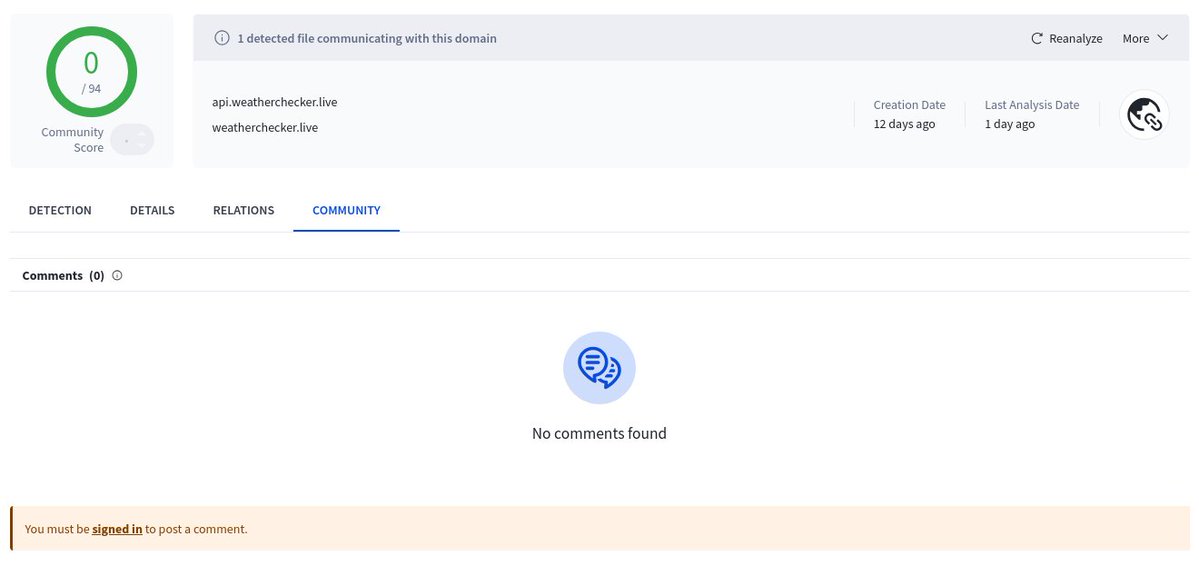
1/ New #macOS samples, 0 detections on VT as of writing, but multiple artifacts suggest Sliver-like HTTP(S) C2. Shared by @malwrhunterteam. What stood out: procedural URL patterns, PNG-wrapped network payloads, no plaintext IOCs, and wazero/WASM-related execution. More below👇





Another double extension compiled AppleScript file shared by @malwrhunterteam: Digital Currency Group (DCG) - Audit Confirmation Request.docx.scpt - 61b56c8c2df374861c8b23e6c555456f34e17e5638ea9965f721c3ffe77f57ca. If you go to line #1649, you can see the actual commands. 🧵

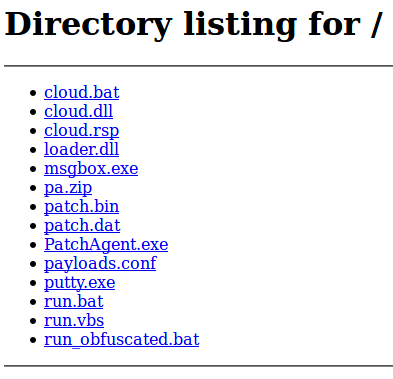
Two related samples are uploaded @abuse_ch bazaar.abuse.ch/browse/tag/46-…

