Will Oram
402 posts

Will Oram
@willoram
Cyber Incident Response Director at @PwC_UK | Tweets about cyber security, ransomware, and identity-based attacks | Opinions my own

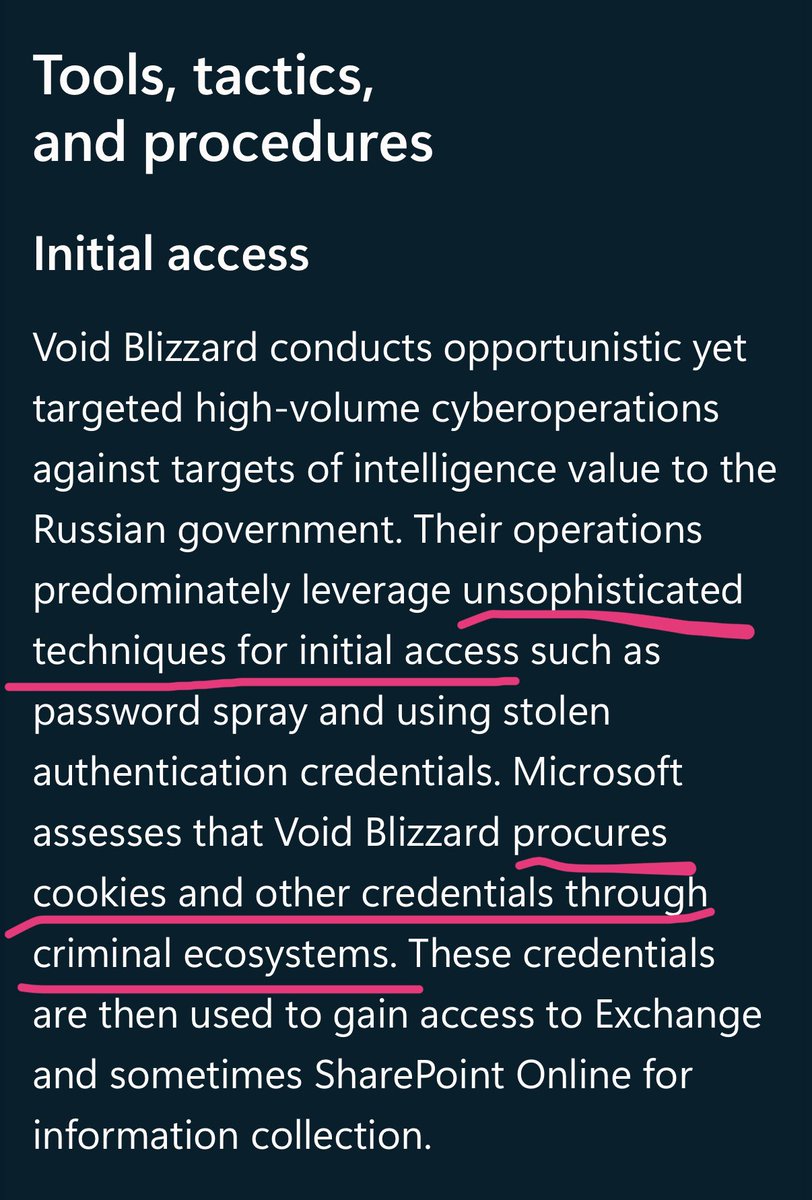

Microsoft has discovered worldwide cloud abuse activity by new Russia-affiliated threat actor Void Blizzard (LAUNDRY BEAR), whose cyberespionage activity targets gov't, defense, transportation, media, NGO, and healthcare in Europe and North America. msft.it/6011S9JpN

