David Schekaiban
28.7K posts


vocês sabiam???? se colocar uma pinha no banheiro, quando você estiver tomando banho ela vai fechar e quando o banheiro ficar seco, ela volta a abrir
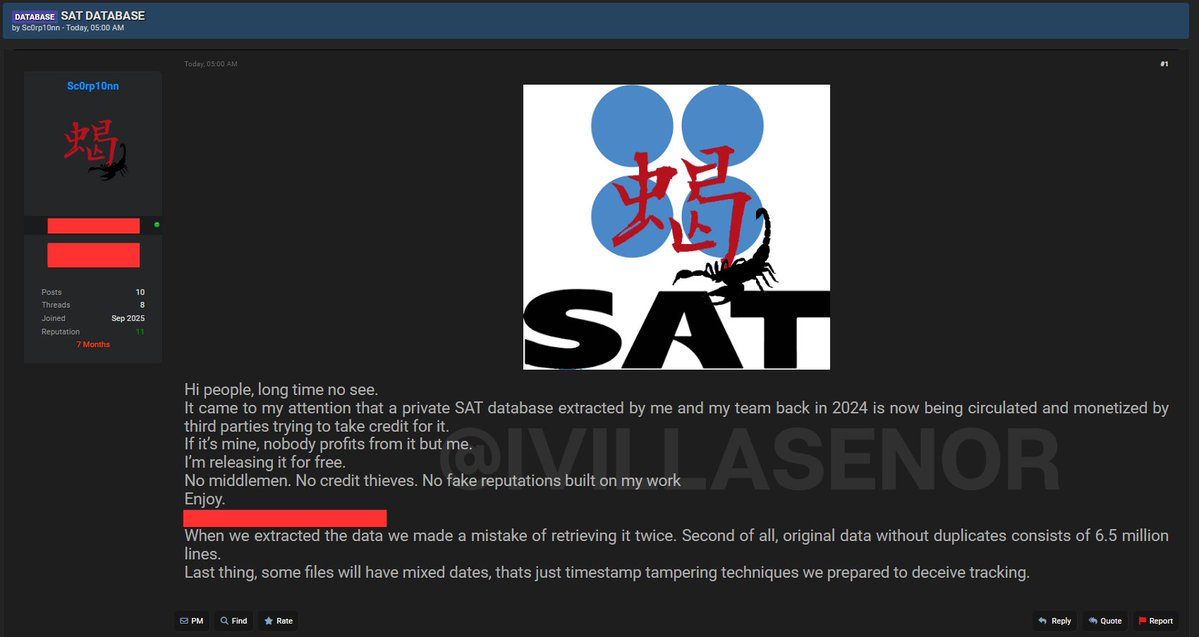
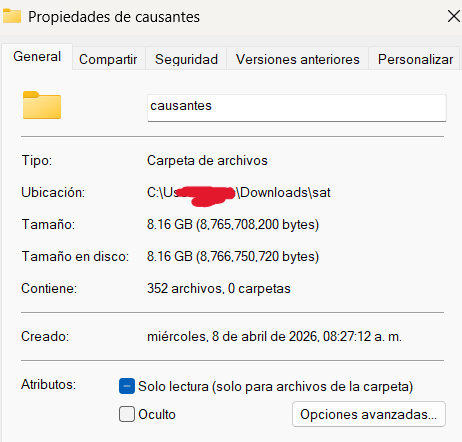
🚨 NATIONAL SECURITY ALERT: COMPROMISED FINANCIAL CORE (TREASURY OF NUEVO LEÓN - MEXICO) 🇲🇽 A critical, high-impact vulnerability has been detected targeting the Finance and Treasury Department of the State of Nuevo León. The threat actor, identified as Z3r00, claims to have "full access" to the state's financial core, exposing tax and transactional data of citizens and businesses. 👤 Threat Actor: Z3r00 🌍 Location: Nuevo León, Mexico 🇲🇽 📊 Exposure Volume: Approximately 53,000 financial records. 📑 Compromised Information (Highly Sensitive): Tax Identification: Full names and RFC (Federal Taxpayer Registry). Transactional Data: Digital tax receipts, bank authorization numbers, amounts paid, and tax amounts. Payroll Details: Company IDs, tax types (e.g., payroll tax), and municipalities of operation. Security: Electronic signatures (hashes) and internal control records. 🔍 Monitor: analyzer.vecert.io #CyberSecurity #Mexico #NuevoLeon #DataBreach #TesoreriaNL #SpeakTeam #InfoSec #VECERT #Ciberseguridad #SAT #RFC #Hacking
If this is real, it could be one of the largest data breaches in China’s history. A hacker group claims it extracted over 10 petabytes of data from a state-run supercomputing facility, widely believed by experts to be the National Supercomputing Center in Tianjin. This center supports thousands of clients, including research institutes, aerospace programs, and defense-linked organizations. What’s reportedly in the data: - Documents marked “secret” in Chinese - Missile and bomb schematics - Aerospace and aviation research - Bioinformatics and fusion simulation data - Files linked to major state entities like AVIC and COMAC Cybersecurity experts who reviewed sample data say it matches what you would expect from such a facility, though the full breach is not independently verified. Even more concerning: - The attacker claims access lasted months without detection - Sample datasets were posted online via Telegram - Full access is reportedly being sold for hundreds of thousands of dollars in crypto At this stage, the scale and origin are still being verified. But if even partially true, it points to a serious vulnerability in infrastructure tied to China’s scientific and defense ecosystem. If a centralized system like this can be penetrated, what does that say about the security of the data it was processing? #China #Cybersecurity #CCP #DataBreach #Geopolitics #Tech cnn.com/2026/04/08/chi…


