John Connor
384 posts





Everyone wants the gist. But the gist is what's left after someone else decided what mattered. Their priorities aren't yours. Their filters aren't yours. When you operate on summaries, you're thinking with someone else's brain.

pwno.io exploiting a v8 engine pwn challenge

.@Volexity #threatintel: Multiple Russian threat actors are using Signal, WhatsApp & a compromised Ukrainian gov email address to impersonate EU officials. These phishing attacks abuse 1st-party Microsoft Entra apps + OAuth to compromise targets. volexity.com/blog/2025/04/2… #dfir

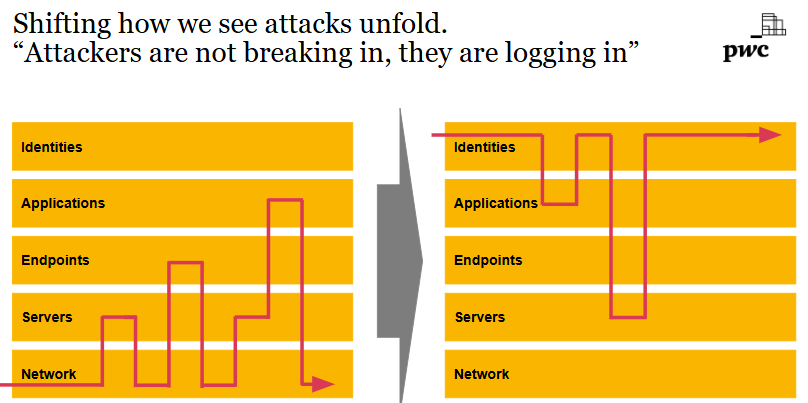
In the past, you had to: phish a user, drop malware, escalate privileges, pivot to servers, evade EDR, dump creds, move laterally, exfiltrate quietly, clean up, leave a backdoor. Today, you just: phish a user, steal an OAuth token, access everything from anywhere. Cloud breaches aren’t hacks. They’re logins.