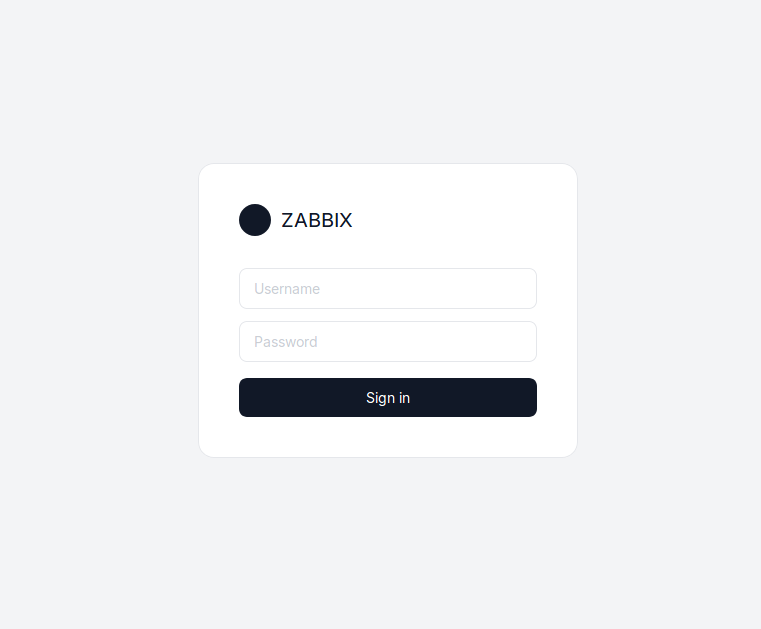
Some panel with "ZABBIX" as "login-brand": http://41.216.188[.]46:8443/login 🤷♂️



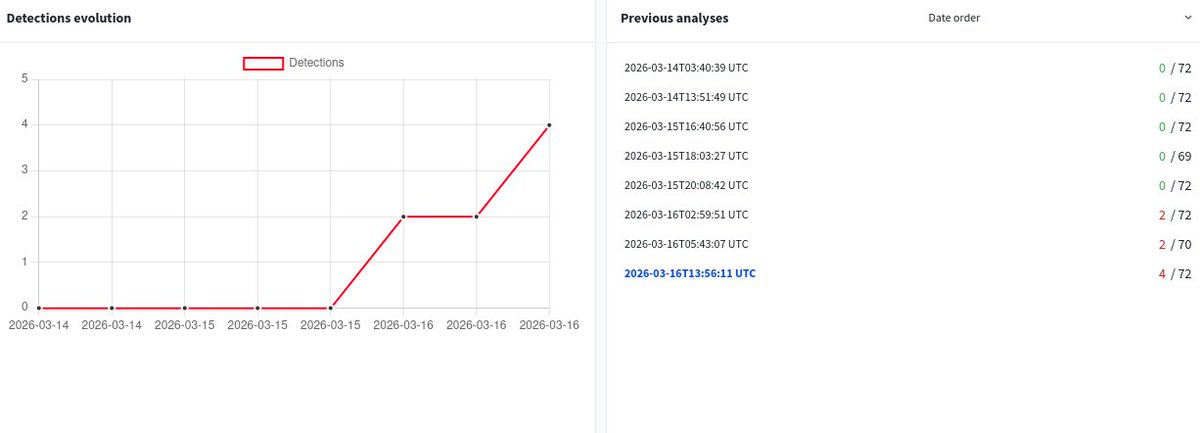
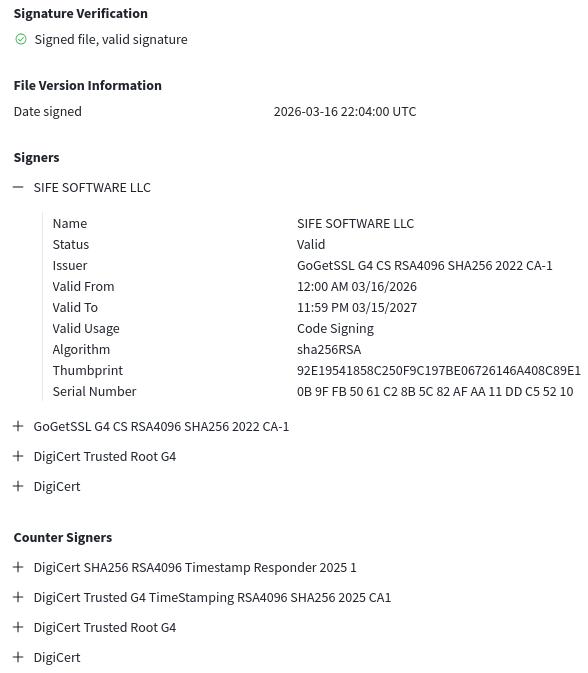
@malwrhunterteam Certificate reported. Uploaded to Triage for analysis and available for others to download: tria.ge/260316-qyhvbsg… Also made available on Mega NZ: #Id-ichinwCbfOOCJHT-USys2xO4hnxf32XXCxtWLagM" target="_blank" rel="nofollow noopener">mega.nz/file/tntjDKpY#…