Mexico Speeds Up Biometric ID Rollout reclaimthenet.org/mexico-speeds-…
🚨 CYBER THREAT ALERT: MASSIVE DATA LEAK AFFECTING PORT AND NAVAL PERSONNEL - MEXICO 🇲🇽 A massive data exfiltration has been detected originating from the *Puerto Inteligente Seguro* (Secure Intelligent Port) platform (puertointeligenteseguro.mx)—an integral system managed by the National Port System Administration (ASIPONA) under the supervision of the Secretariat of the Navy (MARINA). 👤 Threat Actor: marssepe (Private Society 157). 📍 Affected Entity: National Port System Administration (ASIPONA) / MARINA. 📊 Data Volume: +640,000 personnel records. 🌍 Scope: Logistics operators, port workers, and security personnel at strategic ports (e.g., Altamira). 🛠️ Data Nature: JSON (Access control API logs). 📦 COMPROMISED INFORMATION (PII & LOGISTICS): The leaked data structure is extremely detailed, enabling comprehensive profiling of individuals with access to restricted zones: 👤 Full Identity: Names, surnames, CURP, RFC, and Social Security Number (NSS). 🧬 Biographical Data: Gender, date of birth, and blood type. 📸 Biometric Data: Profile photos in Base64 format (digitized). 🏢 Employment Information: Company (e.g., *Almacenamiento y Logística Portuaria de Altamira*), employee ID, job title, operational area, and hierarchical level. 🚗 Licensing & Traffic: License numbers, categories, expiration dates, and medical examination details. 🛂 International Documentation: Passport numbers and their respective expiration dates. Monitor: analyzer.vecert.io #Cybersecurity #Mexico #Marina #PuertoInteligente #DataLeak #NationalSecurity #ASIPONA #VECERT #InfoSec #CyberAttack

CEO of 11x here, wanted to add some context. Security is something we take very seriously. For some quick background: we had a SOC 2 Type I through Vanta in 2024 with 3+ months of continuous monitoring before engaging Delve for our Type II later that year. The auditors used evidence from both platforms to satisfy the observation period. In our 2025 cycle, we had a full observation window and stand by our security posture and controls. We removed Delve's name because upon seeing these reports we are terminating our relationship with them and have since engaged Drata and are actively migrating.
🚨 INTELLIGENCE ALERT: Data Leak from the Attorney General's Office of the State of Tabasco (Mexico) 🇲🇽⚖️ Our Analyzer platform has detected an exfiltration of highly sensitive data affecting the Attorney General's Office of the State of Tabasco (FGE). The threat actor adrxx_Chronus has published what appears to be a compendium of asset declarations and personal data belonging to public servants. Victim: Attorney General's Office of the State of Tabasco (fgetabasco.gob.mx) 🏛️. Threat Actor: adrxx_Chronus 🎭. Volume: 21,504 individuals exposed (in PDF format). Date: March 28, 2026 🗓️. Analysis of Compromised Data The leak is exhaustive and compromises the total privacy of the officials involved and their families: 🔹 Personal and Professional Data: Names, home addresses, educational background, work experience, and contact details. 🔹 Financial Information: The declarant's net income, bank accounts, investments, debts, loans, and business holdings. 🔹 Assets: Real estate, vehicles, and movable property. 🔹 Family Details: Data regarding spouses/partners and financial dependents (including their income and assets). 🔹 Other: Private benefits, trusts, and public assistance received. Monitor: analyzer.vecert.io #CyberSecurity #Mexico #Tabasco #FGETabasco #DataBreach #Fiscalia #InfoSec #CyberAlert #HackingNews #NationalSecurity #PrivacyRisk #MexicoLeaks
Cuadra por cuadra... tardará un poco, pero quedará hermoso.


🇲🇽México → Lugar 76 de 116 en uso de IA per cápita → Índice de uso: 0.50x (usamos la mitad de lo esperado para nuestra población) → 9,757 conversaciones analizadas ¿En qué usamos IA los mexicanos? 1. Tareas escolares (6.6%) 2. Desarrollo web (3.9%) 3. Soporte técnico (3.6%) 4. Traducción (3.3%) 5. Software empresarial (3.3%) 6. Escritura creativa (2.8%) 7. Estrategia de negocios (2.8%) El uso #1 de IA en México son las tareas de la escuela, mientras EE.UU. la usa para construir empresas, Israel para innovar y Corea para automatizar industrias. No es que México no tenga talento, es que no estamos usando la herramienta más poderosa del siglo para lo que realmente importa. #country-usage" target="_blank" rel="nofollow noopener">anthropic.com/economic-index…





