固定されたツイート
0xSimon
2.9K posts


0xSimon
@0xSimon
programmable money , technical lead @ObexIncubator , stealth
Miami, FL 参加日 Nisan 2022
1.6K フォロー中4K フォロワー

It's obvious why Quasar is beating Anchor, but a lot of people are also asking "why is Quasar beating Pinocchio on some CU benchmarks?" I personally really dislike the framing of the question, as it appears to draw an incorrect conclusion.
It is certainly not the case that @0x_febo neglected to optimize a bunch of things and we managed to beat him to it. Quite the opposite, in fact! Pinocchio, and now by extension, the newer versions of Solana SDK, are actually *so* optimal that the only way we have found to significantly reduce CUs any further is by introducing additional context in the form of a framework.
Comparing a library to a framework is not an apples-to-apples comparison. There are many program-specific optimizations that are trivial to implement when you have enough context, but extremely difficult to generalize into a program-agnostic library. Allow me to explain one such case:
In 2024, @cavemanloverboy introduced solana-nostd-entrypoint and solana-nostd-invoke. This was the first serious attempt to address some of the absolute worst Solana SDK code consumed by every single onchain program. Within this crate, Cavey introduced a technique called "nodup" entrypoint, where instead of burning CUs to manage duplicate accounts, you simply error out the moment you encounter one. This technique stacks well with some other optimizations that I'll get into later.
Unfortunately, due to the nature of how the Solana entrypoint was originally designed to be both global for all instructions in a program, and require full parsing of many variable length inputs to achieve any situational awareness, all it takes is for one instruction in your program to have a potential duplicate account for the entire program to be unable to take advantage of this technique.
Last year, I floated an idea to Febo, Cavey and @alessandrod: What if, in addition to register 1 pointing to the start of the serialized input region, we also instantiated the VM with a pointer to the first byte of our instruction data in register 2? This would enable us to create per-instruction entrypoints, allowing us to safely and performantly take advantage of techniques like nodup.
@realbuffalojoe picked up the idea, wrote the SIMD and agave implementation, and pushed a whole bunch of insane PRs to our mainnet compatibility tooling to ensure this would be safe for all currently deployed programs and clusters. The feature is now active on testnet and devnet, and is due to be activated on mainnet within the next week or so. That's when Quasar officially achieves mainnet compatibility.
As a result of all of us working together, a new optimization emerged: When operating under the assumption that you have immediate access to the instruction discriminator via r2, it is now possible to know:
- exactly how many accounts your instruction expects, and
- whether they will be a signer, mutable, executable or duplicate
Due to how the account flags are encoded in a contiguous 4 byte sequence, rather than having to perform four individual checks (is_duplicate(), is_signer(), is_mutable(), is_executable()), we can actually stack these into a single u16 or u32 comparison. This means that not only is the r2 entrypoint able to safely and optimally utilize nodup; it also typically gives us our signer/mutable/executable checks for free!
We're still on our day zero "unrelease", grinding away trying to stabilize the API and put out our first official version, but we'll be sure to put out some proper research detailing some of the techniques we've discovered along the way once we're done. One thing is for sure: Enabling an efficient Solana program framework was not just a @blueshift effort. We stand on the shoulders of giants. 🙏
English

@TheDefiSphere Defi need better risk metrics , huge props to the @BlockAnalitica team for this build
English
0xSimon がリツイート

Today we're launching the new Sphere Dashboard.
Real-time DeFi stablecoin lending analytics: rates, risk scores, liquidation data, and simulation tools across 270+ markets on Ethereum, Arbitrum, Base, Avalanche, and Plasma.
defi-sphere.com
English

The graded Pokémon card market is still really fragmented, especially with more TCG RWA platforms popping up.
That’s why I built @OnlySlabs_
Search Pokémon slabs across marketplaces in one place and spend less time digging for the slab you actually want.
We’re opening up a closed beta now.
If you want early access, reply below.
onlyslabs.io

English

@grovedotfinance @kevinlichan great explanation , love to see grove pushing RWAs
forward
English

T-Bills were the entry point. AAA CLOs were the natural next step.
@kevinlichan on why Grove allocated into this asset class to scale onchain credit.
English

For ERC-8109 Diamonds, Simplified, should the events that track functions added to, replaced in, and removed from diamond contracts be three events like this:
DiamondFunctionAdded(selector, facet)
DiamondFunctionReplaced(selector, oldFacet, newFacet)
DiamondFunctionRemoved(selector, oldFacet)
Or one event like this:
SetDiamondFacet(selector, facet)
Or one event like this:
DiamondFunctionSet(selector, oldFacet, newFacet)
(When oldFacet is address(0) then it means adding a new function)
(When newFacet is address(0) then it means removing a function)
I am interested in feedback about this from developers, and people that work on indexers, block explorers and other tools that use events.
The full draft ERC-8109 standard is here: eips.ethereum.org/EIPS/eip-8109
Discussion about this is here: ethereum-magicians.org/t/erc-8109-dia…
English