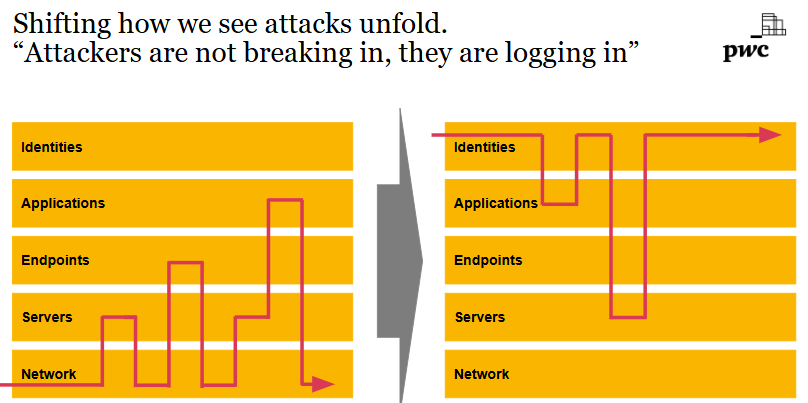
In the past, you had to: phish a user, drop malware, escalate privileges, pivot to servers, evade EDR, dump creds, move laterally, exfiltrate quietly, clean up, leave a backdoor. Today, you just: phish a user, steal an OAuth token, access everything from anywhere. Cloud breaches aren’t hacks. They’re logins.

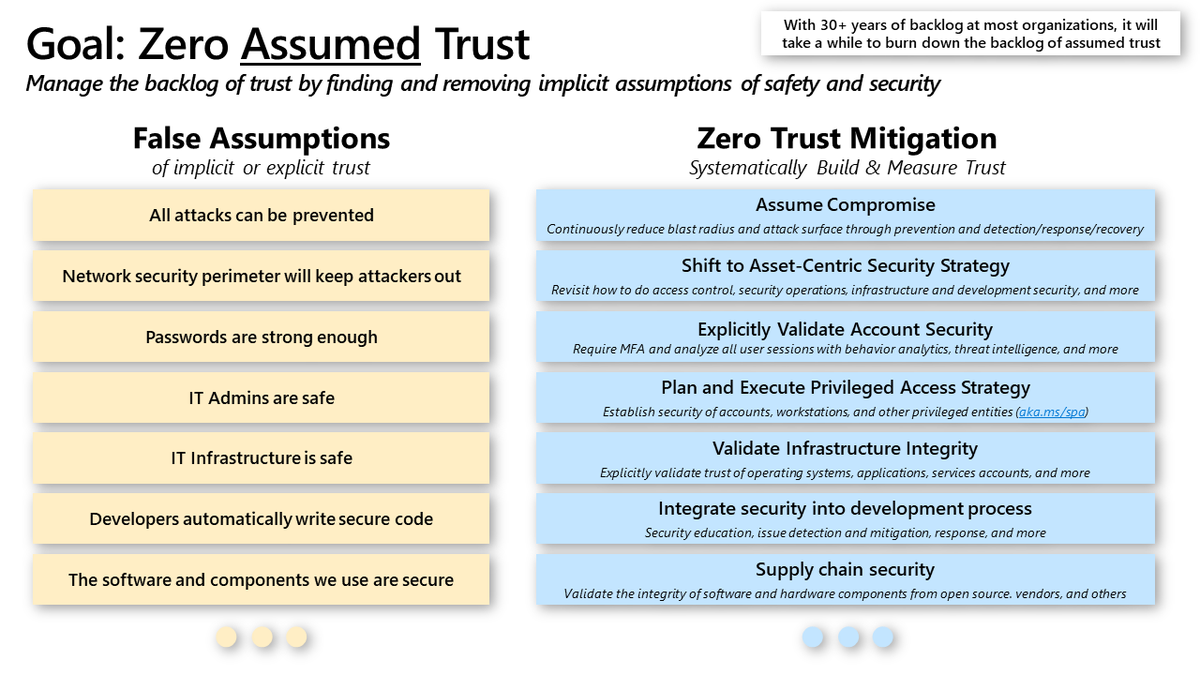
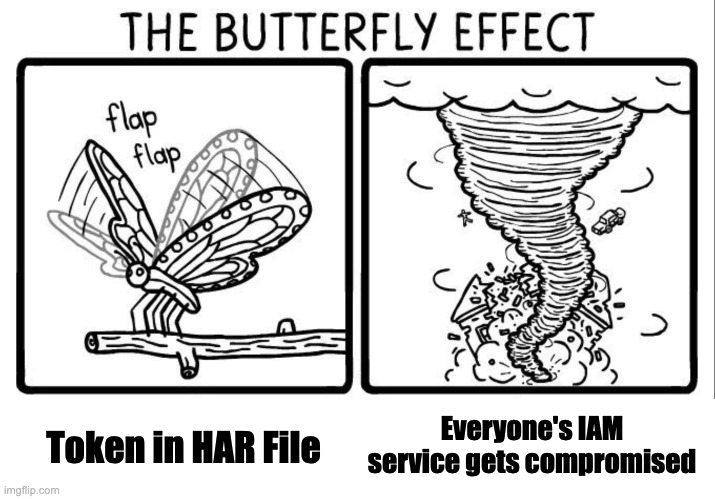
We’re seeing a clear trend: attackers are bypassing the endpoint entirely. Not just avoiding traditional EDR-monitored systems by pivoting to embedded and edge devices, but now also operating purely in the cloud. No shell, no malware, no persistence on the endpoint. Just an OAuth token and full access to whatever’s in the victim’s Microsoft 365, Google Workspace, or AWS console. It’s a complete inversion of how things used to be. The endpoint, once the weakest link, is now usually the most monitored, most policy-enforced part of the infrastructure. You’ve got EDRs, SIEM integration, automation, threat hunting - the full stack. But attackers don’t need to touch it anymore. Instead, they go after the new soft spots: - Cloud platforms, where logging is limited, expensive, or off by default - Network devices and appliances, which are practically blind spots - obscure OSes, no EDRs, hard to monitor, hard to forensicate. - Embedded systems and IoT junk that no one really knows how to secure, but that sit in critical network paths. Cloud especially is a mess: - Logging tiers cost extra and the good stuff is behind paywalls. - Detection content is lacking, both from vendors and the community. - You don’t get memory dumps or full control like you do on endpoints. - You’re at the mercy of the provider when it comes to visibility and response. And that’s the shift: attackers aren’t hacking computers anymore. They’re hacking trust relationships, identities, and APIs. The whole idea of detection and response needs to evolve with that. Otherwise, we’re securing the hell out of endpoints while attackers happily fish through mailboxes and cloud shares from halfway across the planet.




