𝖊𝖛𝖆𝖉𝖊 がリツイート
𝖊𝖛𝖆𝖉𝖊
191 posts



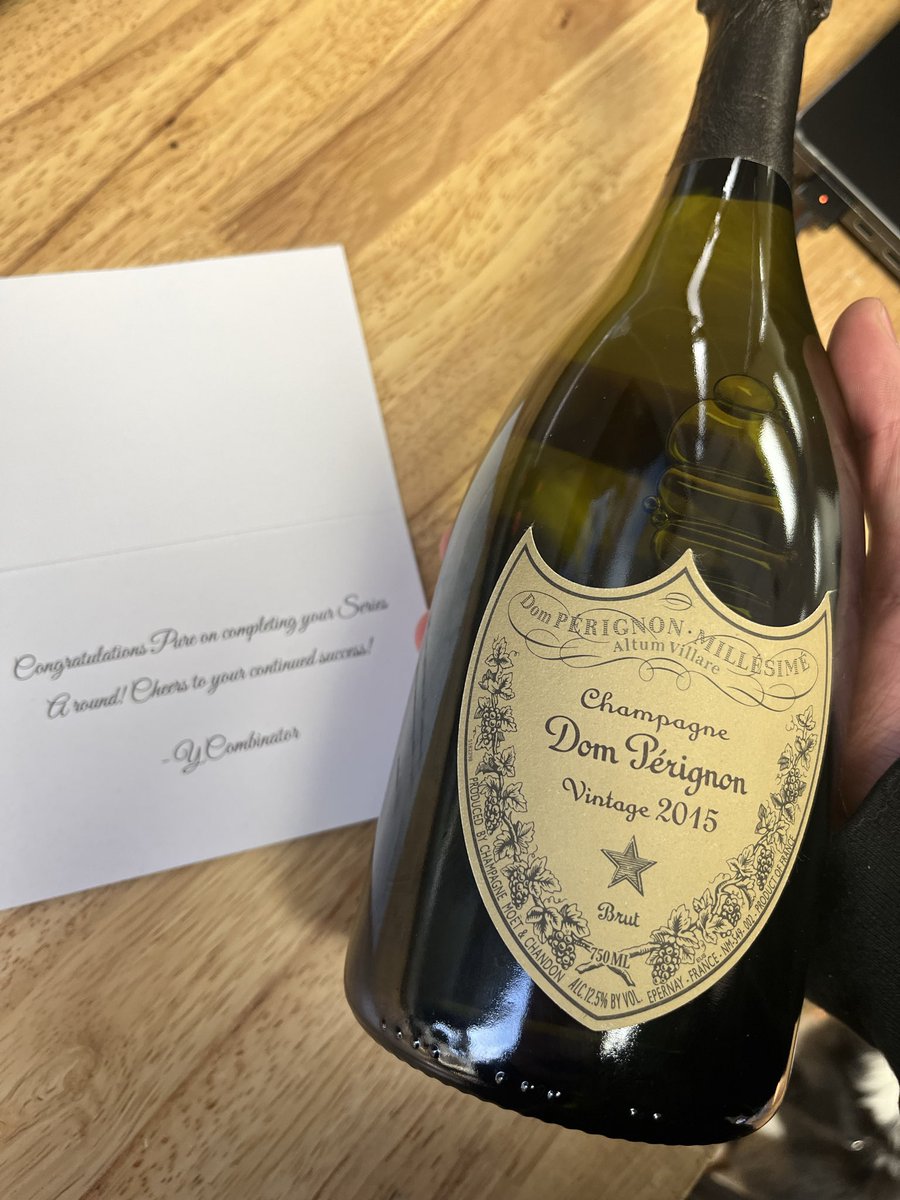
I guess I'm a coin trader now?
ty@tylermoz
Casual first few days of dogfooding buying Pokemon on Terminal
English
𝖊𝖛𝖆𝖉𝖊 がリツイート

@infosec_au @SLCyberSec @hash_kitten @assetnote Back in may I emailed their responsible disclosure email with a firewall bypass I found and I got a response a day later asking me to onboard to HackerOne so I can submit it but the bypass had been patched 🤣
English

@SLCyberSec @hash_kitten @assetnote This has been silently patched now 🫠 There's probably more WAF bypasses out there.
English

