stasi
53 posts


stasi
@sta5i
ministry of state security - Staatssicherheit email: stasi(at)tfwno(dot)gf - new delhi.
参加日 Nisan 2025
129 フォロー中12 フォロワー

Full write-up with YARA rules, MITRE ATT&CK mapping, complete 79-domain IOC list, and all recovered payload source:
intel.breakglass.tech/post/kimsuky-c…
Prior art: @AaboreSec documented bootservice.php endpoint names in 2024. @huntaboratory documented "Million OK" in Dec 2024. This is the first public recovery of the full payload source code.
Reply or DM if you've published on this cluster — we'll credit.
#Kimsuky #APT43 #DPRK #ThreatIntel
English

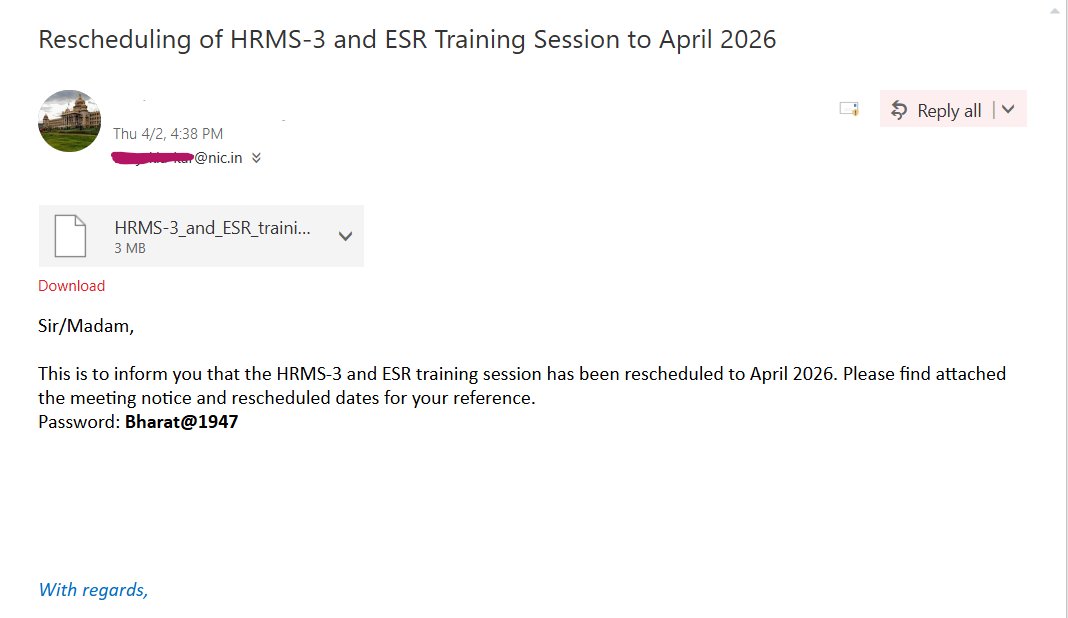
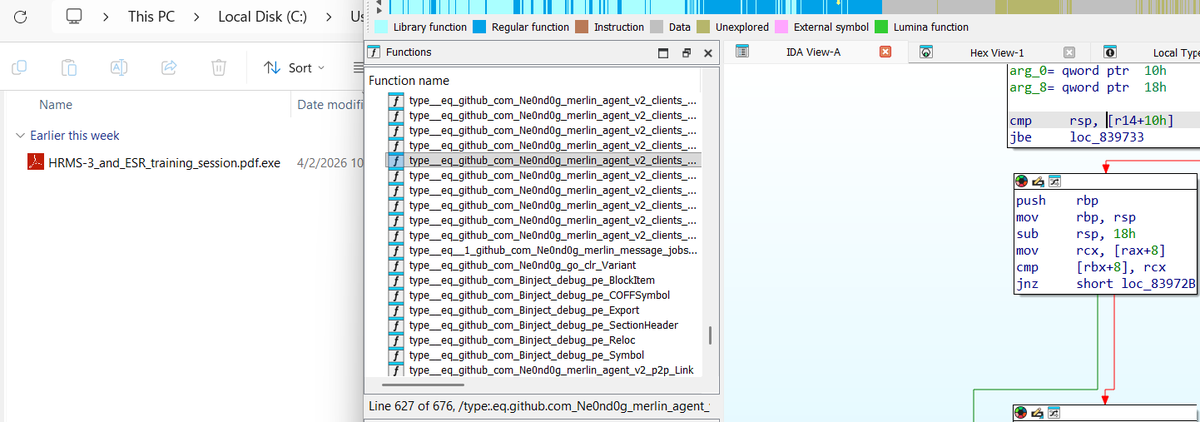
Tracking a live infection of Karnataka State of Govt. of India, attackers are spreading Golang based Merlin agent.
C2 address is port forwarded:
lasafem240-61062.portmap.host:61062/data
virustotal.com/gui/file/e63d6…
English