"Directory Synchronization Accounts" Entra role is very powerful (allowing privilege escalation to Global Admin role) while being hidden in Azure portal / Entra admin center (+ poorly documented) making it a stealthy backdoor for persistence in Entra ID 🙈 medium.com/tenable-techbl…








This table in the Microsoft Digital Defense Report is always fascinating, these stats are taken from DART engagements and other IR teams, it shows the common issues seen across our customers. Brilliance in the basics isn't easy, but worth it. Full report - aka.ms/mddr

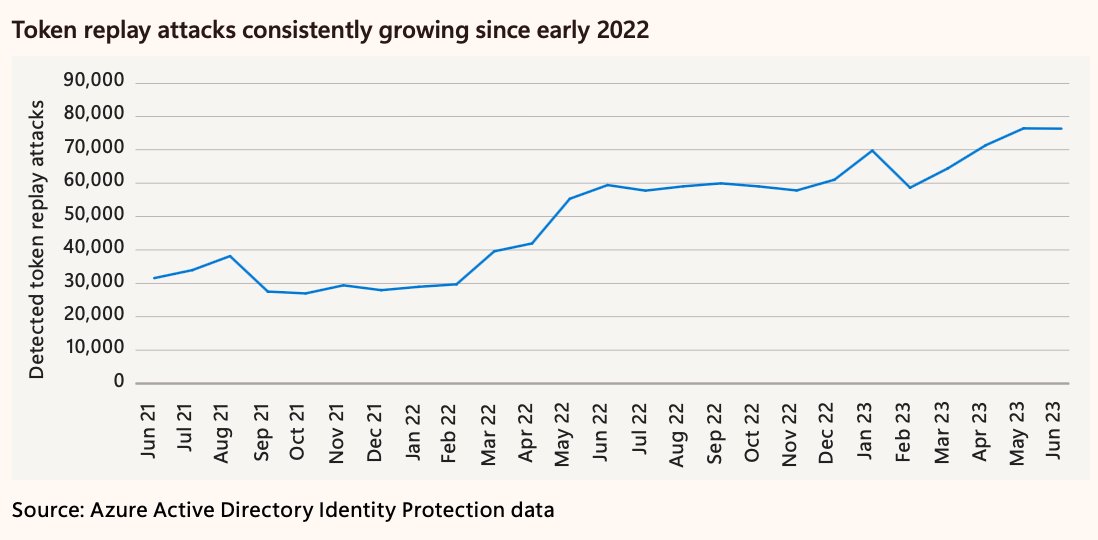
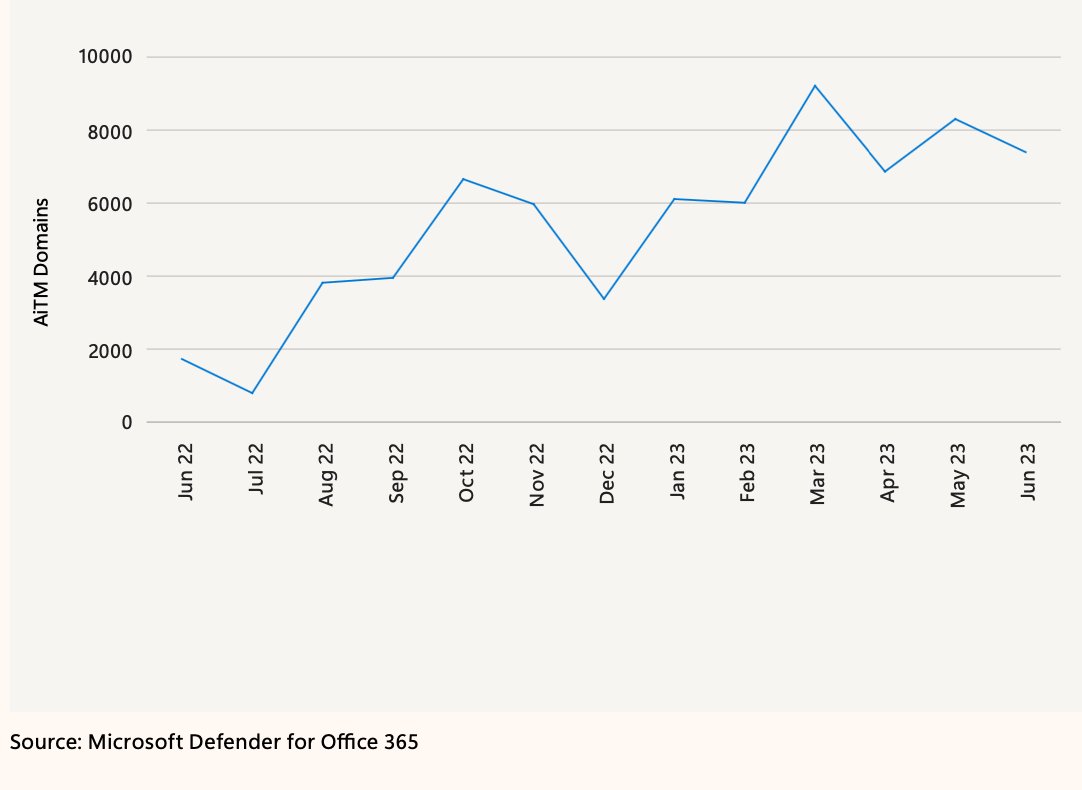
Great insights from Microsoft Digital Defense Report 2023. aka.ms/MDDR Major Increase in AITM domains, which also roughly translates to increase in token theft attacks 2022->2023 ~1500-2000 to~7000-9000