@TwoSevenOneT But if you delete the symlink Windef doesn't know where to find its folder and doesn't work anymore 🫤
English
Utilisateur anonyme
8 posts





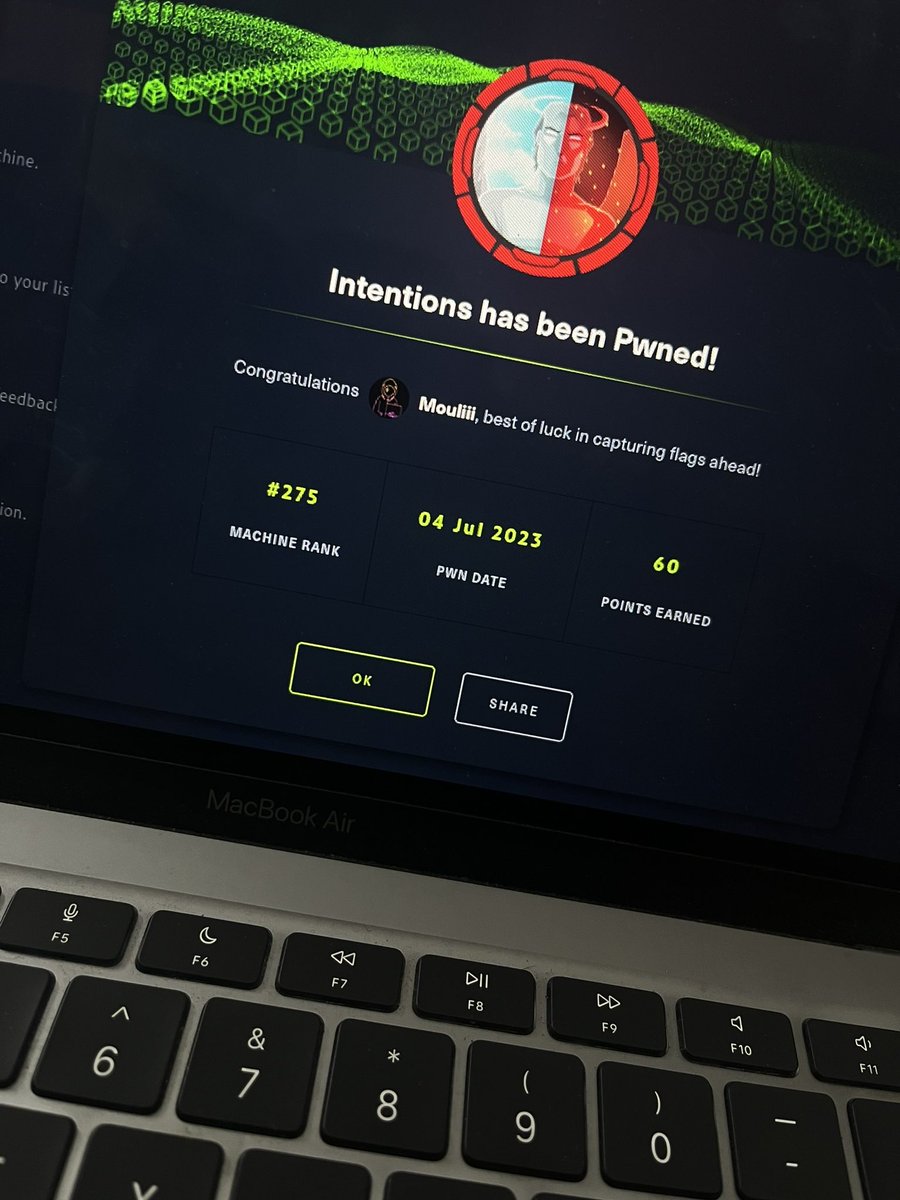



It's insane that Meterpreter + the Metasploit backend is a jawdroppingly complex piece of malware that many of us could (and do) learn so much from, but people call it shit because the default artifacts are sigged by Defender