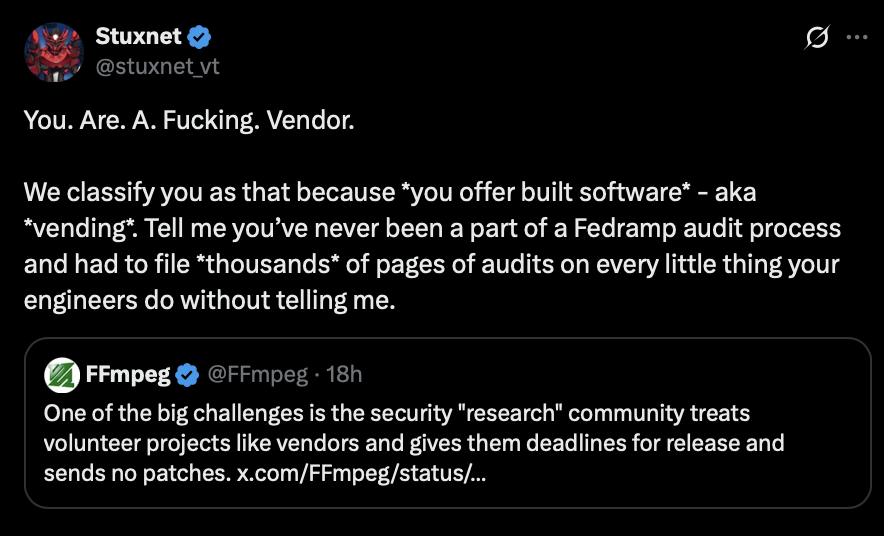
固定されたツイート

Bang on Iain! As much as the example in the blog post works, getting c2 over any form of filesystem, is the real gem here.
Even locally for privesc, get a system shell without worrying about proxies for example.
Looking forward to see what folk come up with use case wise.
@[email protected]@strawp
This is such a cool C2 channel technique. Use network file share, RDP mapped drives and anywhere else more than one host sees the same filesystem as a C2 channel which really doesn't get logged. Simple but effective!
English