p0sql
38.6K posts


p0sql
@p0sql
Cloud Native & Infosec enthusiast in telco world. Let's break things ! Bike Life 🏍️ 🇲🇶 || Some cool stuff :: https://t.co/nhqotQKrrA


Mais donne nous les livres ou ftg , les békés de la Guadeloupe sorte de la Martinique pleure stv , c’est la vérité

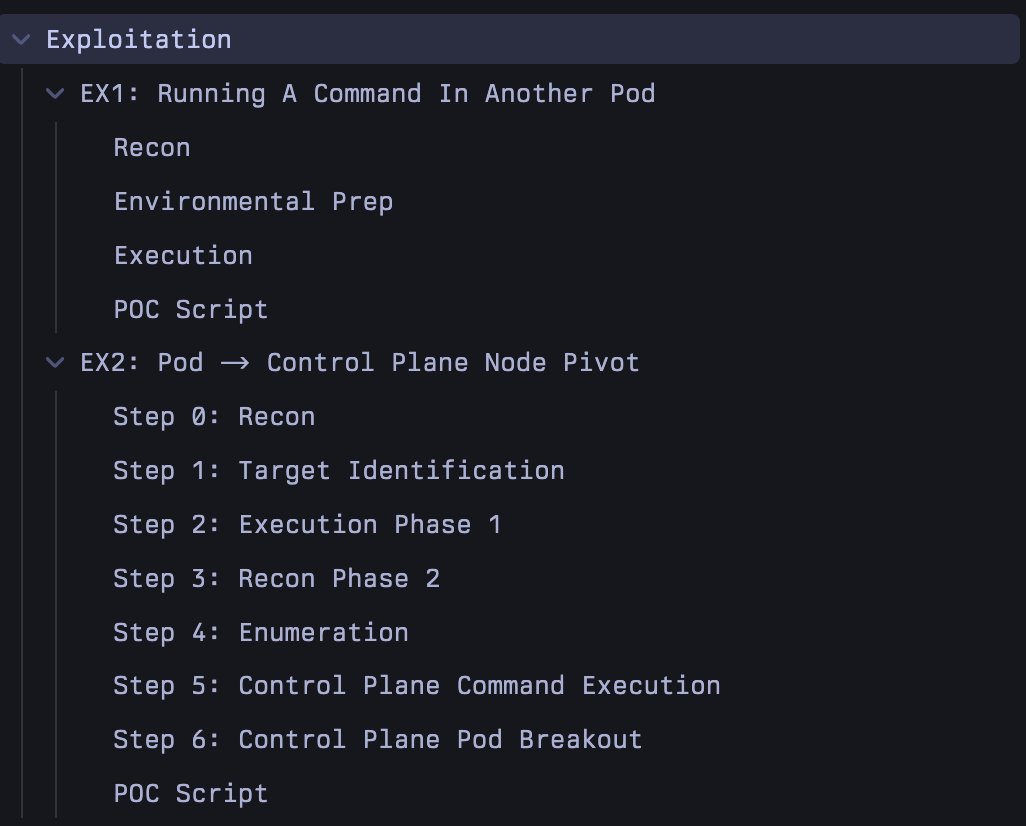
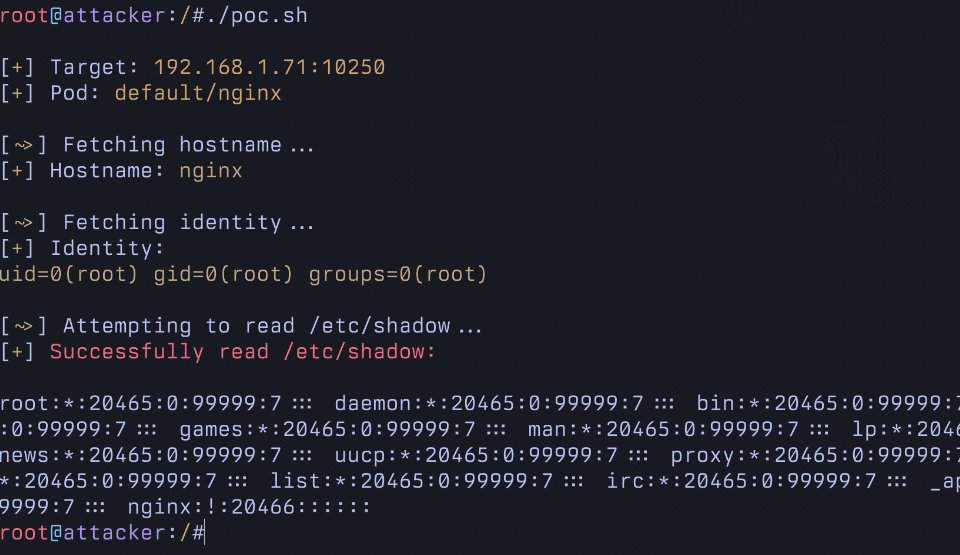
Excited to disclose my research allowing RCE in Kubernetes It allows running arbitrary commands in EVERY pod in a cluster using a commonly granted "read only" RBAC permission. This is not logged and and allows for trivial Pod breakout. Unfortunately, this will NOT be patched.