Vercel is questioning whether or not a WAF bypass is possible... Pushed an update that uses a payload from @SLCyberSec research team (specifically @hash_kitten). Payload has been running for @assetnote customers for last 18h. github.com/assetnote/reac… use --vercel-waf-bypass flag
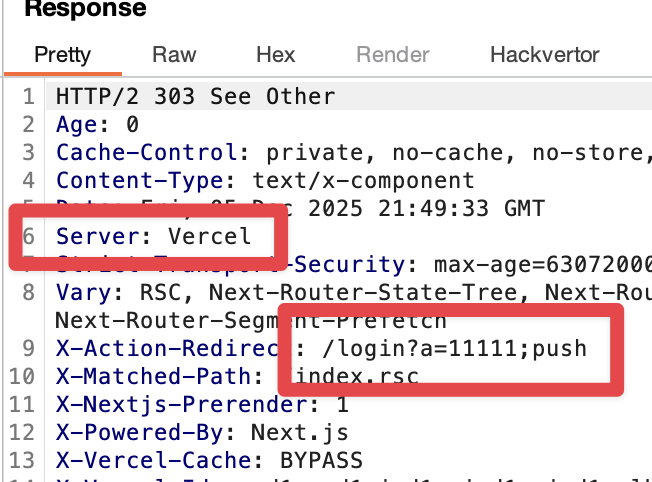
Guillermo Rauch@rauchg
@infosec_au @assetnote DM’d you. You have a working repro for bypassing Cloudflare but not Vercel. Would love to correct the record or see the evidence.
English

the other common entrepreneurial red pill is building sneaker bots
Troy Kirwin@tkexpress11
if I meet a founder ages 17-25 there is a 50% chance they cut their teeth running Minecraft servers at 10
English

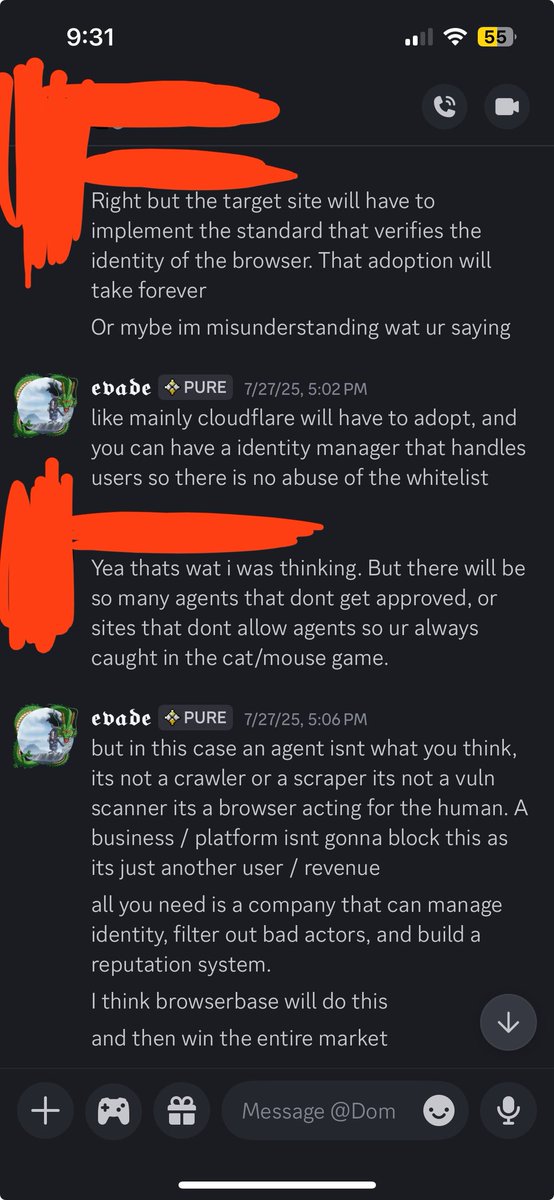
I think remote browsers still doesn't solve this problem. A layer needs to be built to prevent the agents from doing unprompted tasks local or remote, a stolen session is still a stolen session even if its not all of them. Aside from that companies like Cloudflare are trying to build prompt injections / a labyrinth to mess with agents which will waste compute and time. If something isn't built many people will bankrupt themselves getting reversed ddosed by cloudflare
English

@guohao_li @browserbase the difference with local vs remote browsers is that with remote browsers you have to explicitly give it those cookies or access
English

tl;dr: letting a model control your local browser is dangerous. anyone can prompt injection and steal your cookies.
you need a remote browser that’s isolated and intentionally given access. that’s why we’re building @browserbase
Anthropic@AnthropicAI
We’ve developed Claude for Chrome, where Claude works directly in your browser and takes actions on your behalf. We’re releasing it at first as a research preview to 1,000 users, so we can gather real-world insights on how it’s used.
English


@sleepy__dev any sneaker site could have done this and it'd be so hard to tell 😭
English

