Sabitlenmiş Tweet

New logo. New website. Same DFIR Report team. 🔎
Check out the incredible analysts behind the research:
thedfirreport.com/company/analys…
English
The DFIR Report
1.7K posts


@TheDFIRReport
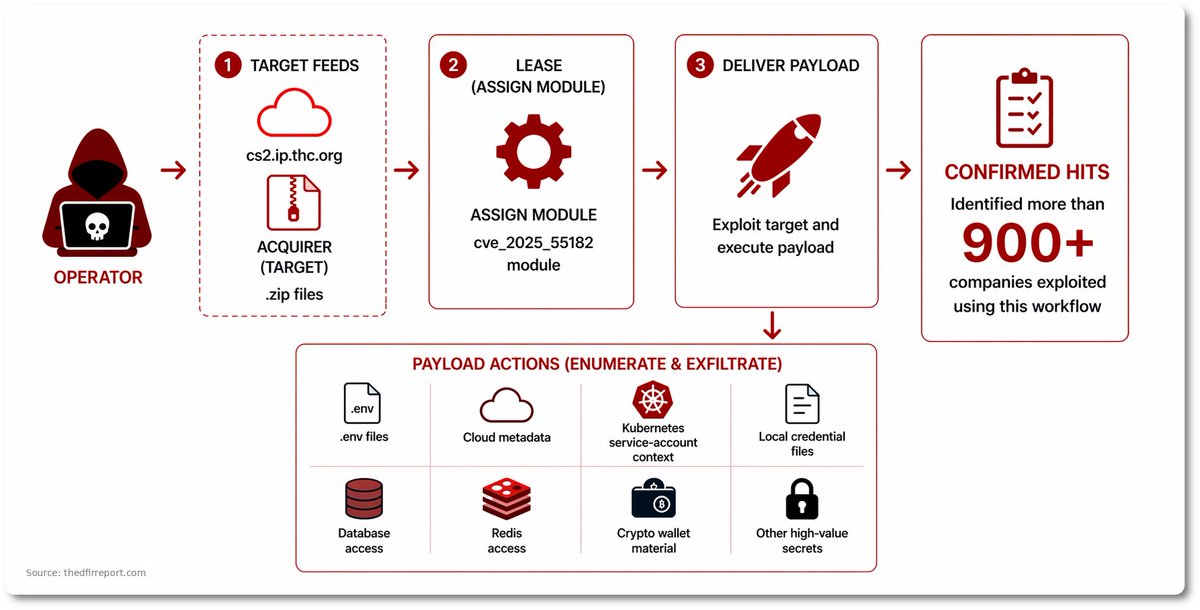
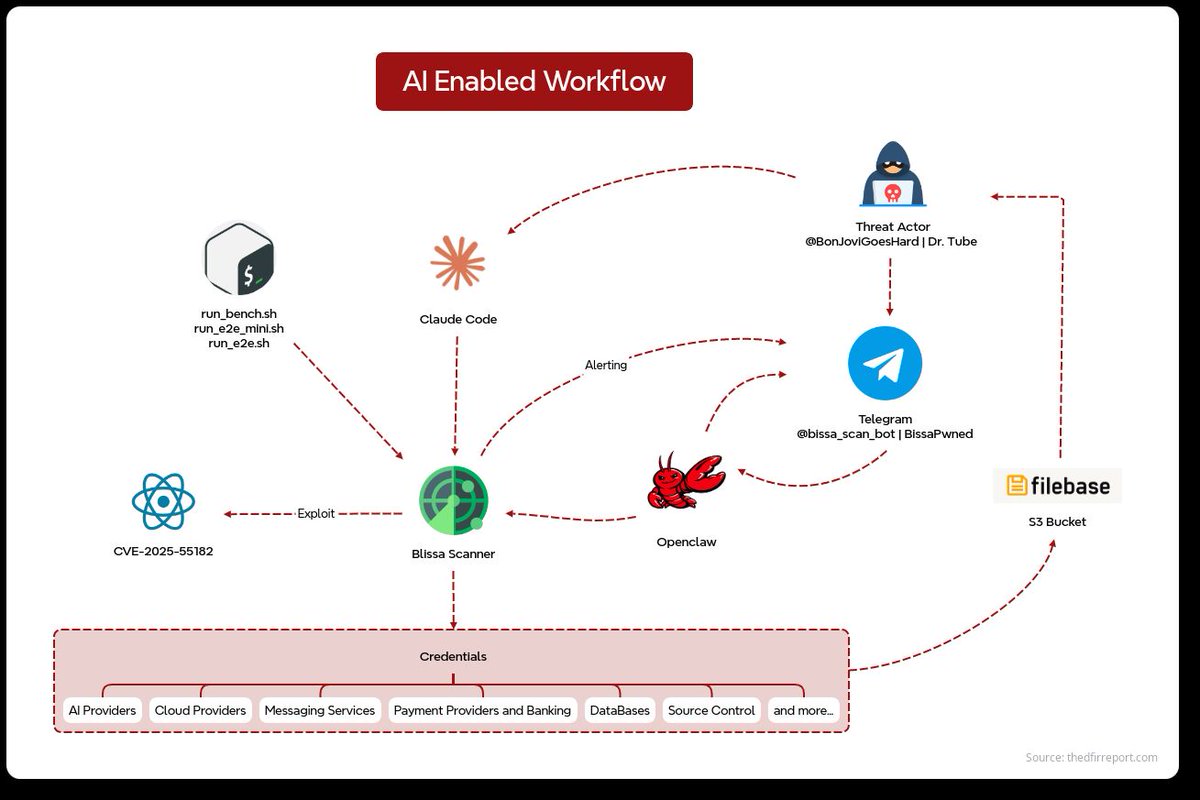
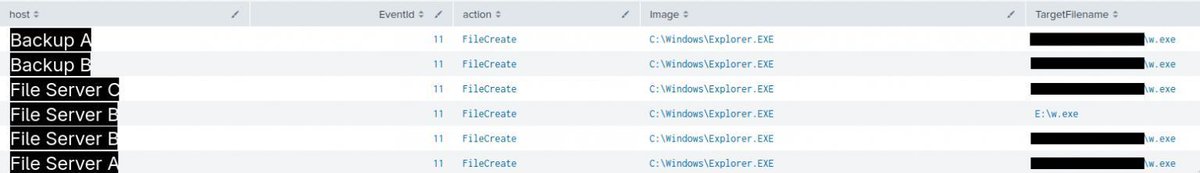
Real Intrusions by Real Attackers, the Truth Behind the Intrusion