Sean Metcalf
22.7K posts


Sean Metcalf
@PyroTek3
Identity Security Architect @ TrustedSec. Microsoft Certified Master #ActiveDirectory & former Microsoft MVP. Co-Host @ Enterprise Security Weekly. He/Him. #BLM


🚨#BREAKING: According to Tech Sciencest they report that AI bot traffic is projected to surpass human internet traffic by 2027
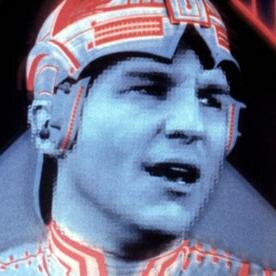
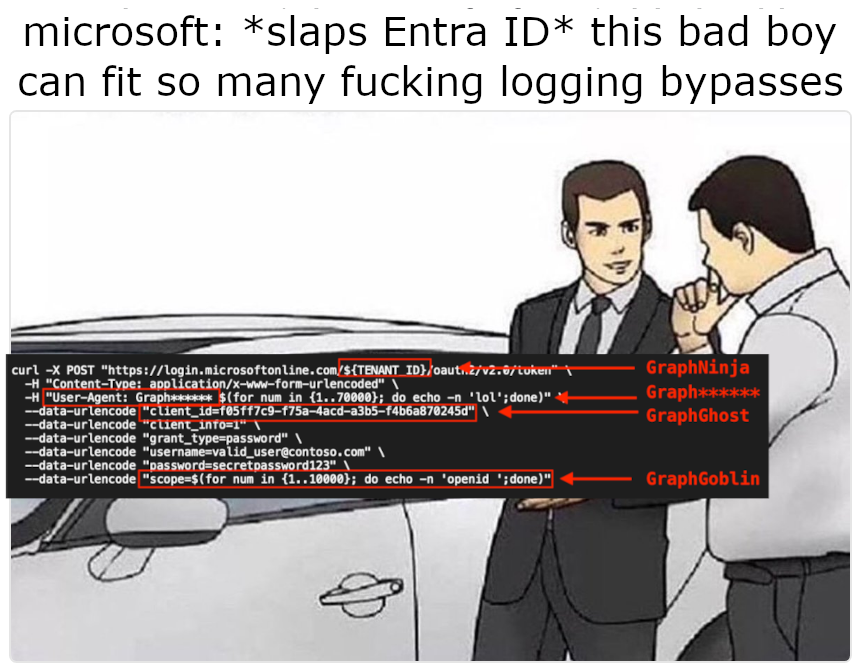
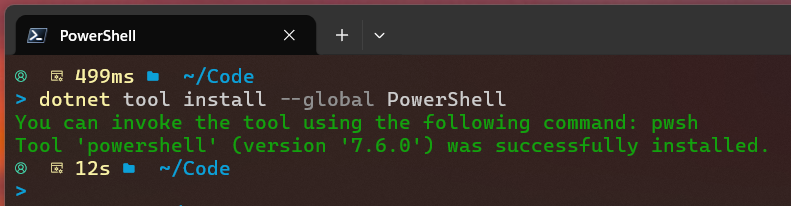
Who knew a really long string could make an Entra ID login disappear from the logs entirely? In our #blog, @nyxgeek breaks down how overflowing #Azure's sign-in logging mechanism allowed access tokens to be issued without a single log entry. Read it now! hubs.la/Q047xTVc0





Best practices for securing Microsoft Intune In view of the March 11, 2026 cyberattack against U.S.-based medical technology firm Stryker Corporation, which affected their Microsoft environment. Microsoft has newly released the following guidance: techcommunity.microsoft.com/blog/intunecus… #Cybersecurity #MicrosoftIntune #Hardening






🚨Well this is interesting... Aliens.Gov Name: aliens.gov Registry Domain ID: DF133F918-GOV Domain Status: serverTransferProhibited Nameservers:…cloudflare.comwally.ns.cloudflare.com Dates Registry Expiration: 2027-03-17 18:55:49 UTC Updated: 2026-03-17 18:56:12 UTC Created: 2026-03-17 18:55:49 UTC Check it out on Icann lookup.icann.org/en #ufotwitter #uapX #aliens Thanks to: reddit.com/user/thelazt1/