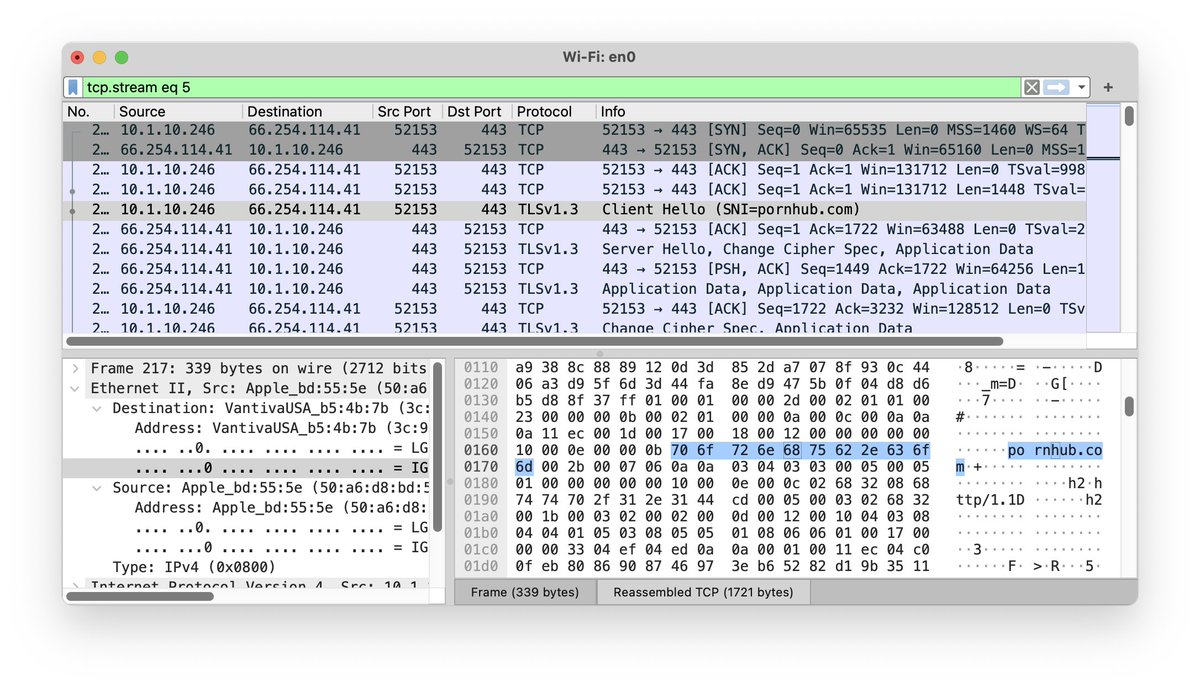

@BuckedUnicorn As an expert, then, I defer to you to show me how any of this is false on an ecrypted DNS channel like 1.1.1.1 that supports ECH. Maybe "expert" is too strong a word, then? Or perhaps a little knowledge is a dangerous thing.



First day at AWS, did a small update to the cable system and took my afternoon off