github.com/Hulett77/VALOR…
another Luajit malware distributing through github repo poisoining
English

github.com/Buvan7-glitch/…
Found another LuaJit based malware (smartloader)
impersonating GhostVEH project.
English

github.com/Stendrmatm
This user on github is suspicious, poisoning repo to come on top of search result like Stendrmatm/Muck-Stealer. nothing suspicious found in the repos yet.
cc: @RussianPanda9xx
English

@LeighGi66657535 but that is for development. how do i go to hunt for vulnerable programs, and look for exploitative path. I should learn binary exploitation, and fuzzing ?
English

@LeighGi66657535 I am well versed in x86/x64 assembly, c language and windows internals.
English

@LeighGi66657535 @uwu_underground @hasherezade I have seen many of yours posts, and always wonder if someone living in different part of the world could watch them.
English

Chat, I've done it.
I've managed to get Windows Sockets (Winsock) functionality working by communicating directly with AFD (Ancillary Function Driver for WinSock) by IO control codes AND used it with HTTPS by using SSPI (Microsoft Security Support Provider Interface).
By doing this, this completely eliminates the need for WININET or WINHTTP for malware payloads. It also removes the weird telemetry and ETW stuff present in Winsocks, WININET, and WINHTTP.
My code is still in a debug state at the moment, but I'll eventually release a non-fucked-up version (no SYSCALLs, no position independence) so people can look at it, study it, or review it.
Currently this is only supports GET requests for simple pages (not even file downloads...). However, I'm having so much fun with this I think I am going to expand on it to do the following:
- HTTPS authentication
- HTTPS upload
- HTTPS download
- ???
I'll make it all open source, non-crazy, in a format people can copy pasta and have fun with it. I'll also probably make a fork where it's the crazy schizo version.
I hope all my malware development friends, reverse engineer friends, and anime friends, look at it and appreciate it. This is some of my favorite code I've written and I think it has a lot of applicability to Red team engagement. Conversely, it also offers insight to defenders on detecting this sort of functionality.

English

@sta5i when its done i will replace the real calc with my patched calc on the target machine.
English

I patched the github.com/microsoft/calc… with a runpe loader over http without writing to disk rootkit. w00t w00t

English

I had this idea to do HTTPS stuff in C using the Windows Sockets API (Winsocks).
I did it. I got it working. I was able to verify an SSL cert, do a GET, do a POST octet binary stream thingy to upload a simple file (unironically testing using a picture of a cat).
After I got it working I decided to do what I always do: make it more malware like.
I decided I wanted to poke Windows with a stick, make the code position independent, and make it function as close to the metal as possible.
What happened next cannot be described as a "rabbit hole". I have fallen into an infinite abyss, a fucking Windows internals chasm. I am looking at things in Windows I have never looked at before. I am scared, confused, intrigued, ... but mostly confused (and lost).
ReactOS, x86matthew, some weird French Guy (can't remember his name), and random nerds on OSR, have done unholy work and really dug into it. They deserve a lot of credit for walking knee deep in Windows sludge.
English