Marcin
5.7K posts

Marcin
@marcinw
because tweeting and blogging is a full time job


When speaking with @aloria my spirits would lift. Her wit and brilliance were stuff of legend and she would often make me smile and think at the same time. You will be missed and this is how I will remember you:

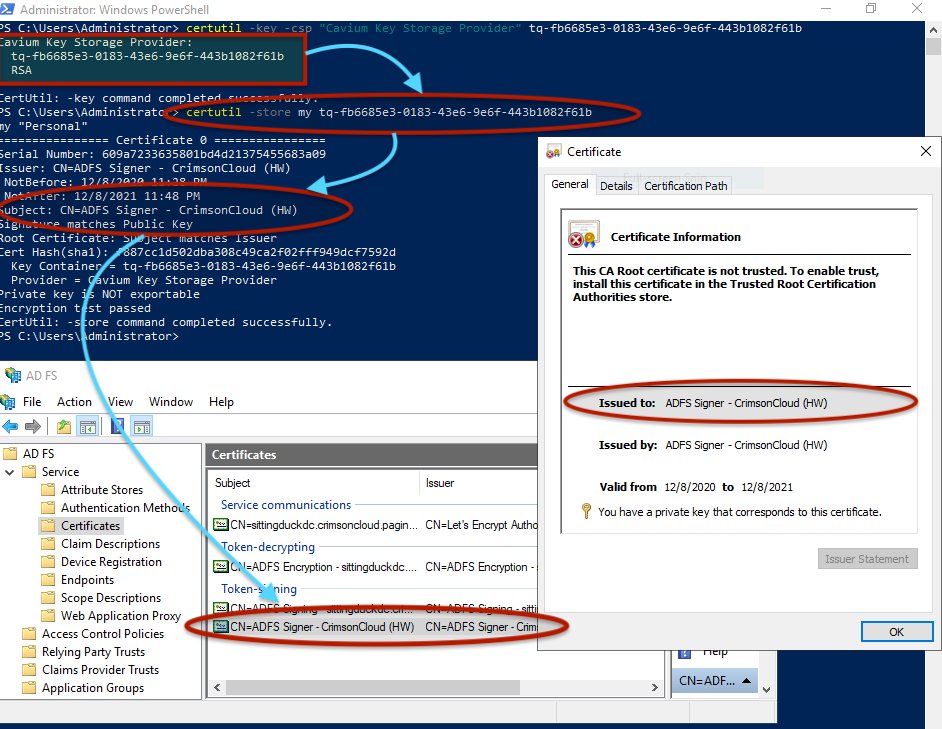
The Code Signing Working Group recently improved requirements for code signing. Effective Nov. 15, 2022, key protection requirements for OV code signing certificates are harmonized to be the same as EV code signing certificates. digicert.com/blog/improved-…





People may disagree with me on this, but allowing users to dtrace-log the hell out of their phones would at least help at-risk users collect better forensic evidence... iOS still has all the dtrace infra, android has all the eBPF infra. Allow users to add o11y to their phones.

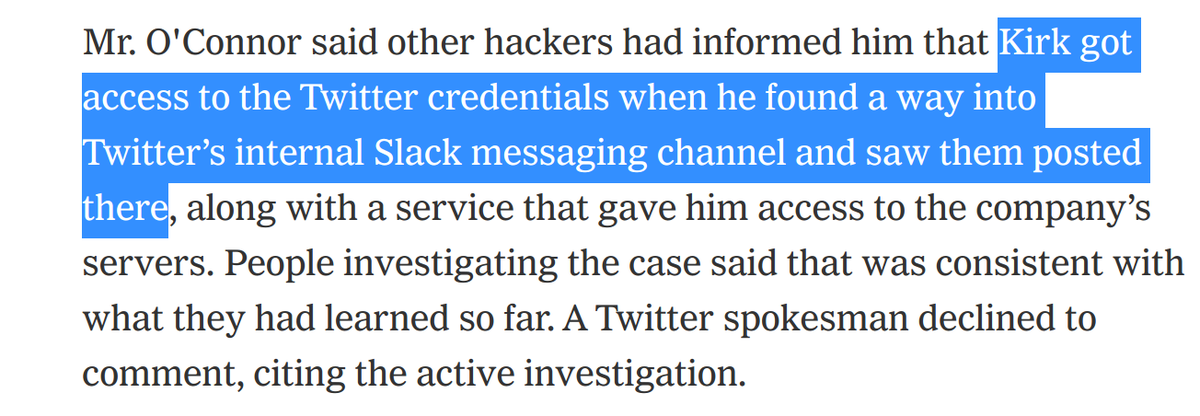
For years I’ve avoided anything to do with cryptocoins. Initially it was because people assumed being in security meant I knew about it & kept pestering me. Later it was because I saw the greed derail a couple of good hackers careers. Then it was some of the unpleasant community.





I once had dinner with @JacobTorrey in Amsterdam

Join an amazing team and work on interesting cryptography projects and research at the forefront of information security and privacy! linkedin.com/jobs/view/2181…
Periodic reminder that you should check out cryptopals.com if you’re involved in making or breaking software that uses cryptography