@muellerberndt @sherlockdefi Amazing! Thanks for sharing im trying it out now
English

@0xSimon @sherlockdefi This is proprietary. But you can check out my open source tool here if you haven't already github.com/scabench-org/h…
English

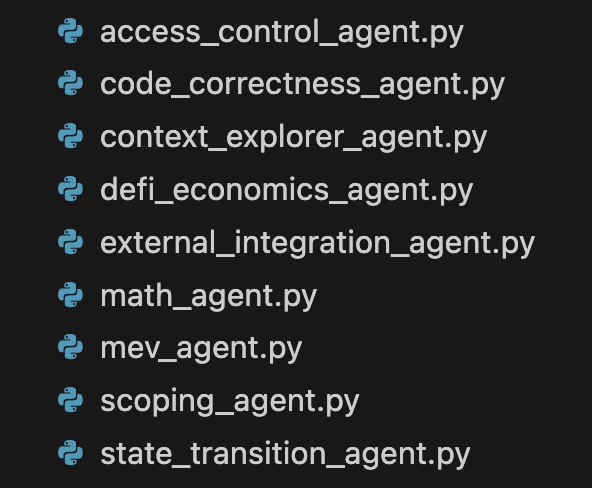
Running @sherlockdefi AI is like hiring an army of top-tier web3 auditors, each of which uses custom methodologies and tools derived from real contest-winning workflows. It’s only getting better from here.
English

@mjovanovictech You can set a deterministic unique key constraint on a column and it will be ACID compliant. If the tx key is deterministic you don’t need to deal with locks at all
English

Imagine you just sold the very last ticket to a concert.
But two users clicked "Buy" at the exact same millisecond.
Both requests hit your server. Both check the database. Both see Tickets = 1. Both process the payment.
Congratulations, you just sold one seat to two people. You have a Race Condition, data corruption, and angry customers.
This is why we need Distributed Locking.
It acts like a physical token. Before any server can touch that ticket record, it must acquire the lock.
• User A's request grabs the lock.
• User B's request tries to grab it, sees it's taken, and waits (or fails).
• User A buys the ticket.
• User B finally gets in, sees Tickets = 0, and is politely turned away.
"But what if the server crashes while holding the lock?"
That is the most common fear. If the server dies, does the lock stay forever?
No. This is why we use Lease Times (TTLs). The lock automatically expires after a set time (e.g., 10 seconds) if it isn't renewed. It’s a dead man’s switch for your data integrity.
Pro Tip: You might not need Redis for this.
If you are using PostgreSQL, you can use Advisory Locks. These are application-level locks that allow you to lock abstract concepts (like "Ticket_ID_123") rather than just database rows.
I wrote a full breakdown on how to implement this pattern here: milanjovanovic.tech/blog/distribut…
Note: this isn't the only way to solve this problem. We could also use optimistic locking, with versioning of the ticket quantity. If we get a version conflict on save, the transaction is rolled back. Another interesting solution is the business one: it's ok to oversell some tickets. We can expect some people not to show up to the concert, so we won't run into seating issues (but it's a risk).
---
Sign up for the .NET Weekly with 75K+ other engineers, and get a free Clean Architecture template: milanjovanovic.tech/templates/clea…

English


Many people have asked me where my formatting style is from. It all started before I've ever written a single line of Solidity code.
I was a Machine Learning Engineer before and I did most things in numpy, pytorch and tensorflow. Don't use tensorflow, but that's for a different time.
Most of that code are chains of mathematical operations. This is where I picked up the symmetry thing.
Lining up equations just makes it so much easier to read. The symmetry is also just beautiful.
@jeremyphoward blog post was also very influential. READ IT! docs.fast.ai/dev/style.html
Most of my work was in Jupyter Notebooks. I love JNs. Having illustrations and explanations live directly where my code lives totally makes sense to me. We probably should write Smart Contracts like that.
Imagine the Uniswap contract with all its visualizations just on top of the code. Great for people reading it and amazing for auditors.
Formatting by hand is also just a great way to re-read code. You can not automate that! Although maybe you could train an LLM on all my contracts and see what happens!
If you want to build a shafu formatter lmk! I would fund it.
forge fmt --shafu

English

incredible knowledge from one of the best auditors in the space
Optimum@0xOptimum
Hey frens 👋 My smart contract security guide just got a glow-up — it’s now a GitBook 😎 docs.optimumsec.xyz
English

Hey frens 👋 My smart contract security guide just got a glow-up — it’s now a GitBook 😎
docs.optimumsec.xyz
Optimum@0xOptimum
Security is a top priority for every #web3 project. While much is written about vulnerabilities, less focus is on practical steps for a secure lifecycle. Check out my guide, "The Complete Guide to Securing Smart Contracts," from design to deployment. github.com/optimumsec/com…
English