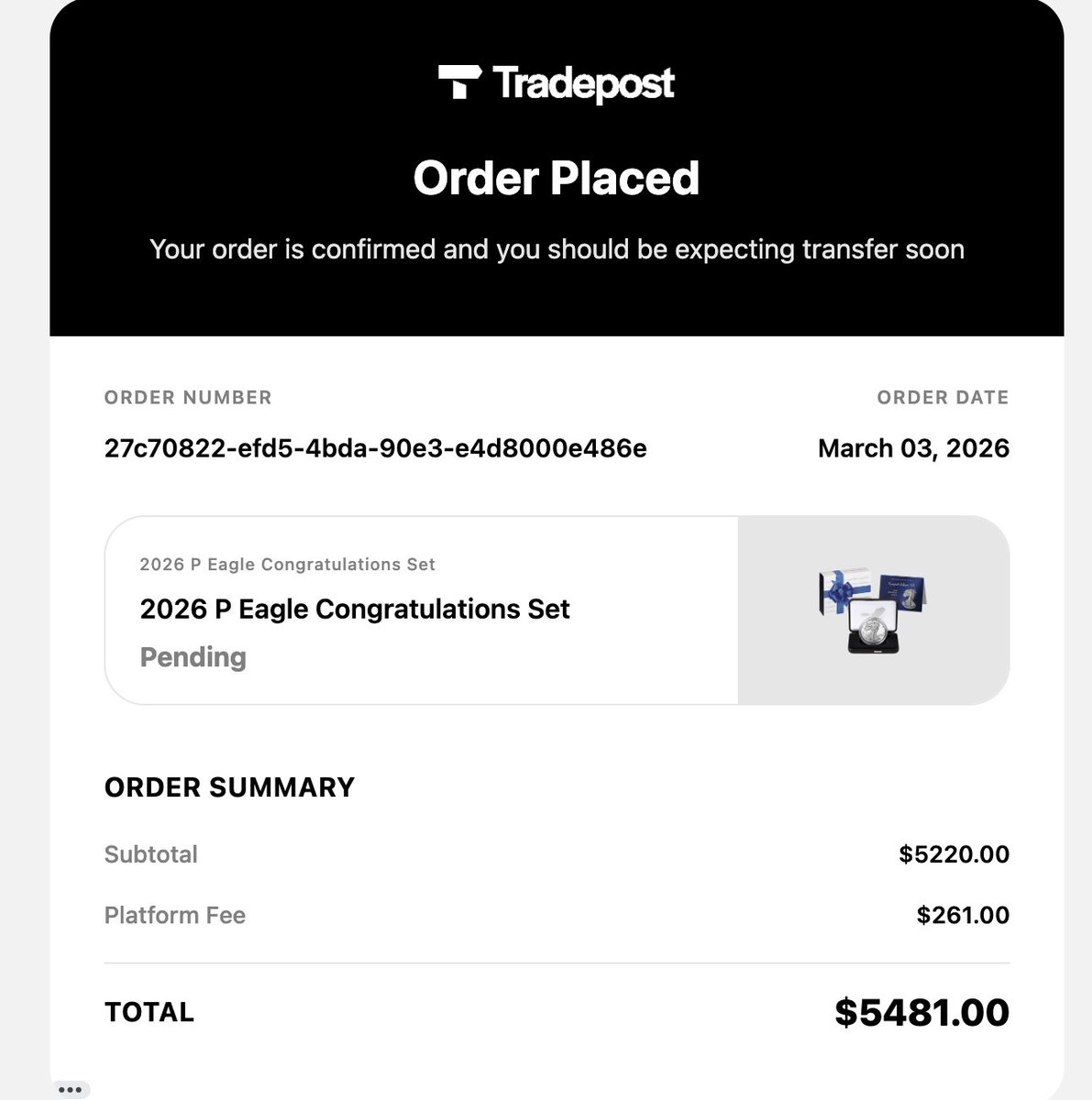
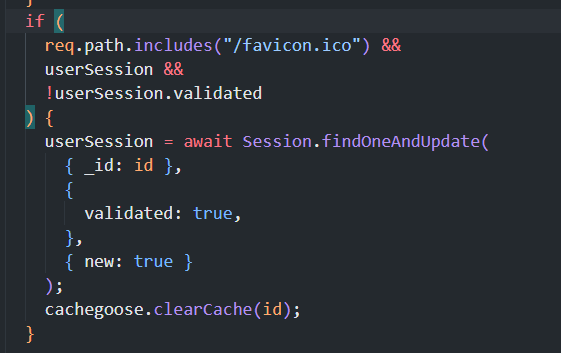
I was managing the queue for a big sneaker store in EU.
Wanted to share how I managed to block Cybersole from getting valid sessions.
I would simply check if the client ever requested the website favicon.ico file, no full request bot ever requests the favicon, also the session validity was never returned in any API endpoint, meaning they could never guessed if the session was valid.
Yes, this simple method worked, felt like sharing after a couple years because I still think to this day it is very funny.
English